How to Turn on Secure Boot takes center stage as a crucial step in ensuring laptop and computer security, and its impact on system performance cannot be overstated. By preventing malicious firmware from tampering with the system’s boot process, Secure Boot plays a vital role in protecting sensitive data and maintaining system integrity.
In today’s digital landscape, Secure Boot has become an essential feature in computer systems, and its implementation varies across different hardware platforms. In this comprehensive guide, we will walk you through the process of enabling Secure Boot on your computer, creating a secure boot key, and exploring its benefits in protecting your data.
Understanding the Purpose of Secure Boot
Secure Boot is a crucial feature that ensures the security and integrity of your laptop or computer’s operating system. It acts as a safeguard against malicious software and unauthorized access to your system, thereby preventing various types of malware and threats from wreaking havoc on your device.
At the core, Secure Boot ensures that only trusted software can run on your device’s operating system. This is achieved by verifying the digital signature of the boot loader and the operating system kernel, thereby preventing any tampering or unauthorized updates. Secure Boot is especially important in today’s digital landscape, where malware and other types of threats are becoming increasingly sophisticated and difficult to detect.
The Types of Malware Prevented by Secure Boot
Secure Boot helps to prevent various types of malware, including rootkits, bootkits, and ransomware. These types of malware are designed to target the boot process, thereby gaining unauthorized access to your system.
- Rootkits are malicious software that hide themselves from the operating system, making them difficult to detect. They can be used to steal sensitive information, spy on users, or even take control of the system.
- Bootkits, on the other hand, infect the boot process, allowing them to load before the operating system is started. This gives them full access to the system, enabling them to steal data, install spyware, or even hold the system for ransom.
- Ransomware is a type of malware that encrypts the user’s data and demands a ransom in exchange for the decryption key. Secure Boot can prevent ransomware from running by verifying the digital signature of the operating system and boot loader.
These types of malware are particularly difficult to detect and remove, as they often target the root of the operating system, making them difficult to remove without completely reinstalling the operating system.
Secure Boot as a Hardware-Level Security Feature
Secure Boot is a hardware-level security feature that ensures the security and integrity of the boot process. It is implemented at the firmware level, making it difficult for malware to bypass or tamper with. Secure Boot is a key component of UEFI (Unified Extensible Firmware Interface) firmware, which provides a layer of security between the operating system and the firmware.
Secure Boot is a critical component of secure firmware, and its implementation on various computer systems has been a key factor in preventing malware attacks. Secure Boot is implemented on various computer systems, including laptops, desktops, and even servers, providing a robust layer of security against malware and other types of threats.
Preparing Your Computer for Secure Boot
To enable secure boot on your computer, you’ll need to configure your BIOS settings correctly. This involves checking if your computer’s BIOS supports secure boot and making the necessary adjustments. Additionally, creating a bootable USB drive is an essential step in preparing your computer for secure boot.
Checking if Your Computer’s BIOS Supports Secure Boot
Your computer’s BIOS must support secure boot for the feature to work. Check your BIOS settings to see if secure boot is supported. If you’re unsure how to access the BIOS settings, check your computer’s documentation or search for instructions online. If secure boot is not supported, you may need to purchase an update or a new motherboard to enable the feature. To check, you can follow these steps:
- Restart your computer and enter the BIOS settings by pressing the F2, F12, or Del key.
- Look for the “Secure Boot” option in the BIOS settings.
- Check if the option is enabled or disabled.
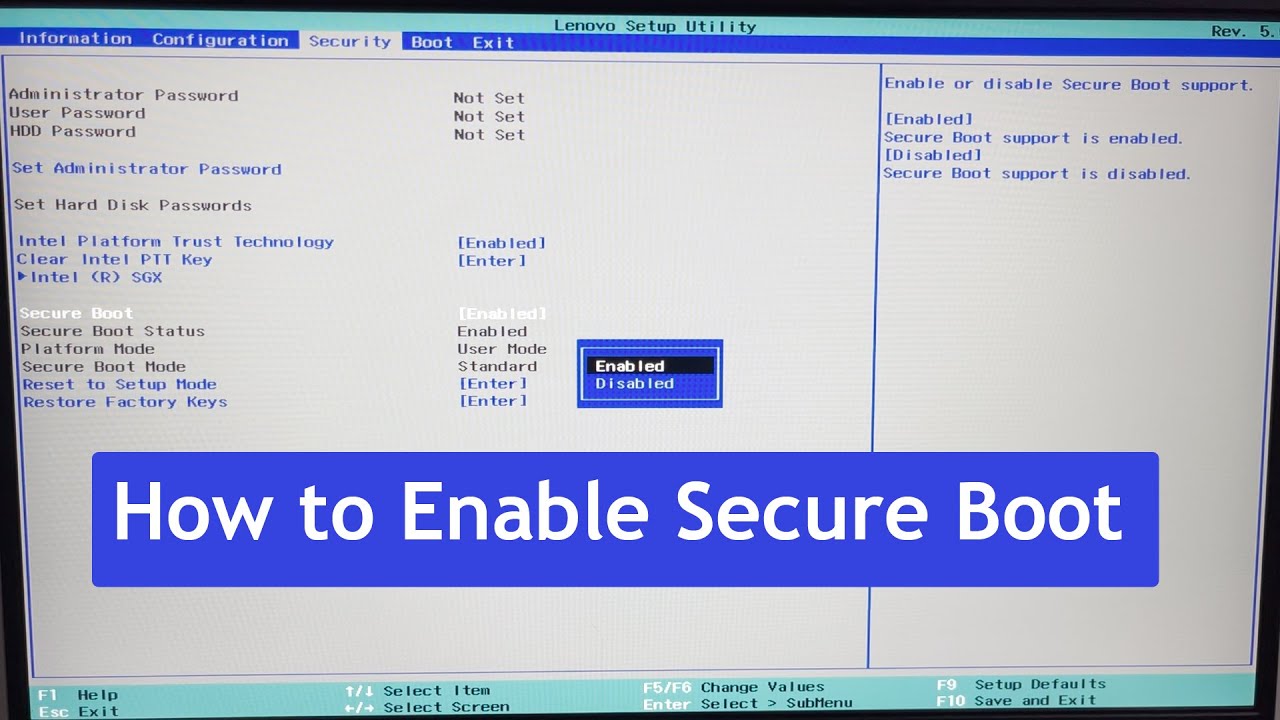
Configuring BIOS Settings to Enable Secure Boot
Once you’ve confirmed that your computer’s BIOS supports secure boot, you can configure the settings to enable the feature. This usually involves setting the secure boot mode to “Enabled” and selecting the Trusted Platform Module (TPM) settings. Make sure to save the changes and exit the BIOS settings to apply the new configuration.
- Restart your computer and enter the BIOS settings by pressing the F2, F12, or Del key.
- Look for the “Secure Boot” option and set it to “Enabled”.
- Select the TPM settings and choose the desired option.
- Save the changes and exit the BIOS settings.
- Restart your computer to apply the new configuration.
Creating a Bootable USB Drive for Secure Boot
A bootable USB drive is essential for secure boot. You’ll need to create one using your computer’s BIOS settings. This involves setting the USB drive as the first boot device and enabling secure boot. Follow these steps to create a bootable USB drive:
- Download a USB creator tool from a trusted source.
- Insert a USB drive into your computer.
- Launch the USB creator tool and select the USB drive as the target device.
- Create the bootable USB drive by following the on-screen instructions.
Troubleshooting Secure Boot Issues
If you encounter any issues with secure boot, you may need to troubleshoot the problem. Common issues include incorrect BIOS settings, missing TPM settings, or incompatible firmware. Check the computer’s documentation or online resources for troubleshooting tips.
Creating a Secure Boot Key

Secure Boot keys play a crucial role in the authentication process, ensuring that only authorized firmware and operating systems can boot on a computer. A Secure Boot key is used to validate the digital signatures of the boot process, preventing unauthorized modifications or tampering.
In order to create a secure boot key, you need to use the MokManager utility. MokManager is a tool that allows you to configure and manage the Secure Boot settings on your system.
Using MokManager to Create a Secure Boot Key
To create a secure boot key using MokManager, follow these steps:
- Boot your system in the Secure Boot mode. If you’re not sure how to do this, refer to the previous steps on preparing your computer for Secure Boot.
- Once you’re in the Secure Boot mode, insert a USB drive that contains the MokManager utility.
- Restart your system and boot from the USB drive.
- When MokManager loads, select the option to create a Secure Boot key.
- MokManager will then prompt you to create a passphrase. This passphrase will be used to unlock the Secure Boot key.
- Enter a strong and unique passphrase. It’s recommended to use a randomly generated passphrase and store it securely for future reference.
- MokManager will then generate the Secure Boot key and store it on the USB drive.
- Remove the USB drive and restart your system. Your system should now be configured to boot using the Secure Boot key.
Scenario: Using a Secure Boot Key for Troubleshooting Secure Boot Issues
Imagine you’re experiencing issues with Secure Boot on your computer. You’ve tried troubleshooting and resolving the issue, but it still persists. In this scenario, a Secure Boot key can be a lifesaver. By creating a Secure Boot key, you can bypass the Secure Boot mechanism and boot into the system, allowing you to troubleshoot and resolve the issue. This can be especially useful if you’re unable to boot into the system due to a Secure Boot issue.
Using Secure Boot to Protect Your Data: How To Turn On Secure Boot
Secure Boot plays a crucial role in safeguarding your system and data from potential threats. By verifying the authenticity of your system’s firmware, Secure Boot prevents malicious code from being executed, thereby ensuring the integrity of your system. In this section, we will delve into the ways in which Secure Boot protects your data and its relationship with encryption.
Preventing Malicious Firmware from Tampering with the System’s Boot Process
Malicious firmware can wreak havoc on your system by tampering with the boot process. It can inject malware during the boot process, rendering your system vulnerable to attacks. Secure Boot prevents this by verifying the authenticity of the firmware before allowing it to execute. This ensures that only authorized firmware is executed, thereby preventing malicious code from infiltrating your system.
Secure Boot achieves this by using digital signatures to verify the firmware’s identity. When you enable Secure Boot, your system checks the firmware’s digital signature against a list of trusted signatures. If the signature matches, the firmware is allowed to execute. However, if the signature doesn’t match, the system refuses to execute the firmware, thereby preventing malicious code from taking control.
Protecting Sensitive Data by Preventing Unauthorized Access
Secure Boot can be used to protect sensitive data by preventing unauthorized access to the system. By ensuring that only authorized firmware is executed, Secure Boot prevents malicious code from gaining access to sensitive data. This is particularly important for systems that handle sensitive information, such as financial or personal data.
In addition, Secure Boot can be used to protect data by preventing unauthorized modifications to the system’s firmware. If a malicious entity gains access to your system’s firmware, they can modify it to steal or delete sensitive data. By using Secure Boot to verify the firmware’s integrity, you can prevent this from happening.
The Relationship Between Secure Boot and Encryption
Secure Boot and encryption are two related but distinct security measures. While Secure Boot protects the boot process and firmware, encryption protects data at rest and in transit. When used together, Secure Boot and encryption provide an additional layer of security for your system and data.
Secure Boot can be used to protect encryption keys by preventing unauthorized access to the system. By ensuring that only authorized firmware is executed, Secure Boot prevents malicious code from accessing encryption keys. This is particularly important for systems that use encryption to protect sensitive data.
In summary, Secure Boot plays a crucial role in protecting your system and data from potential threats. By preventing malicious firmware from tampering with the boot process and protecting sensitive data from unauthorized access, Secure Boot ensures the integrity of your system. When used in conjunction with encryption, Secure Boot provides an additional layer of security for your system and data.
Troubleshooting Secure Boot Issues
Secure Boot issues can be frustrating, but they are often easy to resolve. If you’ve enabled Secure Boot and encounter problems, remain calm and follow these steps to troubleshoot common issues.
Failing to Boot: Secure Boot is Enabled, but the System Won’t Boot, How to turn on secure boot
One of the most common issues with Secure Boot is a system failure to boot. To resolve this, follow these steps:
- Check the UEFI/BIOS settings to ensure Secure Boot is actually enabled. This might seem obvious, but it’s an easy mistake to make.
- Verify that the Secure Boot key you created is correct. Ensure the key matches the one stored on your motherboard or UEFI/BIOS settings.
- Reinstall the Secure Boot key or UEFI/BIOS settings to default values.
- Try booting the system in Safe Mode or without Secure Boot enabled.
- Update your motherboard or UEFI/BIOS to the latest version.
When dealing with boot-related issues, it’s essential to maintain a backup of your system. This way, you can easily restore your system settings and prevent significant data loss.
Invalid Boot Key: Secure Boot Key Not Recognized
An invalid Secure Boot key can cause the system to refuse booting. To resolve this, try the following:
- Recreate the Secure Boot key, ensuring it is stored in the correct location.
- Verify that the Secure Boot key is listed in the UEFI/BIOS settings.
- Update your motherboard or UEFI/BIOS to the latest version.
- Reinstall the Secure Boot key or UEFI/BIOS settings to default values.
Secure Boot keys, like passwords, have specific requirements. Ensure your key is alphanumeric, contains only the allowed characters, and meets any requirements set by your motherboard or UEFI/BIOS.
System Refuses to Boot After Enabling Secure Boot: Possible Causes and Solutions
Several factors might cause the system to refuse booting with Secure Boot enabled. To resolve this, try the following:
| Issue | Solution |
|---|---|
| Secure Boot is enabled, but the system refuses to boot. | Try booting the system in Safe Mode or without Secure Boot enabled. Update your motherboard or UEFI/BIOS to the latest version. |
| Key size is not 256 bits. | Create a new Secure Boot key with a size of 256 bits. |
| Key is not in correct location. | Verify the Secure Boot key location and recreate it if necessary. |
Boot order is crucial when troubleshooting Secure Boot issues. The system attempts to boot from the device at the top of the list. Verify the boot order and adjust it if necessary to resolve any boot-related issues.
Secure Boot can be sensitive to small changes in the system settings or hardware configuration. If you have recently updated your motherboard or UEFI/BIOS, try reverting those changes to resolve Secure Boot issues.
Designing a Secure Boot-Enabled Infrastructure
In large-scale computing environments, designing a secure boot-enabled infrastructure is crucial to ensure the integrity and security of sensitive data. Secure boot prevents unauthorized software from loading and executing during the boot process, thereby reducing the risk of malware and other security threats.
Secure boot can be integrated with existing infrastructure such as network management systems, allowing for seamless monitoring and management of secure boot-enabled systems. This integration enables IT administrators to configure and maintain secure boot-enabled systems more efficiently and effectively.
Role of IT Administrators in Configuring and Maintaining Secure Boot-Enabled Systems
IT administrators play a crucial role in ensuring the secure boot-enabled systems are properly configured and maintained. Their responsibilities include:
- Configuring Secure Boot Settings: IT administrators must configure secure boot settings to ensure that only trusted firmware and software are loaded during the boot process. This involves defining the list of allowed firmware and software, as well as configuring the boot order and other settings.
- Managing Secure Boot Keys: IT administrators must manage secure boot keys, which are used to authenticate the firmware and software loaded during the boot process. This involves generating, storing, and rotating secure boot keys to ensure their security and integrity.
- Maintaining Secure Boot Firmware and Software: IT administrators must stay up to date with the latest secure boot firmware and software updates to ensure that their systems remain secure and compliant with regulatory requirements.
The secure boot process involves a series of verifications and checks to ensure that only trusted firmware and software are loaded during the boot process. This includes checks for digital signatures, encryption, and other forms of authentication.
In a large-scale computing environment, the role of IT administrators in configuring and maintaining secure boot-enabled systems is critical to ensuring the security and integrity of sensitive data. By properly configuring and maintaining secure boot settings, managing secure boot keys, and maintaining secure boot firmware and software, IT administrators can reduce the risk of security threats and ensure the reliability and availability of their systems.
Exploring Advanced Secure Boot Features
Secure Boot is a powerful security feature that ensures only authorized software is loaded on a system at startup. To take this security to the next level, advanced Secure Boot features are now available, providing an even more robust defense against malware and unauthorized software. One of the key components of advanced Secure Boot is the Unified Extensible Firmware Interface (UEFI) firmware, a crucial piece of software that controls the system’s startup process.
UEFI Firmware and Its Integration with Secure Boot
The UEFI firmware plays a central role in Secure Boot, serving as the interface between the system’s hardware and operating system. By integrating Secure Boot with UEFI firmware, systems can verify the authenticity of boot software before it loads, ensuring that only trusted code is executed. This integration provides a secure environment for the system to boot, protecting against bootkits and other malware that rely on exploiting the boot process. UEFI firmware is updated regularly, incorporating the latest security features and patches, which is a significant advantage over traditional firmware, which is often static and difficult to update.
- Secure Boot relies on UEFI firmware to authenticate the boot software before it loads.
- UEFI firmware serves as the interface between the system’s hardware and operating system.
- Secure Boot provides a secure environment for the system to boot by verifying the authenticity of boot software before it loads.
Platform Key Pairs and Their Interaction with Secure Boot
Platform key pairs play a critical role in Secure Boot, providing a secure way to identify and authenticate the system. A platform key pair consists of a public key and a private key, which work together to ensure the system is authenticated. When a system boots, the public key is used to verify the digital signature of the boot software, while the private key is used to create the digital signature. This process ensures that the system can only boot with authorized software and provides a strong defense against unauthorized access.
- The platform key pair consists of a public key and a private key, which work together to authenticate the system.
- The public key is used to verify the digital signature of the boot software, while the private key is used to create the digital signature.
- Secure Boot relies on the platform key pair to ensure the system is authenticated and can only boot with authorized software.
Secure Firmware Update and Recovery
Secure firmware update and recovery are critical advanced Secure Boot features that provide a secure way to update and recover the firmware. This feature ensures that the firmware is always up-to-date and secure, reducing the risk of attacks and unauthorized access. By integrating Secure Boot with secure firmware update and recovery, systems can enjoy an even higher level of security and stability, protecting against firmware-related attacks and ensuring that the system remains secure over its entire lifecycle.
Last Word
In conclusion, Secure Boot offers a robust layer of security for your computer, providing a reliable way to prevent unauthorized access and malicious attacks. By following the steps Artikeld in this guide, you can take control of your system’s security and ensure a safer computing experience.
Detailed FAQs
Can I enable Secure Boot on an older computer system?
Yes, but compatibility may vary depending on the system’s hardware and firmware version. It’s essential to check your system’s specifications before attempting to enable Secure Boot.
What happens if I forget my Secure Boot password?
Don’t worry, you can recover your password using the MokManager utility. If you’re unable to recover it, you may need to reflash your UEFI firmware or contact a professional for assistance.
Can Secure Boot prevent all types of malware?
Secure Boot primarily protects against firmware-based malware, but it’s essential to maintain a layered security approach by using anti-virus software and other security measures to protect against other types of threats.