How to read dmp files – Kicking off with how to read DMP files effectively, this opening paragraph is designed to provide a comprehensive overview of the process from start to finish. DMP files can be quite complex, often resulting in a multitude of questions and concerns. Therefore, breaking down the process into manageable pieces will make it easier to understand and ultimately read these files.
The process begins by understanding the format of DMP files, including their binary composition and file organization. This information can be found within the header, metadata, and data sections. Furthermore, users can rely on built-in tools, as well as third-party software, to read and analyze DMP files.
Understanding the Format of DMP Files
DMP (Digital Measurement Protocol) files are widely used in the field of digital analytics and data collection. Despite their widespread adoption, the internal format and organization of these files can be complex and difficult to navigate. In this section, we will delve into the structure of DMP files, discussing their binary composition, file organization, and how different software applications interpret and handle the various components of these files.
Binary Composition and File Organization
DMP files are binary files that contain a series of structures representing data fields, headers, and metadata. The format is typically comprised of a sequence of blocks, each representing different aspects of the file. Understanding the structure and organization of these blocks is essential for working effectively with DMP files.
- Data Sections: These sections represent the actual data collected from various sources, such as user interactions, page views, or other events. Data sections are usually divided into blocks containing specific types of data, such as timestamps, user IDs, or event types.
- Headers and Metadata: The header section provides vital information about the file, including its structure, version, and other relevant metadata. This information is crucial for processing and interpreting the data within the file.
- Footer: The footer section typically includes error correction information, integrity checks, or other validation data.
Significance of Headers, Metadata, and Data Sections
The headers and metadata in a DMP file play a crucial role in determining how it will be processed and interpreted by different software applications. They provide essential information about the structure and content of the file, ensuring that data is accurately extracted, processed, and stored.
“Metadata is like a book’s table of contents – it helps you understand the structure and content of the data and navigate it effectively.”
Here’s an example of how a software application might interpret the various components of a DMP file:
* Data: The software application identifies the data sections within the file and extracts relevant information about user interactions, page views, or other events.
* Headers and Metadata: The application uses this information to validate and interpret the data within the file, ensuring that it is properly formatted and organized.
* Footer: The application verifies and validates the integrity and error correction data in the footer, ensuring that the file is complete and accurate.
Different Software Applications and Their Handling of DMP Files
Different software applications handle and interpret the various components of DMP files in different ways, depending on their architecture and purpose. However, most applications rely on the headers, metadata, and data sections to determine how to process the file.
For instance, marketing analytics software may focus on extracting data related to user behavior, while data integration software might prioritize metadata information for data standardization and mapping.
Software and Libraries for Working with DMP Files
Several software libraries and applications make working with DMP files more accessible by providing pre-built functions and tools for parsing, interpreting, and integrating the data within these files.
Some examples include:
- DMP SDK: A software development kit (SDK) that enables developers to build custom applications for working with DMP files.
- Open-source DMP Parser: An open-source library that provides pre-built functions for parsing and interpreting DMP files.
- Digital measurement protocol reader: A command-line tool for reading and extracting data from DMP files.
The use of such libraries and software significantly simplifies the process of working with DMP files and enhances the efficiency and accuracy of data analysis.
Using Third-Party Software for DMP File Reading
When it comes to reading and analyzing DMP files, there are various third-party software tools available that can enhance your workflow and provide more flexibility compared to native software. One of the primary motivations to use third-party software tools for DMP file reading is to benefit from their additional features and functionality that may not be available in built-in tools.
Available Third-Party Software Tools for DMP File Reading
There are numerous third-party software tools specifically designed for reading and analyzing DMP files. Some of these tools include:
- Dump Explorer – A free, cross-platform tool for reading and exploring DMP files.
- DebugDiag – A troubleshooting and diagnostic tool that also includes a DMP file viewer.
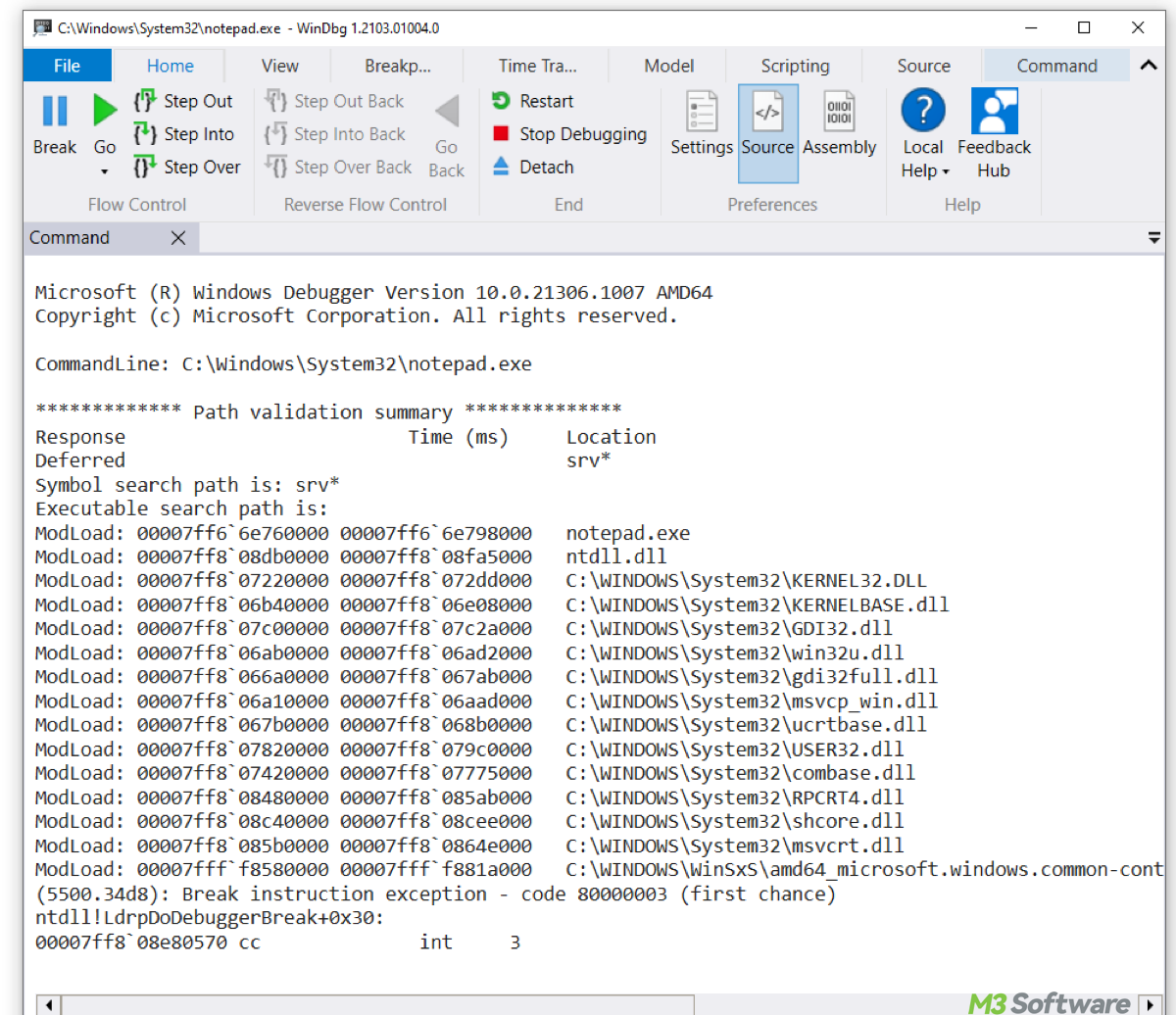
- WinDbg – A debugging tool from Microsoft that includes a DMP file viewer and analyzer.
- ProcMon – A system monitoring tool that includes a DMP file viewer for analyzing process execution.
Advantages of Using Third-Party Software Tools, How to read dmp files
Using third-party software tools for DMP file reading offers several advantages, including:
- Enhanced functionality – Third-party tools often include additional features and functionalities that are not available in native software.
- Increased flexibility – Third-party tools can provide more flexibility in terms of data analysis and troubleshooting.
- Improved user experience – Some third-party tools are designed with a more user-friendly interface that can make it easier to read and analyze DMP files.
- Cost-effectiveness – Some third-party tools are available for free, while others offer a free trial or low-cost subscription options.
Comparison of Third-Party Software Tools
While all the third-party software tools mentioned offer advanced features and functionality for reading and analyzing DMP files, each tool has its unique strengths and weaknesses. The choice of which tool to use ultimately depends on your specific needs and requirements.
- Dump Explorer is a lightweight and free tool that is easy to use and navigate.
- DebugDiag is a more comprehensive tool that includes advanced troubleshooting and diagnostic features.
- WinDbg is a powerful debugging tool that includes a DMP file viewer and analyzer, but may require more technical expertise to use.
- ProcMon is a system monitoring tool that includes a DMP file viewer for analyzing process execution, but may require more technical expertise to use.
Selecting and Installing Suitable Third-Party Software
When selecting and installing suitable third-party software for reading and analyzing DMP files, consider the following steps:
- Identify your specific needs and requirements.
- Research and evaluate different third-party software tools.
- Read reviews and check compatibility with your system.
- Download and install the chosen tool.
By following these steps and considering the advantages of using third-party software tools, you can select the best tool for your specific needs and improve your workflow when reading and analyzing DMP files.
• Cross-checking the data with external sources to verify its accuracy
• Using data validation tools to identify inconsistencies and errors
• Creating data quality metrics to track and monitor the accuracy of the extracted data
Handling Large and Complex DMP Files
DMP files, containing valuable data, can grow in size and complexity as the number of events or user interactions increases, posing significant challenges. The sheer volume and intricacy of large DMP files can overwhelm systems, hindering performance, and imposing storage constraints. This situation demands strategic approaches for efficient management and processing, ensuring seamless analysis and insights.
Data Partitioning Strategies
Effective data partitioning involves dividing large DMP files into smaller, more manageable chunks, enabling parallel processing and reducing the burden on systems. By doing so, users can distribute the workload across multiple processing units, significantly enhancing overall performance and scalability. To achieve this, data partitioning techniques can be employed, such as:
- Timestamp-based partitioning, where data is split based on timestamp intervals, allowing for efficient processing of historical data.
- User-defined partitioning, where data is divided based on specific user-defined criteria, such as user ID or event type.
- Random partitioning, where data is randomly split into partitions, ensuring even distribution and preventing bias.
Each method offers unique benefits and trade-offs, requiring careful consideration based on the specific requirements of the data and processing needs.
Distributed Processing and Cloud Computing
In addition to data partitioning, distributed processing and cloud computing provide scalable solutions for handling large DMP files. By leveraging cloud resources, users can offload computational tasks, reducing on-premises infrastructure requirements and mitigating performance bottlenecks. Cloud-based services, such as Amazon Web Services (AWS) and Microsoft Azure, offer scalable computing power, storage, and specialized services like Hadoop and Spark, enabling efficient processing and analysis of large DMP files.
Designing Scalable Solutions
To ensure efficient and scalable DMP file analysis, users must design and implement solutions tailored to their specific needs. A well-planned strategy involves considering factors such as data volume, processing requirements, storage constraints, and scalability needs. By employing scalable architectures, such as microservices or containerized applications, users can easily adapt to changing requirements and accommodate growing data volumes, ensuring seamless processing and analysis of large DMP files.
Ensuring Data Security and Integrity
When working with sensitive DMP files, it’s crucial to prioritize data security and integrity to prevent potential data breaches or corruption. Ensuring the confidentiality, integrity, and availability of your data is vital, especially when handling large and complex data sets. In this section, we’ll discuss measures to protect against potential data breaches or corruption, as well as robust data backup and archival procedures to maintain data integrity.
Protecting Data with Encryption and Checksum Verification
Data encryption is a robust method of protecting sensitive information from unauthorized access. It works by converting plaintext data into unreadable ciphertext, making it virtually impossible for hackers to intercept and exploit your data. Regular checksum verification is also essential in ensuring data integrity. This involves generating and validating digital fingerprints (checksums) for your data, allowing you to detect even the slightest changes or corruption.
“Data encryption is like locking your door. Checksum verification is like checking if the door is locked and unlocked at the right time.
- Password-based encryption (PBE) uses a password to encrypt and decrypt data. It’s an effective method, but it’s essential to use strong, unique passwords and store them securely.
- Key-based encryption uses a secret key to encrypt and decrypt data. It’s a more secure method than PBE, but it requires more administrative effort to manage keys.
- End-to-end (E2E) encryption ensures that data is encrypted on the sender’s device and decrypted on the recipient’s device. It’s an ideal method for sensitive data, like financial information.
Robust Data Backup and Archival Procedures
Regular backups and archival procedures are essential to maintain data integrity. This ensures that your data is recovered in case of data loss or system failure. Implementing a robust data backup and archival strategy involves:
- Scheduling regular backups of critical data, like DMP files.
- Using redundant storage solutions, like RAID or disk arrays, to ensure data availability.
- Verifying data restores to ensure backups are reliable.
Data Security Protocols Comparison
When evaluating data security protocols, consider the following factors:
- Key exchange algorithms: Look for secure algorithms like Diffie-Hellman (DH) or elliptic curve cryptography (ECC).
- Authentication methods: Choose secure authentication methods like public-key authentication or biometric authentication.
- Access control: Ensure that access control mechanisms, like access control lists (ACL) or role-based access control (RBAC), are in place to restrict unauthorized access.
- Encryption standards: Opt for industry-standard encryption protocols like Advanced Encryption Standard (AES) or Transport Layer Security (TLS).
Implementing Data Security Measures
To ensure data security and integrity, follow these best practices:
- Implement a secure data destruction policy to erase sensitive data when it’s no longer required.
- Restrict access to sensitive data using secure authentication methods.
- Regularly update and patch software and systems to address security vulnerabilities.
- Monitor data for unauthorized access or tampering.
Collaborative Analysis and Data Sharing: How To Read Dmp Files
Collaborative analysis and data sharing are crucial components of successful data management plan (DMP) file analysis. By working together, researchers and data analysts can pool their expertise, share resources, and achieve more meaningful insights than they could alone. In this section, we’ll explore the benefits of collaborative analysis and data sharing, introduce tools and platforms that facilitate seamless data exchange and collaborative work, and explain how to establish clear data management and governance procedures for shared DMP files.
Benefits of Collaborative Analysis and Data Sharing
Collaborative analysis and data sharing offer several benefits, including:
- Improved data quality and accuracy: By combining the efforts of multiple researchers, you can identify and correct errors, and ensure that the data is comprehensive and consistent.
- Increased efficiency: Collaborative analysis can help reduce the time and effort required to analyze large datasets, allowing researchers to focus on more complex and meaningful tasks.
- Enhanced creativity and innovation: Collaborative analysis can lead to the development of new methods and approaches, and the sharing of knowledge and expertise can foster a culture of innovation and creativity.
- Better decision-making: By combining the insights and expertise of multiple researchers, you can make more informed decisions, and develop more effective solutions to complex problems.
Tools and Platforms for Collaborative Analysis and Data Sharing
Several tools and platforms facilitate collaborative analysis and data sharing, including:
- Data sharing platforms: Platforms such as SHARE and Dataverse provide a secure and accessible environment for researchers to share their data and collaborate on analyses.
- Collaborative analysis tools: Tools such as Jupyter Notebook and Google Colab provide a shared environment for collaborative analysis, where researchers can work together on projects and share their findings.
- Data visualization tools: Tools such as Tableau and Power BI provide a shared environment for data visualization, where researchers can work together to create interactive and dynamic visualizations.
Establishing Clear Data Management and Governance Procedures
To ensure the success of collaborative analysis and data sharing, it’s essential to establish clear data management and governance procedures. This includes:
- Defining roles and responsibilities: Clearly define the roles and responsibilities of each researcher involved in the collaboration, and ensure that they understand their obligations and responsibilities.
- Establishing data sharing protocols: Establish clear protocols for data sharing, including the formats and frequencies of data exchanges, and the security and privacy measures that will be implemented.
- Developing data quality control procedures: Develop procedures for ensuring data quality, including data validation, data cleaning, and data documentation.
- Providing data governance and auditing: Establish procedures for data governance and auditing, including regular checks on data consistency, accuracy, and completeness.
Examples of Successful Collaborative DMP Analysis Projects
Successful collaborative DMP analysis projects can be seen in various fields, such as:
- Climate science: The Climate Data Initiative, a collaborative effort between researchers and data analysts, has provided crucial insights into climate change, and has helped inform policy decisions.
- Genetics: The 1000 Genomes Project, a collaborative effort between researchers and data analysts, has provided a comprehensive map of human genetic variation, and has helped identify new genetic associations with disease.
- Public health: The Global Health Data Platform, a collaborative effort between researchers and data analysts, has provided crucial insights into global health trends and outcomes, and has helped inform policy decisions.
Conclusive Thoughts
The journey to reading DMP files comes to an end, but the knowledge and understanding gained will remain long after. Reading these files has its advantages, which include the ability to extract specific data and perform large-scale analyses. It is also crucial to ensure data security and integrity throughout the process.
Collaborative analysis and data sharing play a significant role in the DMP file analysis process, enabling seamless data exchange and productive work among team members.
Helpful Answers
What is the primary purpose of DMP files?
DMP files are used to store and transfer digital measurement protocol data, which includes information about user interactions, click-through rates, and conversion rates, among other metrics.
Can I read DMP files using built-in tools?
Yes, many software applications and operating systems come with built-in tools to read and analyze DMP files. However, the capabilities of these tools may be limited compared to third-party software.
How do I choose the right third-party software to read DMP files?
When selecting third-party software, consider the specific needs of your project, such as functionality, compatibility, and price. Research the features and limitations of each software option and read reviews from other users to make an informed decision.