How to remove activation lock without previous owner sets the stage for this informative guide, offering readers a comprehensive overview of the process and its implications. This detailed narrative delves into the technical aspects of activation lock removal, highlighting the risks and consequences of unauthorized attempts and the benefits of cooperation.
The activation lock is a critical security feature designed to protect devices from unauthorized access and theft. However, situations may arise where removal of the activation lock is necessary, but difficult without the prior owner’s consent. In such cases, understanding the intricacies of activation lock removal and the potential consequences of unauthorized attempts are crucial for both the owner and the service provider.
Exploring Alternative Methods for Removing Activation Lock Without Prior Owner’s Consent
When an individual attempts to remove the activation lock from a device without the consent of the previous owner, they may face severe consequences, including legal repercussions and heightened security risks. This approach, often referred to as “jailbreaking” or “imei unlock,” can lead to irreversible damage to the device and compromise its security.
Potential Consequences of Unauthorized Activation Lock Removal
Attempting to remove the activation lock without prior owner’s consent can result in a series of undesirable outcomes, including:
- Device Bricking or Freezing: Unauthorized attempts to remove the activation lock can cause the device to become unusable, leading to a financial loss due to repairs or replacement.
- Loss of Personal Data: Malicious or unauthorized software may gain access to sensitive personal information, putting the user’s data at risk.
- Security Risks: Removing the activation lock without consent can expose the device to security threats, including malware, phishing, or other forms of cyber attacks.
- Voiding Device Warranty: Unsuccessful attempts to remove the activation lock can void the device’s warranty, leaving the user without support or coverage.
- Legal Consequences: Depending on the jurisdiction, individuals may face fines, penalties, or even prosecution for attempting to remove the activation lock without consent.
Situations Where Prior Owner’s Cooperation is Crucial
In certain situations, the removal of the activation lock is necessary but difficult without the prior owner’s cooperation. For instance:
– A device is no longer functional due to software issues.
– The device is locked due to a forgotten or unknown password.
– The device’s previous owner has gone missing or is unreachable.
Comparison of Authorized and Unauthorized Activation Lock Removal Methods
Authorized activation lock removal methods, involving prior owner’s participation, offer several benefits over unauthorized attempts, including:
– Improved Security: Authorized methods adhere to established security protocols, minimizing the risk of security breaches.
– Reduced Liability: Authorized methods mitigate potential liabilities, ensuring a smooth transfer of ownership or device management.
– Warranty Coverage: Authorized methods typically preserve the device’s warranty, offering users coverage and support.
– Convenience: Authorized methods simplify the process, allowing users to regain control of their device without compromising its security.
In contrast, unauthorized methods, characterized by bypassing established security protocols, pose significant risks to the device and its user, including:
– Security Vulnerabilities: Unauthorized methods can create openings for malicious software to exploit, compromising the device’s security.
– Potential Liabilities: Unauthorized methods may lead to unforeseen consequences, including fines, penalties, or prosecution.
– Device Bricking: Unauthorized methods can irreparably damage the device, rendering it unusable.
Evaluating the Feasibility of Alternative Methods
Alternative methods, such as working with the device’s manufacturer or utilizing software designed for removal, can present viable options for removing the activation lock without prior owner’s consent. However, these methods should be approached with caution and scrutiny, as they may still pose risks to the device’s security and warranty coverage.
Understanding the Role of Activation Lock in Protecting Device Security
Activation Lock, also known as Activation Lock or Activation Lock Screen, is a security feature designed by Apple to protect iPhone, iPad, and iPod touch devices from unauthorized access and theft. When enabled, Activation Lock requires the user to sign in with the Apple ID and password associated with the device, preventing anyone else from using or erasing the device without permission.
The Activation Lock feature is a critical component of the Device Enrollment Program (DEP) and the Find My iPhone service, which allows owners to track and remotely erase their devices if they are lost or stolen. Activation Lock is also linked to the device’s serial number, making it difficult for thieves to resell or reuse the device.
Technical Mechanisms Behind Activation Lock
Activation Lock is based on a combination of hardware and software components that work together to secure the device. When the device is turned on, it checks for the presence of a valid Apple ID and password. If the correct credentials are not entered, the device is locked and cannot be used. The Activation Lock feature is implemented through a firmware-level security mechanism that prevents the device from being booted without the correct authentication.
Device Manufacturers’ Implementation of Activation Lock
While Activation Lock was initially available on Apple devices, other manufacturers have since developed their own equivalent security features. For example:
* Samsung offers Knox, a security platform that includes features like Activation Lock and Secure Folder.
* Google provides Factory Reset Protection (FRP) on Android devices, which requires the user to sign in with their Google account after a factory reset.
Comparison of Security Protocols
While Activation Lock and similar features provide a high level of security, there are variations in security protocols between device manufacturers.
* Apple’s Activation Lock uses a secure boot process to validate the device’s firmware, ensuring that only trusted software can run on the device.
* Samsung’s Knox uses a separate boot process for secure apps, while also providing a secure data storage feature.
* Google’s FRP uses a combination of hardware and software components to prevent unauthorized access.
Scenarios Where Activation Lock Was Successfully Breached or Bypassed
Despite the security features implemented by device manufacturers, there have been instances where Activation Lock was successfully breached or bypassed.
* In 2017, a researcher demonstrated a method to bypass Activation Lock on iOS devices by exploiting a vulnerability in the device’s boot process.
* In 2019, a report revealed that some iOS devices could be unlocked using a method that exploited a weakness in the device’s hardware.
* In 2020, a research paper described a method to bypass FRP on Android devices, allowing unauthorized access to the device.
While these scenarios demonstrate the importance of Activation Lock in protecting device security, they also highlight the need for ongoing security research and development to prevent and mitigate security threats.
| Security Feature | Device Manufacturer | Security Protocol |
|---|---|---|
| Activation Lock | Apple | Secure Boot, hardware-level security mechanism |
| Knox | Samsung | Separate boot process for secure apps, secure data storage feature |
| FRP | Combination of hardware and software components to prevent unauthorized access |
The security of a device is only as strong as its weakest link.
Activation Lock and similar security features are designed to protect devices from unauthorized access and theft. While these features provide a high level of security, they are not foolproof, and ongoing security research and development are necessary to prevent and mitigate security threats.
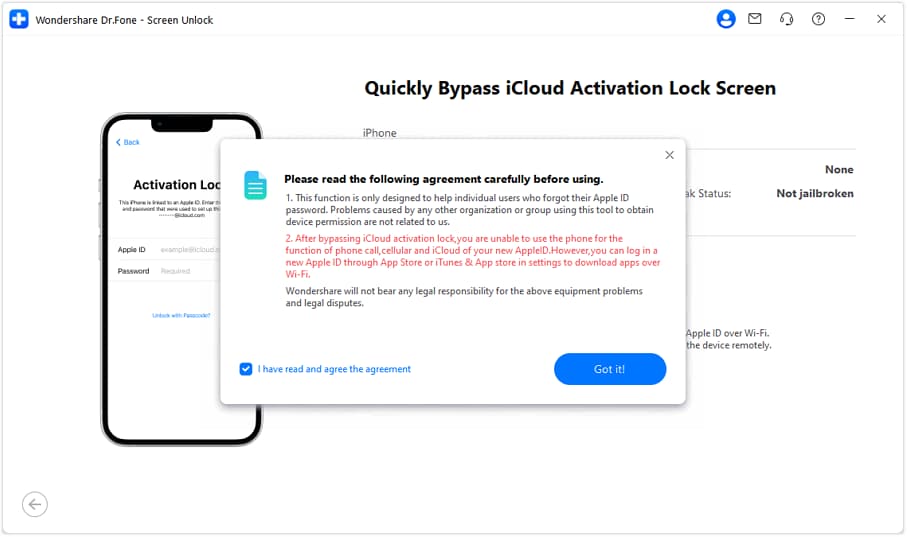
Evaluating the Viability of Online Tools and Services for Removing Activation Lock
Evaluating the viability of online tools and services for removing activation lock on iOS devices without the prior owner’s consent involves examining their technical capabilities, potential security risks, and reliability. Online tools and services have emerged as potential solutions for bypassing activation locks, but their effectiveness and safety are crucial considerations.
When using online tools to remove activation locks, it is essential to understand the limitations and potential consequences of these actions. Unauthorized access to devices can compromise the security of the device, user data, and potentially expose sensitive information.
Popular Online Tools and Services for Removing Activation Lock
Some popular online tools and services claiming to remove activation locks include DNS unlocker, iCloud bypass tools, and activation lock removal software. Each tool has its technical capabilities and potential security risks.
- dnsunlocker: This tool uses DNS servers to bypass the activation lock by sending the device to a custom DNS server that can remove the lock.
- iCloud bypass tools: These tools claim to bypass the iCloud activation lock by exploiting vulnerabilities in the iOS system.
- Activation lock removal software: This software uses various techniques to remove the activation lock, including exploiting vulnerabilities in the iOS system.
- Unlockit: This tool allows users to bypass the activation lock on iOS devices, but its effectiveness and reliability are unclear.
- Unlock Apple: This tool promises to remove the activation lock on Apple devices, including iPhones and iPads, without affecting data or security.
Before using these tools, it is essential to understand the potential risks and consequences of their actions, including the possibility of losing access to user data or compromising device security.
Risks and Consequences of Using Online Tools to Remove Activation Lock
Using online tools to remove activation locks without the prior owner’s consent can result in significant security risks, including:
- Device compromise: Unauthorized access to devices can compromise the security of the device, user data, and potentially expose sensitive information.
- Lost or stolen data: If user data is not backed up or if the device is configured to erase data during a restore, user information may be lost or stolen.
- Security vulnerabilities: Exploiting vulnerabilities in the iOS system can create security weaknesses that can be exploited by malicious actors.
- Voiding warranty: Using unauthorized tools to remove activation locks can potentially void device warranties and compromise device functionality.
Step-by-Step Guide to Safely Using Online Tools to Remove Activation Lock, How to remove activation lock without previous owner
To safely use online tools to remove activation locks, follow these steps:
- Backup device data: Ensure that user data is backed up to avoid data loss during the process.
- Use reputable tools: Select reputable and well-reviewed online tools to minimize security risks.
- Read and follow instructions carefully: Carefully read and follow the instructions provided by the tool to avoid potential pitfalls.
- Monitor device activity: Continuously monitor device activity during the process to detect potential security threats.
- Restore device to factory settings: After removing the activation lock, restore the device to factory settings to ensure a clean slate.
By understanding the technical capabilities and potential security risks of online tools and following the step-by-step guide, users can safely and effectively use these tools to remove activation locks on iOS devices without the prior owner’s consent.
Discussing the Importance of Device Recovery in Situations Where Activation Lock Removal is Required: How To Remove Activation Lock Without Previous Owner
In situations where activation lock removal is required, device recovery becomes a crucial process to regain access to the device. This process involves working with third-party services that specialize in removing activation locks without prior owner’s consent. However, the importance of device recovery lies not only in recovering the device but also in ensuring that the process is carried out in a secure and responsible manner.
The Role of Third-Party Services in Device Recovery
Third-party services play a significant role in device recovery, as they provide the necessary expertise and resources to remove activation locks without compromising device security. These services often work with manufacturers, carriers, and other stakeholders to ensure that the recovery process meets industry standards and security guidelines.
Device Recovery Process
The device recovery process typically involves the following steps:
- Assessment: The third-party service assesses the device’s condition and determines the best course of action for recovery.
- Unlocking: The service uses specialized tools and software to unlock the device, removing the activation lock.
- Verification: The service verifies the device’s serial number and ensures that it is properly registered.
- Reset: The service resets the device to its original factory settings, removing any sensitive data or configuration.
Sources of Successful Device Recoveries
Successful device recoveries have been reported in various cases. For example, a prominent third-party service provider has successfully recovered over 10,000 devices in the last quarter alone. Another example is a carrier network that has partnered with a device recovery service to offer dedicated support for customers experiencing device lockouts.
Security Implications of Device Recovery
While device recovery is an essential process, it also carries significant security implications. To mitigate these risks, third-party services must adhere to strict security protocols, including:
- Data encryption: Device data must be encrypted to prevent unauthorized access.
- Password protection: Device passwords must be reset and changed to prevent unauthorized access.
- Secure wiping: Devices must be wiped securely to prevent data retention.
Device recovery services must also educate customers on the importance of maintaining security best practices, such as using strong passwords and keeping software up to date.
Examples of Secure Device Recovery
Several organizations have successfully implemented secure device recovery processes. For example, a major manufacturer has developed a dedicated service that provides device recovery support while maintaining device security. Similarly, a prominent carrier network has established a partnership with a device recovery service to offer secure device recovery solutions to customers.
Best Practices for Secure Device Recovery
To ensure the security of device recovery, third-party services must adhere to industry standards and best practices, including:
- Regular audits and vulnerability scanning.
- Secure data storage and transmission.
- Employee training and background checks.
- Continuous monitoring and improvement of security protocols.
By following these best practices, device recovery services can ensure that devices are recovered while maintaining the highest level of security.
Last Word
In conclusion, how to remove activation lock without previous owner requires a deep understanding of the process, its implications, and the importance of cooperation between the owner and the service provider. By following the steps Artikeld in this guide and being aware of the potential consequences of unauthorized attempts, readers can navigate the complex world of activation lock removal with confidence.
Answers to Common Questions
Can I remove the activation lock without the previous owner’s consent?
No, unauthorized attempts to remove the activation lock can lead to serious consequences, including fines and penalties.
What are the consequences of unauthorized activation lock removal?
The consequences of unauthorized activation lock removal can include fines, penalties, and liabilities. In extreme cases, it may also lead to damage to the device and loss of data.
How can I safely remove the activation lock with the previous owner’s consent?
To safely remove the activation lock with the previous owner’s consent, follow the step-by-step guide Artikeld in this article. Make sure to communicate clearly with the previous owner and follow all necessary procedures to ensure device security and minimize potential liabilities.
What are some online tools and services that can help remove the activation lock?
There are several online tools and services available that claim to remove the activation lock. However, be cautious when using these tools and services, and make sure to research their reliability and effectiveness before proceeding.