Delving into how to enable secure boot windows 11, this introduction immerses readers in a unique and compelling narrative, with engaging and thought-provoking content from the very first sentence.
Secure Boot is a critical security feature in Windows 11 that prevents malware and unauthorized firmware from loading during the boot process, ensuring the integrity and stability of your device. It’s essential to understand the benefits and prerequisites for enabling Secure Boot in Windows 11, including the minimum hardware requirements and differences between UEFI and Legacy BIOS modes.
Understanding the Benefits of Secure Boot in Windows 11
Secure Boot is a critical security feature in Windows 11 that helps protect the operating system and user data from malicious attacks. By ensuring that only authorized software can run during the boot process, Secure Boot prevents malware and other unauthorized firmware from loading, thereby enhancing the overall security and stability of the system.
Preventing Malware and Unauthorized Firmware
Secure Boot acts as a shield against malware and other malicious programs that attempt to bypass the normal boot process. During the boot process, Secure Boot verifies the digital signatures of software components, preventing unauthorized or malicious code from executing. This is achieved through the use of a Secure Boot key, which is used to digitally sign trusted firmware and operating system components.
To illustrate this concept, consider a scenario where an attacker attempts to install a malicious rootkit on a Windows 11 system. The attacker creates a modified BIOS (Basic Input/Output System) that bypasses the Secure Boot verification process, allowing the rootkit to load during the boot process. However, due to the Secure Boot feature, the system detects the malicious code and prevents it from executing, thereby preventing the rootkit from compromising the system.
Secure Boot also prevents the installation of unauthorized firmware on the system. For instance, an attacker might try to install a malicious firmware on a system’s network interface controller (NIC) to launch a man-in-the-middle attack. However, Secure Boot ensures that only authorized firmware is installed on the system, preventing the attacker from executing their malicious code.
Comparison with Other Security Features
Secure Boot is an essential component of the Windows 11 security ecosystem, working in conjunction with other features such as Windows Defender, BitLocker, and UEFI Secure Boot. While these features focus on different aspects of security, Secure Boot provides a critical layer of protection against malware and unauthorized firmware.
| Feature | Description |
| :—————– | :————————————————————————————————- |
| Windows Defender | A robust antivirus solution that protects against malware, viruses, and other security threats. |
| BitLocker | A full-disk encryption feature that safeguards user data, even in the event of disk theft or attack. |
| UEFI Secure Boot | A feature that ensures that only authorized firmware can boot a system, preventing unauthorized code. |
These features complement Secure Boot, providing a comprehensive security solution for Windows 11 systems. However, it is essential to note that Secure Boot is a crucial component of the security ecosystem, and disabling it would compromise the overall security and stability of the system.
Real-World Scenario
In 2020, a major security breach was reported at a large financial institution. The breach was caused by an attacker who managed to install malware on a system’s BIOS. The malware was designed to steal sensitive financial data, and it went undetected for several months. The breach was eventually discovered, and the institution was forced to issue a recall of compromised systems.
However, in this scenario, the use of Secure Boot would have prevented the malware from executing in the first place. Since Secure Boot verifies the digital signatures of software components, it would have detected the malicious code and prevented it from loading during the boot process. This would have saved the institution from the costly breach and the subsequent recall of compromised systems.
Prerequisites for Enabling Secure Boot in Windows 11
To enable Secure Boot in Windows 11, your computer must meet certain hardware requirements and firmware configurations. In this section, we will discuss the prerequisites for Secure Boot in Windows 11, including the minimum hardware requirements, UEFI and Legacy BIOS modes, and how to determine your PC’s firmware compatibility.
Minimum Hardware Requirements for Secure Boot in Windows 11
Secure Boot requires a PC with UEFI firmware, which is a newer type of firmware than Legacy BIOS. To enable Secure Boot in Windows 11, your PC must have the following hardware requirements:
* A UEFI firmware-compatible PC
* A Windows 11 operating system installation media that supports Secure Boot
* A Trusted Platform Module (TPM) version 2.0 or later (optional)
* A CPU that supports Secure Boot
Differences Between UEFI and Legacy BIOS Modes
UEFI and Legacy BIOS modes are two different types of firmware configurations used in PCs. To determine your PC’s firmware compatibility, you need to understand the differences between these two modes.
UEFI (Unified Extensible Firmware Interface) is a newer firmware standard that provides a more secure and flexible boot process. UEFI firmware uses a graphical interface and supports features like Secure Boot, which ensures that only authorized operating systems can boot on the PC.
Legacy BIOS, on the other hand, is an older firmware standard that uses a text-based interface and does not support Secure Boot. Legacy BIOS firmware is less secure and less flexible than UEFI firmware.
Table: UEFI vs. Legacy BIOS Modes
| Feature | UEFI | Legacy BIOS |
| — | — | — |
| Boot Process | Graphical interface, supports Secure Boot | Text-based interface, does not support Secure Boot |
| Security | More secure, supports Secure Boot | Less secure, does not support Secure Boot |
| Flexibility | More flexible, supports multiple operating systems | Less flexible, limited to single operating system |
Steps to Determine Your PC’s Firmware Compatibility
To determine your PC’s firmware compatibility, follow these steps:
* Restart your PC and enter the Boot Options menu (usually by pressing F2, F12, or Del keys).
* Look for the firmware settings or Boot Mode menu.
* Check if your PC is set to Legacy BIOS or UEFI firmware.
* If your PC is set to Legacy BIOS, you may need to update your firmware to enable Secure Boot in Windows 11.
UEFI Firmware Requirements for Secure Boot
To enable Secure Boot in Windows 11, your PC must meet the following UEFI firmware requirements:
* The UEFI firmware must support Secure Boot.
* The UEFI firmware must be version 2.3.1 or later.
* The UEFI firmware must have a Trusted Platform Module (TPM) version 2.0 or later.
Legacy BIOS Limitations for Secure Boot
If your PC has Legacy BIOS firmware, it may not support Secure Boot. Legacy BIOS firmware has several limitations that prevent it from enabling Secure Boot, including:
* Limited boot options: Legacy BIOS firmware only allows one boot option, which is the primary hard drive.
* Limited security features: Legacy BIOS firmware does not support Secure Boot, which means that any operating system can boot on the PC.
* Limited flexibility: Legacy BIOS firmware is not as flexible as UEFI firmware and does not support multiple operating systems.
Conclusion
In this section, we discussed the prerequisites for enabling Secure Boot in Windows 11, including the minimum hardware requirements, UEFI and Legacy BIOS modes, and how to determine your PC’s firmware compatibility. We also highlighted the differences between UEFI and Legacy BIOS modes and provided a table summarizing these differences. By understanding these prerequisites, you can enable Secure Boot in Windows 11 and enjoy a more secure and flexible boot process.
Preparing Windows 11 for Secure Boot
Preparing your Windows 11 system for Secure Boot involves several steps that help ensure your system is ready for the Secure Boot process. This includes disabling the Legacy BIOS mode, updating the UEFI firmware, and creating a UEFI-compatible bootable USB drive.
Disabling Legacy BIOS Mode
Disabling the Legacy BIOS mode in Windows 11 is essential for enabling Secure Boot. Here’s how you can do it:
The Legacy BIOS mode is outdated and can cause issues with Secure Boot. To remove this mode, you need to access your UEFI firmware settings. Most PCs have a key press combination to boot directly into the UEFI settings. This varies depending on your system type.
For example, if you have a Dell laptop, press the F2 key when you’re starting the system. You’ll see the UEFI settings page.
– Go to the boot settings: In the UEFI settings, look for the ‘Boot’ tab and click on it.
– Disable Legacy BIOS mode: Find the ‘Legacy BIOS Mode’ option and toggle it off.
Updating UEFI Firmware
Updating your UEFI firmware is crucial to ensure you have the latest security features and fixes. Here’s how you can update your UEFI firmware:
- Find the latest firmware update: Check your system manufacturer’s website for the latest UEFI firmware update for your system.
- Download the update: Download the UEFI firmware update and save it to a folder on your system.
- Run the update tool: Run the UEFI firmware update tool and follow the on-screen instructions to update your UEFI firmware.
- Reboot and confirm update: Reboot your system and enter UEFI settings to confirm the update was successful.
Setting Secure Boot Mode to Custom
In the UEFI firmware settings, you need to set the Secure Boot mode to ‘Custom’. This will allow you to add an exception for your installation media, such as a USB drive.
– Go to the boot settings: In the UEFI settings, go to the ‘Boot’ tab and click on it.
– Set Secure Boot mode to Custom: Find the ‘Secure Boot Mode’ option and select ‘Custom’.
Creating a UEFI-Compatible Bootable USB Drive
To create a UEFI-compatible bootable USB drive, you’ll need a UEFI bootable USB drive creator. Here’s a step-by-step guide to create a UEFI-compatible bootable USB drive:
- Download a UEFI bootable USB drive creator: Download a UEFI bootable USB drive creator like Microsoft’s Media Creation Tool or Rufus.
- Download Windows 11 ISO file: Download the Windows 11 ISO file from Microsoft’s website.
- Create bootable USB drive: Use the UEFI bootable USB drive creator to create a UEFI-compatible bootable USB drive from the downloaded ISO file.
- Boot from USB drive: Insert the USB drive and restart your system. Press the key press combination to access the UEFI settings or press the key to boot from the removable device. Follow the on-screen instructions to install Windows 11.
Enabling Secure Boot in Windows 11
Enabling Secure Boot in Windows 11 is a crucial step towards securing your device and protecting it from unauthorized access. By enabling Secure Boot, you can ensure that only trusted operating systems and applications can run on your device, thereby reducing the risk of malware and other security threats. Here are the steps to enable Secure Boot in Windows 11.
Enabling Secure Boot during Installation
When installing Windows 11, you can enable Secure Boot during the setup process. To do this:
1. Insert the Windows 11 installation media and restart your device.
2. Press the key to enter the UEFI firmware settings. This key will be displayed on the screen during the boot process.
3. Select the language and other preferences, and then click on “Next”.
4. Click on “Install Now” to begin the installation process.
5. In the “Where do you want to install Windows?” screen, select the partition where you want to install Windows.
6. Click on “Custom: Install Windows only (advanced)”.
7. In the “Customize settings” screen, uncheck the box next to “Require a UEFI firmware based system device”.
8. In the “Secure Boot” screen, check the box next to “Secure Boot enabled”.
9. Click on “Next” to begin the installation process.
Enabling Secure Boot after Installation
If you have already installed Windows 11, you can enable Secure Boot after installation using the built-in settings. To do this:
1. Press the Windows key + R to open the Run dialog box.
2. Type “msinfo32” and press Enter to open the System Information window.
3. In the System Summary section, click on “System” and then click on “Device security”.
4. Under “Device security”, click on “Secure Boot”.
5. Check the box next to “Secure Boot enabled” and click on “OK”.
6. Restart your device to apply the changes.
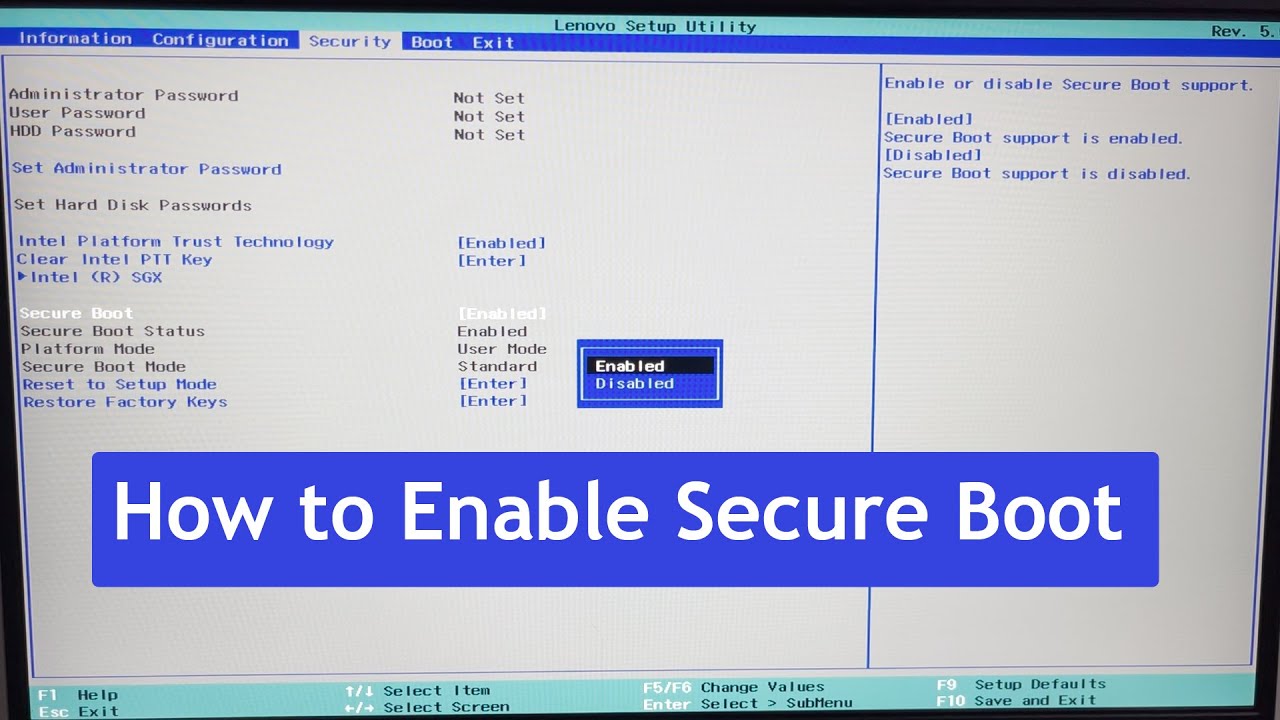
Configuring Secure Boot Mode to “Custom”
You can configure the Secure Boot mode to “Custom” using the UEFI firmware settings. To do this:
1. Press the key to enter the UEFI firmware settings. This key will be displayed on the screen during the boot process.
2. Select the “Boot” tab and then select “Secure Boot”.
3. Check the box next to “Secure Boot mode” and select “Custom” from the dropdown menu.
4. Save your changes and restart your device.
Managing the Trusted Platform Module (TPM), How to enable secure boot windows 11
The Trusted Platform Module (TPM) is a hardware component that stores cryptographic keys and other sensitive data. In Windows 11, you can manage the TPM using the built-in settings. To do this:
1. Press the Windows key + R to open the Run dialog box.
2. Type “tpm.msc” and press Enter to open the TPM Management console.
3. In the TPM Management console, you can view and manage the TPM settings, including enabling or disabling the TPM, creating and deleting certificates, and viewing the TPM status.
Troubleshooting Secure Boot Issues in Windows 11
Troubleshooting Secure Boot issues in Windows 11 is a crucial step to ensure the smooth and secure operation of your device. Secure Boot is a vital security feature that verifies the boot loader and prevents unauthorized access to your system. However, issues may arise during the Secure Boot process, and it’s essential to diagnose and resolve them as soon as possible. In this section, we’ll cover the common issues related to Secure Boot, how to troubleshoot them using Event Viewer logs, and provide guidance on resetting the Secure Boot mode to its default settings.
Common Secure Boot Issues
Secure Boot issues can be frustrating and may prevent your system from booting normally. Some common issues include:
- Firmware or driver issues: Incompatible or outdated firmware or drivers may cause Secure Boot to fail, preventing your system from booting.
- Boot order issue: The boot order may be set incorrectly, causing the system to try and boot from a non-approved device.
- Secure Boot settings: Incorrect or inconsistent Secure Boot settings may prevent the system from booting or cause other issues.
- Malware or viruses: Malware or viruses may infect your system, causing it to become unable to boot securely.
These issues can be difficult to diagnose, but by following the steps Artikeld in the next section, you’ll be able to troubleshoot and resolve the issues.
Troubleshooting Secure Boot Errors with Event Viewer Logs
Event Viewer logs provide valuable information about the Secure Boot process, allowing you to identify and troubleshoot issues. To access the Event Viewer logs, follow these steps:
- Press the Windows key + R to open the Run dialog box and type
eventvwrand press Enter. - In the Event Viewer window, navigate to the
Windows Logssection. - Expand the
Securitysection and look for events related to Secure Boot.
Once you’ve identified the issue, you can take the necessary steps to resolve it. For example, if the issue is related to a firmware or driver issue, you may need to update the firmware or drivers to resolve the problem.
Resetting Secure Boot Mode to Default Settings
If you’re unable to boot your system due to a Secure Boot issue, you may need to reset the Secure Boot mode to its default settings. To do this, follow these steps:
- Enter the BIOS settings by pressing the designated key (usually F2, F12, or Del) during boot.
- Navigate to the
SecurityorSecure Bootsection. - Reset the Secure Boot mode to its default settings.
Reinstalling Windows 11 with Secure Boot Enabled
If the above steps don’t resolve the issue, you may need to reinstall Windows 11 with Secure Boot enabled. To do this, follow these steps:
- Download the latest Windows 11 installation media from the Microsoft website.
- Boot from the installation media and follow the installation prompts.
- During the installation process, select the Secure Boot option from the boot configuration menu.
By following these steps, you’ll be able to troubleshoot and resolve Secure Boot issues in Windows 11, ensuring the smooth and secure operation of your device.
The Event Viewer logs are a valuable resource for troubleshooting Secure Boot issues. By analyzing the logs, you can identify the root cause of the problem and take the necessary steps to resolve it.
Managing Trusted Platform Modules (TPMs) in Windows 11
Trusted Platform Modules (TPMs) play a crucial role in enhancing the security features of Windows 11. In this section, we will explore the differences between TPM 1.2 and TPM 2.0, the benefits of using TPM 2.0, and the steps to enable it.
Differences between TPM 1.2 and TPM 2.0
The primary difference between TPM 1.2 and TPM 2.0 lies in their architecture and functionality. TPM 1.2 is a legacy version that provides limited security features, whereas TPM 2.0 is a more advanced version that offers enhanced security capabilities. Some of the key differences between the two include:
- Hash-based attestation: TPM 2.0 supports hash-based attestation, which allows for more secure and efficient verification of a platform’s identity.
- Platform Configuration Registers (PCRs): TPM 2.0 provides more advanced PCR controls, allowing for more granular control over the platform’s configuration.
- TPM Remote Attestation: TPM 2.0 supports remote attestation, which enables more secure communication between the TPM and remote services.
- Enhanced Cryptographic Functions: TPM 2.0 includes a wider range of cryptographic functions, including support for SHA-512 and RSA-2048.
- Support for more platforms: TPM 2.0 is designed to work with a broader range of platforms and operating systems, including Windows 11.
Benefits of TPM 2.0 in Windows 11
Using TPM 2.0 in Windows 11 provides several benefits, including:
- Enhanced security: TPM 2.0 provides more advanced security features, such as hash-based attestation and remote attestation, which improve the overall security of the platform.
- Improved protection: TPM 2.0 provides more robust protection against malware and other types of attacks, thanks to its advanced cryptographic functions and platform configuration controls.
- Increased trust: TPM 2.0 enables more secure communication between the TPM and remote services, making it easier to establish trust between different parties.
Enabling TPM 2.0 in Windows 11
To enable TPM 2.0 in Windows 11, follow these steps:
- Check if your system has a TPM 2.0-compliant module: You can use the TPM Management Console (tpm.msc) to check if your system has a TPM 2.0-compliant module.
- Enable TPM 2.0 in the BIOS settings: You may need to enable TPM 2.0 in the BIOS settings to allow it to work with Windows 11.
- Install the TPM 2.0 drivers: You may need to install the TPM 2.0 drivers to enable the TPM 2.0 functionality in Windows 11.
- Configure the TPM 2.0 settings: Once the TPM 2.0 drivers are installed, configure the TPM 2.0 settings in the TPM Management Console (tpm.msc).
Comparison of TPM 1.2 and TPM 2.0 Security Features
The following table compares the security features of TPM 1.2 and TPM 2.0:
| | TPM 1.2 | TPM 2.0 |
| — | — | — |
|
- Hash-based Attestation
| No | Yes |
|
- Platform Configuration Registers (PCRs)
| Limited | Advanced controls |
|
- TPM Remote Attestation
| No | Yes |
|
- Enhanced Cryptographic Functions
| Limited | SHA-512 and RSA-2048 |
|
- Support for more platforms
| Limited | Yes |
It’s worth noting that while TPM 1.2 provides some basic security features, it is not considered secure by modern standards. TPM 2.0 is recommended for all new deployments and should be used whenever possible to ensure maximum security and compatibility with modern operating systems.
Configuring Secure Boot Settings in Windows 11: How To Enable Secure Boot Windows 11
Configuring the Secure Boot settings in Windows 11 is an essential step to ensure the security and integrity of your system. By configuring the Secure Boot settings, you can prevent unauthorized software from loading during the boot process and ensure that only trusted software is executed. In this section, we will guide you through the process of configuring the Secure Boot mode to “Custom” using the UEFI firmware settings, adding custom Secure Boot keys, and updating firmware securely.
Configuring Secure Boot Mode to “Custom” using UEFI Firmware Settings
To configure the Secure Boot mode to “Custom” using the UEFI firmware settings, follow these steps:
1. Restart your system and enter the UEFI firmware settings by pressing the key designated by your system manufacturer (usually F2, F12, or Del).
2. Navigate to the Security or Authentication section and select the “Secure Boot” option.
3. Set the “Secure Boot Mode” to “Custom”.
4. Save the changes and exit the UEFI firmware settings.
By setting the Secure Boot mode to “Custom”, you allow the system to load custom Secure Boot keys and firmware updates.
Adding Custom Secure Boot Keys to the UEFI Firmware Settings
To add custom Secure Boot keys to the UEFI firmware settings, follow these steps:
1. Locate the Secure Boot keys on your system’s manufacturer website or in the system’s documentation.
2. Go back to the UEFI firmware settings and navigate to the “Secure Boot” section.
3. Select the “Key Management” or “Secure Boot Keys” option.
4. Add the custom Secure Boot keys to the system by selecting the “Import” or “Add” option.
5. Save the changes and exit the UEFI firmware settings.
By adding custom Secure Boot keys, you can ensure that only authorized software is executed on your system.
Configuring Secure Boot Settings for Firmware Updates
To configure the Secure Boot settings for firmware updates, follow these steps:
1. Make sure the Secure Boot mode is set to “Custom” using the UEFI firmware settings.
2. Download the firmware update from the system’s manufacturer website.
3. Save the firmware update to a USB drive or other removable storage device.
4. Go to the UEFI firmware settings and navigate to the “Boot” section.
5. Select the USB drive or removable storage device with the firmware update.
6. Save the changes and exit the UEFI firmware settings.
By configuring the Secure Boot settings for firmware updates, you can ensure that the update is signed and secure before it is executed.
Real-World Scenario: Secure Firmware Update using Custom Secure Boot Keys
A real-world scenario where custom Secure Boot keys were used to update firmware securely is in the case of a large enterprise that requires secure updates to its network equipment. The network equipment manufacturer provided custom Secure Boot keys to the enterprise, which were then added to the system’s UEFI firmware settings. When a firmware update was required, the enterprise used the custom Secure Boot keys to ensure that the update was signed and secure before it was executed, preventing any potential malicious updates from being executed on the system.
In this scenario, the use of custom Secure Boot keys provided an additional layer of security for the firmware update, ensuring that only authorized software was executed on the system, and protecting the enterprise’s network from potential security threats.
By configuring the Secure Boot settings, you can ensure the security and integrity of your system, preventing unauthorized software from loading during the boot process and ensuring that only trusted software is executed.
End of Discussion
In conclusion, enabling Secure Boot in Windows 11 requires careful consideration of your device’s hardware and firmware settings. By following the steps Artikeld in this article, you can ensure that your device is secure and protected from malware and unauthorized firmware. Remember to troubleshoot any issues that may arise and configure your Secure Boot settings for optimal performance.
FAQ Explained
What is the purpose of Secure Boot in Windows 11?
Secure Boot prevents malware and unauthorized firmware from loading during the boot process, ensuring the integrity and stability of your device.
Do all Windows 11 devices support Secure Boot?
No, not all devices support Secure Boot. You’ll need a device with UEFI firmware to enable Secure Boot in Windows 11.
How do I troubleshoot Secure Boot issues in Windows 11?
Use the Event Viewer logs to troubleshoot Secure Boot errors and reset the Secure Boot mode to its default settings if necessary.
What is the difference between TPM 1.2 and TPM 2.0 in Windows 11?
TPM 2.0 offers improved security features compared to TPM 1.2, including enhanced encryption and authentication capabilities.
Can I customize my Secure Boot settings in Windows 11?
Yes, you can configure custom Secure Boot keys and settings in the UEFI firmware settings.