Delving into how to stop getting spam emails, this guide presents a comprehensive approach to reducing unwanted messages and protecting your inbox. Spam emails have become an increasingly frustrating reality, but there’s hope.
By understanding the tactics employed by spammers and implementing effective email security measures, you can drastically reduce the likelihood of falling victim to these nuisances. In this article, we will delve into the world of spam emails, exploring the strategies that spammers use to lure users into taking action.
Implementing Strategies to Avoid Email Providers’ Filters and Spam Traps
Email providers have implemented sophisticated filtering methods to detect and block spam emails. However, spammers also employ various tactics to bypass these filters and reach their intended recipients. In this section, we will discuss the strategies used by spammers to evade email filters and propose methods to prevent falling victim to their schemes.
Spammers exploit email providers’ filters by using various tactics such as:
Exploiting Sender Policy Framework (SPF)
Sender Policy Framework (SPF) is a protocol that allows domain owners to specify which IP addresses are authorized to send emails on their behalf. However, spammers can create fake email addresses that appear to be authentic, making it challenging for filters to identify them as spam. To avoid being exploited by such tactics, it is essential to use SPF records correctly and ensure that they are aligned with the actual sending IP addresses.
Many email providers offer advanced features, such as DomainKeys Identified Mail (DKIM) and Sender ID, to help prevent spam emails. However, spammers often use tactics like spoofing sender addresses or using compromised domains to send their emails. To prevent falling victim to these tactics:
- Verify the authenticity of sender email addresses by checking their domain and sender name.
- Avoid using generic sender addresses or names.
- Use SPF records to specify authorized sending IP addresses.
- Implement DKIM to add an electronic signature to outgoing emails.
- Use a reputable email service provider (ESP) that supports SPF, DKIM, and other anti-spam features.
- Regularly update and maintain your ESP’s configuration and settings to ensure optimal spam filtering.
Another common tactic used by spammers is to create spam traps, which are email addresses that are designed to be attractive to spammers. These addresses are often abandoned or recycled from previous legitimate email addresses. To avoid falling victim to spam traps:
Avoiding Spam Traps and Generic Forwarding Addresses
Spammers often target generic email addresses, such as “[info@example.com](mailto:info@example.com)” or “[orders@example.com](mailto:orders@example.com),” which are designed to be attractive to spammers. To avoid being caught in a spam trap, it is essential to use authentic and consistent sender names and domains. This will make it more challenging for spammers to identify and target your email address.
When using generic email addresses, make sure to use the @domain.tld format and specify a valid sender name. This will help differentiate your email address from spam traps and generic forwarding addresses.
Domain Verification and Validation
Domain verification and validation are essential steps in preventing spam emails. By verifying the authenticity of sender domains, email providers can improve the accuracy of their spam filters. To ensure domain verification and validation:
- Validate the sender domain using tools like domainr.com or mailtrap.io.
- Ensure that the sender domain is correctly configured with SPF records and DKIM.
- Use a reputable ESP that supports domain verification and validation.
- Regularly update and maintain your ESP’s configuration and settings to ensure optimal spam filtering.
- Avoid using generic sender addresses or names.
Authentic Sender Names and Domains
Authentic sender names and domains are essential for preventing spam emails. By using consistent and authentic sender names and domains, you can make it more challenging for spammers to identify and target your email address.
When using sender names and domains, make sure to follow the best practices for authentic sender identification:
- Use a consistent sender name and domain.
- Avoid using generic sender names or domains.
- Closely monitor and update your sender name and domain to ensure consistency.
- Use the @domain.tld format and specify a valid sender name.
- Ensure that the sender domain is correctly configured with SPF records and DKIM.
By following these strategies, you can effectively prevent your email address from being exploited by spammers and improve the overall accuracy of email filters.
Understanding the Anatomy of Spam Emails and Their Tactics
The anatomy of spam emails involves several common characteristics and tactics that spammers employ to lure people into taking action. These tactics often rely on psychological manipulation, creating a sense of urgency or scarcity. Understanding these tactics can help individuals identify and avoid falling prey to spam emails.
Tactics Used by Spammers
Urgency and Scarcity Tactics
Spammers frequently employ tactics that create a sense of urgency or scarcity. For example, an email may claim that a limited-time offer or promotion expires soon, encouraging the recipient to act quickly. Similarly, scarcity tactics may be used to create a sense of FOMO (fear of missing out), such as limited availability of a product or service.
- Example: An email claims that a new iPhone model is available for a limited time, with orders limited to the first 100 recipients.
- Effect: Recipient feels a sense of urgency and is more likely to act quickly, potentially without thoroughly evaluating the legitimacy of the offer.
Psychological Manipulation
Spammers often use psychological manipulation to make their emails more appealing and increase the likelihood of recipients taking action. This can involve using emotive language, creating a sense of exclusivity, or making unrealistic promises.
- Example: An email uses emotional language to claim that the recipient has been selected for a prize or reward, making them feel special and increasing the likelihood of taking action.
- Effect: Recipient becomes more likely to respond positively, even if the email is malicious or a scam.
Phishing and Social Engineering
Phishing and social engineering are common tactics used by spammers to trick recipients into revealing sensitive information, such as login credentials or financial information. This can be achieved through emails that appear legitimate but actually lead to malicious websites or attachments.
- Example: An email claims to be from a well-known bank or financial institution, asking the recipient to update their account information.
- Effect: Recipient may provide sensitive information, which can be used for malicious purposes.
Using Real-Life Examples
To illustrate the effectiveness of these tactics, it’s essential to examine real-life examples of successful spam campaigns. For instance, the 2013 Target data breach was attributed to a phishing campaign that exploited vulnerabilities in the retailer’s security systems.
| Example | Effect |
|---|---|
| 2013 Target data breach | Phishing campaign exploited vulnerabilities, resulting in a massive data breach. |
Analyzing Scarcity Tactics
Scarcity tactics can be particularly effective in creating a sense of urgency, as seen in the following example:
“Limited time offer: 50% off on all iPhone orders. Order now to avoid missing out!”
In this example, the scarcity tactic is combined with a sense of exclusivity and a limited-time offer, making the recipient more likely to act quickly.
Dissecting Psychological Manipulation, How to stop getting spam emails
Spammers often use psychological manipulation to create a sense of trust or FOMO. For example:
“Congratulations, you’ve been selected for a prize. Click the link below to claim your reward.”
In this example, the email uses emotional language and a sense of exclusivity to create a sense of trust and increase the likelihood of the recipient taking action.
Creating Effective Filters and Whitelists to Manage Spam
Effectively managing email spam requires a multi-faceted approach that includes implementing robust email filters and whitelists. By setting up and maintaining these tools, individuals and organizations can significantly reduce the amount of unwanted mail they receive, minimizing the risk of clicking on malicious links or opening attachments that may compromise their online security.
A well-crafted filter is essential for preventing spam emails from entering a user’s inbox. This involves creating rules that capture and divert suspicious emails to a designated spam folder. The process of designing these rules requires attention to the various characteristics of spam emails, such as sender addresses, subject lines, and content. Effective filters often identify patterns and anomalies in email behavior, enabling them to block spam before it reaches the inbox.
Common Filter Rules
A set of common filter rules can be employed to capture and block spam emails. These include:
- Sender domain blacklisting: This involves creating a list of domains that are known to send spam and blocking emails from these sources.
- Key phrase blocking: Specific words or phrases can be identified and blocked from appearing in email subject lines or content.
- Attachment blocking: Attachments from unknown sources can be blocked to prevent malware from entering the system.
- IP address blocking: IP addresses associated with known spamming activities can be blocked to prevent spammers from sending emails.
- Header checking: Email headers can be examined for specific characteristics, such as sender IP addresses or message IDs, to identify and block spam.
It is essential to note that the effectiveness of these rules depends on how well they are crafted and maintained. Regular updates and refinements are necessary to account for new spamming tactics and evolving spam patterns.
Whitelists
Implementing whitelists provides an additional layer of protection against spam by allowing trusted senders to bypass filters and deliver their messages directly to the inbox. Whitespace can be configured to automatically grant sending privileges to familiar senders or domains. This ensures that legitimate emails are not mistakenly flagged as spam, even if they exhibit characteristics that match spam profiles.
Strategies for Avoiding False Positives
Creating an effective whitelist requires a balance between granting access to trusted senders and minimizing the risk of false positives. This can be achieved by:
- Creating rules based on specific sender addresses rather than domains.
- Using a combination of sender and recipient addresses to identify genuine emails.
- Configuring whitelists to only permit emails from known senders with specific IP addresses.
- Implementing a secondary spam filter to review emails marked as spam by the primary filter.
By carefully designing and maintaining email filters and whitelists, individuals and organizations can protect themselves against spam and other security threats. This involves staying informed about emerging spamming tactics and regularly updating filters to ensure their continued effectiveness.
Customizing Filters for Specific Spammer Patterns
Customizing filters to address specific spammer patterns is a powerful tool for minimizing spam. This involves analyzing the tactics employed by spammers and creating rules that capture these patterns. By doing so, filters can be tailored to the unique characteristics of a particular spam campaign, significantly reducing the amount of unwanted mail.
This involves analyzing the tactics employed by spammers and creating rules that capture these patterns. Regular updates and refinements are necessary to account for new spamming tactics and evolving spam patterns. By combining these rules, users can create a comprehensive filter system that protects their inboxes from the diverse range of spamming activities.
By creating and maintaining effective email filters and whitelists, users can significantly reduce their exposure to spam and other security threats. Customizing filters to address specific spammer patterns is a critical aspect of this process, enabling users to adapt to the evolving spam landscape and protect themselves against emerging threats.
The Role of Community Participation in Reducing Email Spam

Community participation has emerged as a crucial component in the fight against email spam. By leveraging collective knowledge and expertise, individuals can work together to identify and mitigate spam threats. This collaborative approach not only enhances the effectiveness of email security measures but also fosters a sense of community and shared responsibility.
One of the primary ways community participation contributes to email security is through user reporting. When users flag suspicious emails as spam, they provide valuable insights that can be used to identify and block malicious senders. This feedback loop enables email providers to refine their algorithms and improve their ability to detect and filter out spam.
User-Driven Community Engagement
User-driven community engagement is a critical aspect of email security. By empowering users to take an active role in reporting spam, email providers can create a feedback loop that helps to refine their filtering systems. This collaborative approach has several benefits, including improved spam detection rates and reduced false positives.
When users report spam emails, they provide valuable information that can be used to update filtering algorithms. This information can include details such as the sender’s email address, the content of the email, and the recipient’s IP address. By analyzing this data, email providers can identify trends and patterns that help to identify malicious senders.
Benefits of Community-Driven Email Security
Community-driven email security offers several benefits, including improved spam detection rates, reduced false positives, and enhanced user engagement. By empowering users to take an active role in reporting spam, email providers can create a feedback loop that helps to refine their filtering systems.
- Improved Spam Detection Rates: Community-driven email security enables email providers to refine their filtering systems, leading to improved spam detection rates.
- Reduced False Positives: By empowering users to report spam emails, email providers can reduce the number of false positives, which can lead to user frustration and decreased trust in email providers.
- Enhanced User Engagement: Community-driven email security encourages user participation, leading to a sense of community and shared responsibility.
Expert Opinions on Community-Driven Email Security
Experts in the field of email security emphasize the importance of community participation in reducing email spam. According to a study by the Email Sender and Provider Coalition, community-driven email security is a critical component of effective email filtering systems.
- “Community-driven email security is a critical component of effective email filtering systems. By empowering users to report spam emails, email providers can create a feedback loop that helps to refine their filtering systems.”
- “The benefits of community-driven email security are clear. By improving spam detection rates, reducing false positives, and enhancing user engagement, email providers can create a more secure and trustworthy email experience for users.”
Implementing Community-Driven Email Security
Implementing community-driven email security requires several key components, including user reporting tools, feedback loops, and analytics tools. By leveraging these components, email providers can create a collaborative environment that empowers users to take an active role in reporting spam.
When implementing community-driven email security, email providers should consider the following key components:
* User reporting tools: Provide users with easy-to-use reporting tools that enable them to flag suspicious emails as spam.
* Feedback loops: Establish feedback loops that allow email providers to refine their filtering systems based on user feedback.
* Analytics tools: Use analytics tools to analyze user feedback and identify trends and patterns that can inform filtering decisions.
Challenges and Limitations
While community-driven email security offers several benefits, it also poses several challenges and limitations. Some of the key challenges and limitations include:
* User engagement: Encouraging user participation can be a challenge, particularly among users who may not be familiar with email security best practices.
* Data quality: The quality of user feedback can impact the effectiveness of community-driven email security. Low-quality feedback can lead to inaccurate filtering decisions.
* Scalability: Community-driven email security can be resource-intensive, particularly for large email providers with millions of users.
By understanding these challenges and limitations, email providers can develop effective strategies for implementing community-driven email security that meet the needs of their users.
End of Discussion
By following the tips Artikeld in this guide, you will be well-equipped to tackle the complex issue of spam emails head-on. Remember, preventing spam emails requires a combination of knowledge, vigilance, and collaboration, but with the right tools and mindset, you can keep your inbox safe from unwanted messages.
Essential Questionnaire: How To Stop Getting Spam Emails
Q: What is the best way to identify spam emails?
A: Look out for suspicious sender names, misspelled words, and generic greetings, such as “Dear Customer”. Legitimate emails usually contain personalization and accurate information.
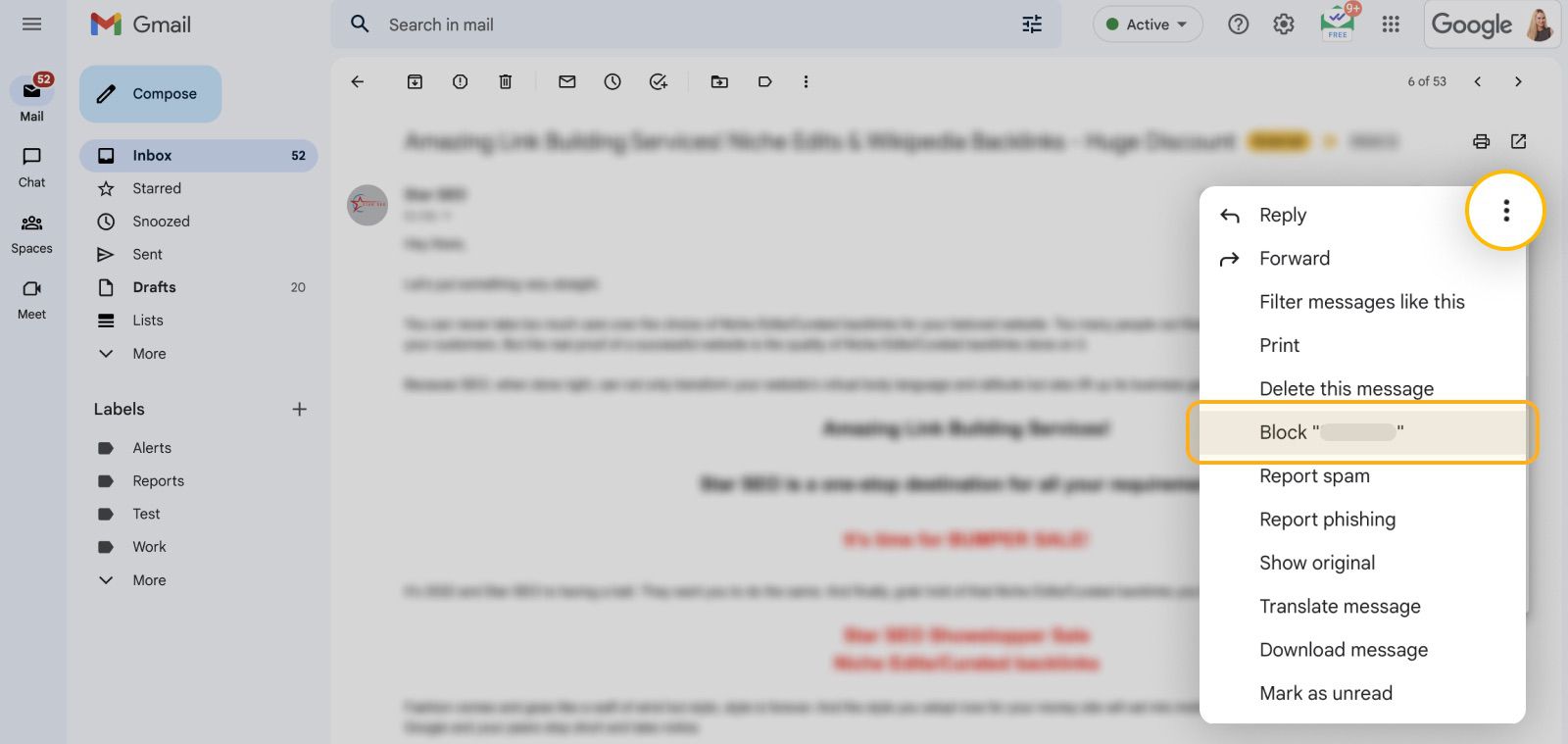
Q: How can I block spam emails from a specific sender?
A: Most email providers allow you to block specific senders by adding their email address to your “block sender” list or creating a filter to automatically reroute their messages to your spam folder.
Q: What is the difference between a spam filter and a whitelist?
A: A spam filter catches suspicious messages and moves them to the spam folder, while a whitelist allows emails from trusted senders to bypass the spam filter and reach your inbox.
Q: Can I report spam emails to my email provider?
A: Yes, most providers allow users to report suspected spam emails, helping to improve their filtering algorithms and reduce unwanted messages.
Q: How often should I update my email provider’s filter settings?
A: It’s essential to regularly review and update your filter settings to adapt to changing spam tactics and improve your email security.