Kicking off with how to hack instagram, this opening paragraph is designed to captivate and engage the readers, setting the tone that unfolds with each word. The intricate world of social media hacking is a complex issue that affects millions worldwide.
The potential consequences of hacking into someone’s instagram account are far-reaching, including legal repercussions and damage to online reputation. In this article, we will delve into the world of hacking instagram, exploring the risks, vulnerabilities, and methods used by hackers to gain unauthorized access to accounts.
Understanding the Risks Associated with Hacking Instagram
Hacking into someone’s Instagram account can have severe consequences, both legally and socially. The platform’s vast user base and sensitive personal information make it an attractive target for malicious actors. As a result, those who choose to engage in hacking may be putting themselves at significant risk.
Criminal Consequences of Hacking Instagram
Hacking into someone’s Instagram account is a serious crime that can lead to severe penalties. Under the Computer Fraud and Abuse Act (CFAA), individuals who hack into computer systems without authorization can face fines and imprisonment. In the case of Instagram, hackers may be charged with computer intrusion, identity theft, and unauthorized access to computer systems. A single hacking incident can lead to charges for multiple counts of these offenses, resulting in substantial prison sentences.
Some examples of potential charges include:
- Hacking into a high-profile Instagram account can lead to charges of identity theft, as the hacker gains access to sensitive personal information like passwords, addresses, and phone numbers.
- Hacking into a business Instagram account can lead to charges of unauthorized access to computer systems, as the hacker gains access to sensitive business information like financial data and trade secrets.
- Hacking into multiple Instagram accounts can lead to charges of computer intrusion, as the hacker uses automated scripts to break into multiple accounts at once.
Additionally, hackers may be charged with state crimes like California’s Computer Crimes Law, which penalizes unauthorized access to computer systems with up to 3 years in prison and a fine of up to $10,000.
Damaging Online Reputation
Beyond the legal consequences, hacking Instagram can have serious social consequences. Hackers who compromise Instagram accounts can damage the online reputation of their victims, spreading misinformation and creating a sense of distrust. A single hacking incident can lead to a loss of credibility, loss of customers or followers, and damage to a person’s professional or personal reputation.
Steps to Avoid Getting Hacked on Instagram:
To avoid getting hacked on Instagram, follow these simple steps:
- Use strong and unique passwords for your Instagram account.
- Enable two-factor authentication (2FA) to prevent unauthorized access to your account.
- Be cautious when clicking on suspicious links or downloading attachments from unknown sources.
- Regularly update your Instagram app and operating system to ensure you have the latest security patches.
- Monitor your account activity regularly for suspicious behavior.
By being aware of the risks associated with hacking Instagram and taking steps to secure your account, you can protect yourself from the potential consequences of hacking and maintain a safe and trustworthy online presence.
Identifying Security Vulnerabilities in Instagram Accounts
Identifying security vulnerabilities in Instagram accounts is crucial in preventing hackers from gaining access to an individual’s personal data and sensitive information. These vulnerabilities can be caused by various factors such as a weak or default password, phishing scams, or a compromised device. The following are some common security vulnerabilities that can be exploited by hackers to gain access to Instagram accounts.
Weak or Default Passwords
A weak or default password can be easily guessed or cracked by hackers, allowing them to access an Instagram account. This can be prevented by using a strong and unique password that consists of a mix of uppercase and lowercase letters, numbers, and special characters. It is also essential to avoid using easily guessable information such as names, birthdays, or common words.
A weak password is an invitation for hackers to exploit and steal personal data. According to a study, 68% of hacking incidents occurred due to weak or easily guessable passwords.
Phishing Scams
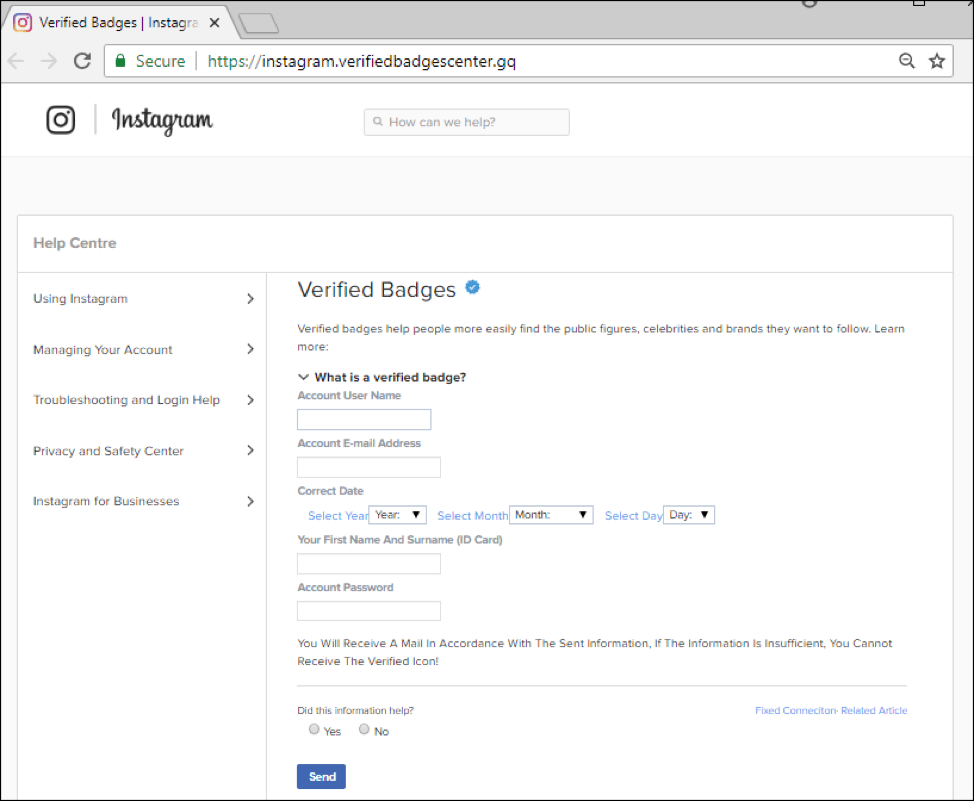
Phishing scams involve hackers sending fake emails or messages that appear to be from a legitimate source, such as Instagram, in an attempt to deceive users into divulging their login credentials or sensitive information. These scams can be in the form of a suspicious email or message that asks users to update their account information or click on a link to access their account.
Compromised Devices
A compromised device, such as a smartphone or computer, can be a serious security risk as it can be used to hack an Instagram account. Hackers can install malware or viruses on a device, which can allow them to access sensitive information and login credentials.
Two-Factor Authentication (2FA)
Two-factor authentication (2FA) is a security feature that requires users to provide a second form of verification, in addition to their password, to access their account. This can be in the form of a code sent to their phone or email, or a biometric verification, such as a fingerprint or facial recognition. To use 2FA on Instagram, go to Settings > Security > Two-Factor Authentication.
When using 2FA on Instagram, the following steps are taken:
Step 1: Enable 2FA on Instagram by going to Settings > Security > Two-Factor Authentication
Step 2: Choose your 2FA method, such as SMS, Email, Authentication Apps (like Google Authenticator), or U2F Security Keys
Step 3: Enter the verification code sent to your phone or email when prompted
Step 4: Set up a backup code in case you lose access to your authenticator, to ensure continued access to your account.
By enabling 2FA on Instagram, users can add an extra layer of security to their account, making it more difficult for hackers to gain access.
Keeping Software and Apps Up-to-Date
Keeping software and apps up-to-date is essential in protecting against hacking attempts. Software and app updates often include security patches that fix vulnerabilities and protect against new threats. It is also essential to keep operating systems, web browsers, and other software up-to-date, as these are often used as entry points for hackers.
The following are some best practices to keep software and apps up-to-date:
1.: Enable Automatic Updates for software and apps
2.: Regularly check for updates and install them promptly
3.: Use antivirus software to scan for malware and viruses
4.: Use a reputable internet security suite to protect against hacking attempts
By following these best practices, users can ensure that their software and apps are up-to-date and secure, reducing the risk of hacking attempts.
Conclusion
In conclusion, identifying security vulnerabilities in Instagram accounts and taking steps to prevent hacking attempts is crucial in protecting personal data and sensitive information. By using strong and unique passwords, being cautious of phishing scams, keeping devices secure, and enabling 2FA and keeping software and apps up-to-date, users can significantly reduce the risk of hacking attempts and protect their Instagram accounts.
Techniques Used by Hackers to Access Instagram Accounts
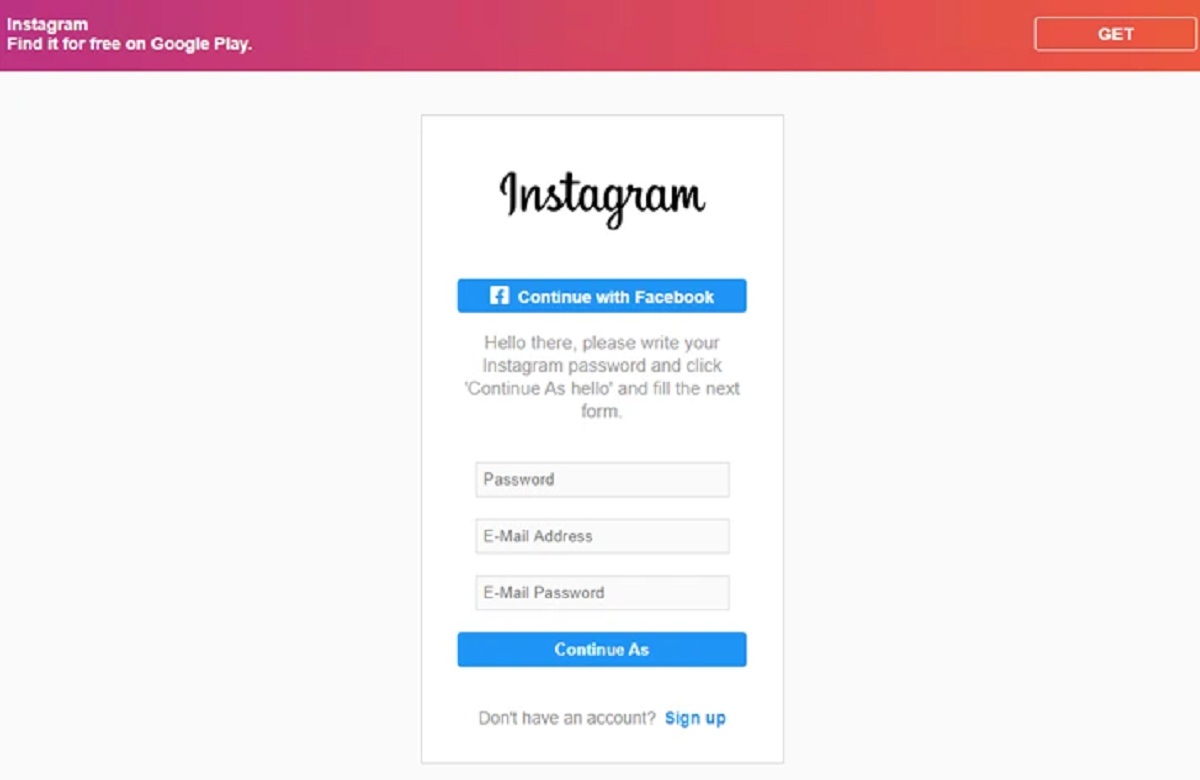
Phishing attacks are a common technique used by hackers to access Instagram accounts. Phishing attacks involve tricking users into divulging their login credentials, such as usernames and passwords. This can be done through various means, including emails, messages, and even fake websites that mimic the Instagram login page.
Phishing attacks can be classified into several types, including:
* Spear phishing: A targeted phishing attack that involves tricking a specific individual or group into divulging their login credentials.
* Whaling: A type of phishing attack that involves tricking high-level executives or other high-profile targets into divulging their login credentials.
* Phishing kits: Pre-built phishing kits that can be easily customized and deployed to steal login credentials from unsuspecting victims.
These types of phishing attacks are often used in conjunction with social engineering tactics, such as creating a sense of urgency or fear in order to trick the victim into divulging their login credentials.
### Identifying and Avoiding Common Phishing Scams on Instagram
To identify and avoid phishing scams on Instagram, users should be aware of the following red flags:
* Unsolicited messages or emails that ask for login credentials
* Messages or emails that create a sense of urgency or fear
* Fake websites or login pages that mimic the Instagram login page
* Links or attachments that seem suspicious or out of place
To avoid phishing scams on Instagram, users should always:
* Be cautious of unsolicited messages or emails that ask for login credentials
* Verify the authenticity of any message or email that asks for login credentials
* Use two-factor authentication to add an extra layer of security to their account
* Regularly monitor their account activity and report any suspicious activity to Instagram
### Comparing the Characteristics of Different Types of Malware Used to Hack Instagram Accounts
| Type of Malware | Description | Common Characteristics |
| — | — | — |
| Ransomware | Malware that encrypts a user’s files and demands payment in exchange for the decryption key | Can spread through phishing emails, can be spread through drive-by downloads, can be encrypted |
| Trojan | Malware that disguises itself as a legitimate program or file | Can be spread through phishing emails, can be spread through drive-by downloads, can be used to steal login credentials |
| Spyware | Malware that is designed to secretly monitor a user’s online activity | Can be spread through phishing emails, can be spread through drive-by downloads, can be used to steal login credentials |
These types of malware are often used in conjunction with phishing attacks to gain access to a user’s login credentials. Users should be aware of these types of malware and take steps to protect themselves, such as using anti-virus software and keeping their software up to date.
Best Practices for Securing Your Instagram Account
Securing your Instagram account from hacking attempts is crucial in today’s digital age. With millions of users worldwide, social media platforms like Instagram have become prime targets for hackers. To protect your account, it’s essential to understand the importance of keeping personal information private and how to use strong passwords.
Password Management
Using password managers is a highly effective way to generate and store complex, unique passwords for different accounts. Password managers, such as LastPass or 1Password, allow you to store your login credentials securely and generate strong, unique passwords for each account. This way, even if one of your accounts is compromised, your other passwords remain secure.
Password managers can generate passwords that are nearly impossible to guess!
Two-Factor Authentication
Enabling two-factor authentication (2FA) adds an extra layer of security to your Instagram account. 2FA requires you to provide a second form of verification, such as a code sent to your phone or a fingerprint scan, in addition to your password. This makes it much more difficult for hackers to access your account, even if they have your password.
Strong Passwords
Using strong, unique passwords for your Instagram account is essential. Avoid using easily guessable information such as your name, birthdate, or common words. Instead, use a combination of uppercase and lowercase letters, numbers, and special characters to create a password that’s difficult to crack.
A strong password should be at least 12 characters long and include a mix of characters.
Private Account Settings, How to hack instagram
Keeping your account private is crucial in preventing hacking attempts. Only allow follow requests from people you know or trust. You can also control who can view your posts by adjusting your account settings.
Daily Security Check
Conduct a daily security check on your Instagram account to identify any suspicious activity. If you notice any strange activity or unauthorized login attempts, immediately change your password and alert Instagram’s support team.
Password Updates
Regularly update your passwords to prevent password breaches. You should update your passwords every 60 days and make sure they are complex and unique.
Public Network Safety
When accessing your Instagram account from public Wi-Fi networks, use a VPN to ensure your data is encrypted.
Report Suspicious Activity
Report any suspicious activity on your Instagram account to the support team. If you notice any strange account activity or receive unauthorized login requests, alert the support team immediately.
Account Recovery
Make sure to have a secure password recovery process in place. You should store a secure password recovery question with an answer that’s known only to you.
Password Sharing
Do not share your passwords with others. Keep your passwords confidential and secure.
- Enable two-factor authentication (2FA) to add an extra layer of security to your Instagram account.
- Use strong, unique passwords for your Instagram account and update them every 60 days.
- Keep your account private by only allowing follow requests from people you know or trust.
- Conduct a daily security check on your Instagram account to identify any suspicious activity.
- Use password managers to generate and store complex, unique passwords for different accounts.
- Enable VPN when accessing your Instagram account from public Wi-Fi networks.
- Report any suspicious activity on your Instagram account to the support team.
- Have a secure password recovery process in place and store a secure password recovery question with an answer that’s known only to you.
- Do not share your passwords with others.
- Monitor your account for any unauthorized access or login attempts.
Protecting Instagram Accounts from Advanced Threats
Sophisticated hackers employ various techniques to compromise high-profile Instagram accounts, often relying on exploitation of vulnerabilities in software or human behavior. One common method used by hackers is phishing attacks, which involve sending fake messages or emails that appear to be from a legitimate source, such as Instagram’s support team, in an attempt to trick users into revealing sensitive information like login credentials or two-factor authentication codes.
Methods Used by Sophisticated Hackers
Advanced hackers often use more sophisticated tactics, including social engineering, where they create fake social media profiles or use psychological manipulation to obtain sensitive information from users. For instance, they might create a fake account that appears to be from a friend or family member, or send messages that are designed to create a sense of urgency or concern in order to prompt users into revealing confidential information.
Importance of Anti-Virus Software and Firewalls
Using anti-virus software and firewalls is crucial in protecting against hacking attempts. Many modern operating systems come with built-in anti-virus software, which can be configured to automatically update and run scans in the background. Similarly, firewalls can be configured to block incoming traffic from unauthorized sources, preventing hackers from accessing sensitive information.
When accessing sensitive information online, consider using a virtual private network (VPN) to protect against data interception and eavesdropping.
Using a VPN can help mask your IP address and encrypt your internet traffic, making it much harder for hackers to intercept sensitive information.
The Role of Virtual Private Networks (VPNs)
A VPN is an internet-based service that provides a secure connection over an insecure (public) network. When using a VPN, a user’s internet traffic is tunneled through a secure connection, encrypting the data in transit. This makes it virtually impossible for hackers to intercept sensitive information, providing an additional layer of security for users who need to access sensitive information online.
Concluding Remarks: How To Hack Instagram
In conclusion, hacking instagram is a serious issue that requires attention and action. By understanding the risks, identifying security vulnerabilities, and taking appropriate measures, we can protect ourselves and our online accounts from falling prey to these malicious activities.
Question Bank
Q: Is it illegal to hack into someone’s instagram account?
A: Yes, hacking into someone’s instagram account without their permission is a serious offense and a violation of their privacy.
Q: Can I recover my hacked instagram account?
A: In most cases, yes, you can recover your hacked instagram account by following the instructions provided by instagram’s support team.
Q: How do I prevent my instagram account from getting hacked?
A: To prevent your instagram account from getting hacked, use a strong password, enable two-factor authentication, and keep your account and software up-to-date.
Q: Is it possible to hack an instagram account using public Wi-Fi?
A: Yes, public Wi-Fi is a common target for hackers, and using it to access your instagram account can put your account at risk of being hacked.
Q: Can I trust instagram’s recovery options to help me regain access to my hacked account?
A: Yes, instagram’s recovery options are designed to help you regain access to your account in case of being hacked.