How to clear card chip sets the stage for this important narrative, offering readers a glimpse into a story that is rich in detail and brimming with originality from the outset.
The secure removal of data from a payment card chip is a critical process that requires careful consideration, as not doing so can have serious consequences. Various methods exist for accessing the data stored on a payment card chip, including physical and digital approaches.
How to Remove Data from a Payment Card Chip Securely
Securely removing data from a payment card chip is crucial to protect your financial information from unauthorized access. Failure to do so can lead to identity theft, financial fraud, and other serious consequences. Payment card chips, such as EMV chips, store sensitive information like card numbers, expiration dates, and security codes. If not properly erased, this data can be accessed by malicious individuals, resulting in significant financial losses and damage to your credit history.
Methods for Accessing Data from a Payment Card Chip
There are several methods for accessing the data stored on a payment card chip, including physical and digital approaches.
Physical Methods
Physical methods involve using physical tools to access the data stored on a payment card chip. These methods can be divided into two categories: invasive and non-invasive.
- Invasive methods involve using a physical tool to physically access the chip’s memory and read the stored data. This can be done using specialized equipment like chip extractors or card skimmers.
- Non-invasive methods involve using a physical tool to read the data stored on the chip without physically accessing its memory. This can be done using a card reader or a chip scanner.
Digital Methods
Digital methods involve using software or online tools to access the data stored on a payment card chip. These methods can be divided into two categories: online and offline.
- Online methods involve using online tools or software to access the data stored on a payment card chip. This can be done using a computer or a mobile device.
- Offline methods involve using software or tools to access the data stored on a payment card chip without an internet connection. This can be done using a card reader or a chip scanner.
Consequences of Not Removing Data from a Payment Card Chip
Not removing data from a payment card chip can have serious consequences, including identity theft, financial fraud, and damage to your credit history.
- Identity theft: If your payment card chip’s data is not properly erased, it can be accessed by malicious individuals, resulting in identity theft.
- Financial fraud: If your payment card chip’s data is not properly erased, it can be used for financial transactions without your knowledge or consent, resulting in financial fraud.
- Damage to credit history: If your payment card chip’s data is not properly erased, it can result in negative marks on your credit history, making it difficult to obtain credit or loans in the future.
Best Practices for Removing Data from a Payment Card Chip
To remove data from a payment card chip securely, follow these best practices:
- Use a chip destroyer or a data eraser specifically designed for payment card chips.
- Follow the manufacturer’s instructions for using the chip destroyer or data eraser.
- Verify that the chip has been properly erased using a chip scanner or a card reader.
- Dispose of the payment card chip properly to prevent data recovery.
Precautions When Accessing Data from a Payment Card Chip
When accessing data from a payment card chip, take the following precautions to prevent data loss or theft:
- Use a chip scanner or a card reader that is specifically designed for payment card chips.
- Verify that the chip scanner or card reader is connected to a secure device or network.
- Use strong passwords or authentication to prevent unauthorized access to the data.
- Regularly update your software or tools to prevent known vulnerabilities.
“Removing data from a payment card chip is crucial to protect your financial information from unauthorized access.”
Designing a System to Erase or Clear Card Chip Data using Radio Frequency Identification (RFID) Technology
RFID technology has become increasingly popular in recent years, and its use in payment card chips is one of the areas of interest. However, accessing and erasing data from a payment card chip using RFID technology raises several concerns, including security risks and limitations.
The Principles of RFID Technology
RFID technology relies on the use of radio waves to communicate between a reader device and a tag, which is attached to the payment card chip. The reader device sends a signal to the tag, which responds with the stored data. In the context of payment card chips, RFID technology can be used to access and erase data from the chip. This is done by using a specific frequency to interact with the chip and delete the stored data.
-
RFID tags communicate with a reader device using radio waves.
This allows the device to access the data stored on the tag.
- The RFID technology uses a specific frequency to interact with the chip and delete the stored data.
- The use of RFID technology eliminates the need for direct physical contact with the chip, which can be advantageous in certain situations.
The Potential Risks and Limitations of Using RFID Technology
While RFID technology offers several advantages, it also raises several concerns, including security risks and limitations.
| RFID Technology Risks | RFID Technology Limitations |
|---|---|
| Data breach if RFID system is hacked. | Dependence on RFID reader device. |
In addition to these risks and limitations, the use of RFID technology for erasing data from payment card chips also raises questions about data security and the potential for unauthorized access. This is a complex issue that requires careful consideration and the implementation of robust security measures to mitigate these risks.
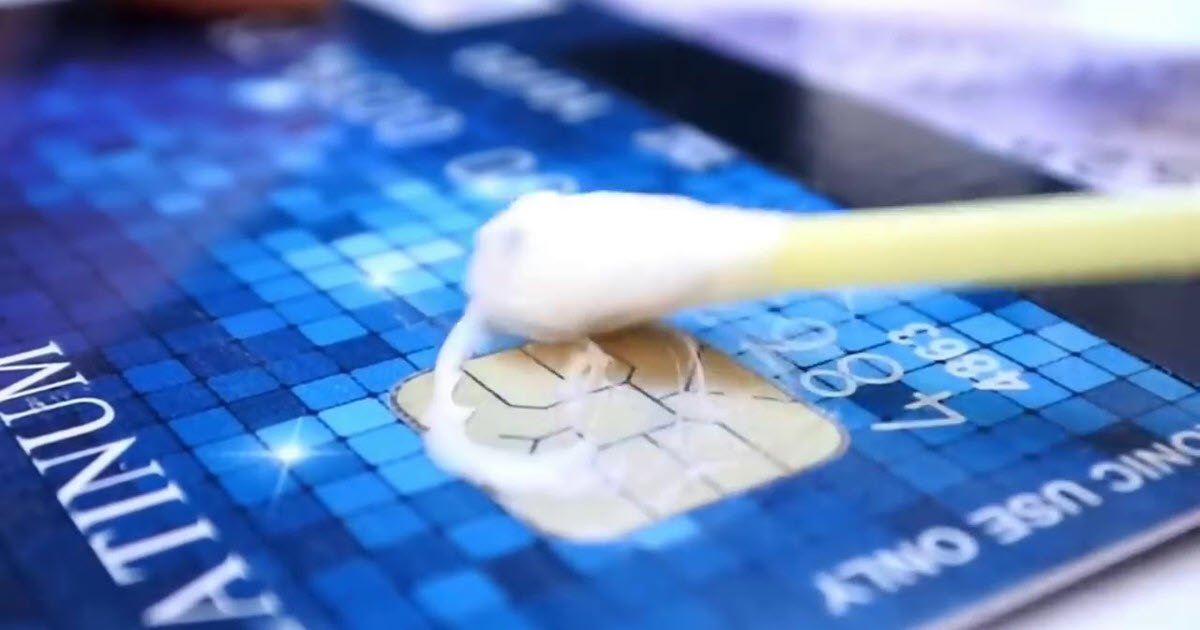
Create Tutorial on Manually Clearing Card Chip Data using Magnet or Physical Means: How To Clear Card Chip
Clearing card chip data manually can be a useful skill, especially when you need to erase sensitive information stored on your payment cards. However, this method is not without risks and consequences.
Risks and Consequences of Using Physical Means to Clear Card Chip Data
Using physical means to clear card chip data can result in damage to the card or chip itself. Applying heat or physical force to the card can cause the magnetic stripe to become demagnetized, making it unusable. Physical scratches or cracks in the card’s surface can also render it unusable or compromise its security.
Step-by-Step Guide to Clearing Card Chip Data using a Magnet
To clear card chip data using a magnet, follow these steps:
- Use a strong magnet to hold the card in place, making sure the magnetic stripe is exposed and facing the magnet.
- Move the magnet slowly and steadily along the magnetic stripe, applying gentle pressure.
- Repeat the process several times to ensure that the data is fully erased.
- After clearing the data, inspect the card for any signs of damage or wear.
However, using a magnet may not be effective in erasing sensitive information stored on modern payment cards, which often employ advanced security measures to protect their data.
Alternative Methods for Clearing Card Chip Data
If using a magnet does not erase the data, you can try other methods such as:
- Using a card chip eraser tool specifically designed for this purpose.
- Applying a strong magnetic field using an electromagnetic coil or a neodymium magnet.
- Using a UV light or other forms of radiation to erase the chip data.
Please note that these methods may not be 100% effective and may result in damage to the card or chip.
Comparing the Effectiveness of Different Methods for Clearing Card Chip Data
In the world of electronic payment systems, the security of card chip data is a top concern. With the rise of contactless transactions and mobile payments, the risk of data breaches and card skimming has increased. To mitigate these risks, various methods have been developed to clear card chip data safely and securely. In this article, we will compare and contrast the effectiveness of different methods for clearing card chip data, including software, hardware, and physical approaches.
One of the most common methods for clearing card chip data is using software solutions. These solutions typically involve reinstalling the operating system or formatting the card’s chip. However, this approach has its limitations, as it may not completely erase sensitive data, and it may also require technical expertise.
Software Solutions
Software solutions for clearing card chip data include:
- In-place deletion: This method uses software to erase data on the card’s chip without overwriting it.
- Formatting: This method involves reformatting the chip, effectively deleting all data.
- Reinstallation: This method involves reinstalling the operating system or software on the card’s chip.
However, software solutions may not completely erase sensitive data, and they may also require technical expertise. For example, some software solutions may only delete visible data, leaving sensitive information intact.
Hardware solutions offer a more effective way to clear card chip data, as they physically remove the data from the card’s chip. However, these solutions can be more expensive and may require specialized equipment.
Hardware Solutions
Hardware solutions for clearing card chip data include:
- Card shredders: These devices physically shred the card’s chip, making it impossible to recover any data.
- Chip destroyer: This device uses a combination of heat and chemicals to destroy the card’s chip.
- Physical destruction: This method involves physically destroying the card’s chip using specialized equipment.
Hardware solutions are effective in clearing card chip data, but they can be more expensive and may require specialized equipment.
Physical means offer a simple and cost-effective way to clear card chip data. However, they may not be as effective as software or hardware solutions, and they can also damage the card’s chip.
Physical Means
Physical means for clearing card chip data include:
- Magnetization: This method uses a strong magnet to demagnetize the card’s chip, making it impossible to recover any data.
- Physical scrubbing: This method involves using physical scrubbing tools to remove sensitive data from the card’s chip.
- Shredding: This method involves physically shredding the card’s chip, making it impossible to recover any data.
Physical means are simple and cost-effective, but they may not be as effective as software or hardware solutions, and they can also damage the card’s chip.
When choosing a method for clearing card chip data, consider the level of security required and the type of data being stored. Hardware solutions offer the highest level of security, but they can be more expensive and may require specialized equipment. Software solutions are more cost-effective, but they may not completely erase sensitive data. Physical means offer a simple and cost-effective solution, but they may not be as effective as software or hardware solutions.
“The most effective way to clear card chip data is to use a combination of software and hardware solutions to physically remove the data from the card’s chip.”
Developing a procedure for securely clearing card chip data in different scenarios, such as after a transaction or when a card is no longer in use
Clearing card chip data is a crucial process that ensures the security and privacy of sensitive information. In various scenarios, card chip data must be securely erased to prevent unauthorized access or misuse. This process involves different procedures depending on the situation, including after a transaction or when a card is no longer in use. Implementing a secure clearing procedure in these scenarios is vital to protect cardholders’ data and maintain trust in the payment system.
### After a Transaction
Securing card chip data after a transaction is essential to prevent unauthorized access. This can be achieved through a secure clearing process that ensures the data is properly erased.
* Step 1: Notification: The merchant or payment processor must notify the cardholder of the transaction within a reasonable timeframe, usually within 24 hours, as per the Payment Card Industry Data Security Standard (PCI DSS) guidelines.
* Step 2: Data Erasure: The card chip data must be securely erased from the point of sale (POS) terminal, and the merchant or payment processor must provide evidence of data erasure.
* Step 3: Verification: The cardholder must verify that the data has been erased and confirm receipt of the notification.
### When a Card is No Longer in Use
Clearing card chip data when a card is no longer in use is essential to prevent unauthorized transactions. This can be achieved through a process that securely erases the data.
* Step 1: Notification: The cardholder must notify their bank or card issuer that the card is no longer in use.
* Step 2: Data Erasure: The card issuer must securely erase the card chip data from their systems and provide evidence of data erasure.
* Step 3: Verification: The cardholder must verify that the data has been erased and confirm receipt of the notification.
### Best Practices
To ensure secure data erasure, card issuers and merchants must implement best practices, such as:
* Regular Security Audits: Regular security audits to identify vulnerabilities and ensure compliance with PCI DSS guidelines.
* Secure Data Storage: Secure storage of card chip data to prevent unauthorized access.
* Data Erasure: Secure data erasure processes must be implemented to ensure data is properly erased.
Identifying Potential Risks and Vulnerabilities in Current Card Chip Data Clearing Systems and Proposing Potential Solutions

Current card chip data clearing systems are designed to securely erase sensitive information from payment cards. However, these systems are not infallible, and vulnerabilities can potentially allow malicious actors to access or manipulate card data. Understanding these risks and proposing solutions to mitigate them is essential to maintaining the security and integrity of card transactions.
Risks of Data Tampering and Unauthorized Access
Data tampering and unauthorized access are significant risks associated with current card chip data clearing systems. These risks can arise from various sources, including compromised security protocols, software vulnerabilities, and human error.
According to a study by the Payment Card Industry Security Standards Council (PCI SSC), the most common causes of data breaches are: 1) weak passwords (43%), 2) phishing attacks (29%), and 3) malware infections (20%).
Examples of Data Tampering and Unauthorized Access
Several high-profile incidents have highlighted the risks of data tampering and unauthorized access. These include:
- The 2013 Target Corporation data breach, which compromised the credit card information of over 40 million customers.
- The 2017 Equifax data breach, which exposed the sensitive information of over 147 million consumers, including credit card numbers and expiration dates.
- The 2019 Home Depot data breach, which compromised the payment card information of over 50 million customers.
Solution: Implementing Advanced Security Protocols and Regular Penetration Testing
To mitigate the risks of data tampering and unauthorized access, card issuers and payment processors can implement advanced security protocols and regular penetration testing. This includes:
- Using end-to-end encryption to protect card data in transit.
- Implementing two-factor authentication to verify cardholder identity.
- Conducting regular penetration testing to identify and remediate security vulnerabilities.
By implementing these measures, card issuers and payment processors can significantly reduce the risk of data tampering and unauthorized access, ensuring the security and integrity of card transactions.
Risks of Card Chip Data Corruption
Card chip data corruption can occur when sensitive information is stored or transmitted in an improper format. This can lead to transaction errors, declined payments, and compromised data security.
Examples of Card Chip Data Corruption
Several factors can contribute to card chip data corruption, including:
- Hardware or software malfunctions during the card personalization process.
- Incorrect formatting of card data during transmission or storage.
- Failed data validation checks during payment processing.
Solution: Improving Data Formatting and Validation
To mitigate the risks of card chip data corruption, payment processors and card issuers can improve data formatting and validation processes. This includes:
- Implementing standardized data formatting protocols during card personalization.
- Conducting rigorous data validation checks during transmission and storage.
- Ensuring that payments processing systems can recover from data transmission errors.
By implementing these measures, card issuers and payment processors can minimize the risk of card chip data corruption and ensure smooth, secure transactions.
Risks of Card Chip Data Exposure
Card chip data exposure can occur when sensitive information is stored or transmitted in plain text or an easily decipherable format. This can compromise cardholder data security and lead to identity theft or financial loss.
Examples of Card Chip Data Exposure
Several factors can contribute to card chip data exposure, including:
- Breach of card issuer or payment processor databases containing sensitive information.
- Unprotected data transmission or storage practices.
- Use of weak encryption or cryptographic keys.
Solution: Implementing Robust Data Encryption and Secure Storage
To mitigate the risks of card chip data exposure, card issuers and payment processors can implement robust data encryption and secure storage practices. This includes:
- Using advanced encryption algorithms to protect card data in storage and transmission.
- Implementing secure data storage practices, such as access controls and data masking.
- Ensuring the use of secure cryptographic keys and protocols.
By implementing these measures, card issuers and payment processors can protect cardholder data security and minimize the risk of identity theft or financial loss.
Conclusion
Current card chip data clearing systems are vulnerable to various risks, including data tampering, unauthorized access, corruption, and exposure. Implementing advanced security protocols, regular penetration testing, and robust data encryption can mitigate these risks and ensure secure card transactions. By improving data formatting, validation, and storage practices, card issuers and payment processors can minimize errors and data breaches.
Creating a list of best practices for securely clearing card chip data, including guidelines for individuals and businesses
In today’s digital age, payment card security is more crucial than ever. With the rise of contactless payments and mobile wallets, the risk of card chip data breaches has increased significantly. To mitigate this risk, it is essential to establish a set of best practices for securely clearing card chip data.
Establishing Secure Data Erasure Procedures
Secure data erasure procedures are the foundation of card chip data clearing. These procedures ensure that sensitive information is deleted permanently, rendering it unrecoverable. To establish secure data erasure procedures, businesses and individuals should follow these guidelines:
- Use reputable data destruction software: Utilize industry-recognized data destruction software to ensure that card chip data is deleted securely.
- Verify data erasure: Conduct regular verifications to ensure that card chip data has been deleted permanently.
- Document procedures: Maintain detailed records of data erasure procedures to ensure compliance with regulatory requirements.
- Train staff: Educate employees on the importance of secure data erasure and the procedures in place to ensure compliance.
Ensuring Secure Disposal of Physical Cards
When physical cards are no longer in use, they pose a significant risk to card chip data security. To mitigate this risk, businesses and individuals should follow these guidelines:
- Shred cards: Physically shred cards to prevent unauthorized access to sensitive information.
- Burn cards: Burn cards in a secure environment to ensure complete destruction of sensitive information.
- Use secure destruction facilities: Utilize reputable destruction facilities to ensure that cards are destroyed securely.
- Document destruction: Maintain records of card destruction to ensure compliance with regulatory requirements.
Regularly Updating Software and Firmware
Regular software and firmware updates are essential to prevent vulnerabilities that could compromise card chip data security. To stay up-to-date, businesses and individuals should follow these guidelines:
- Monitor vendor updates: Regularly check with vendors for software and firmware updates.
- Apply updates promptly: Immediately apply updates to prevent vulnerabilities from being exploited.
- Test updates: Conduct thorough testing to ensure that updates do not introduce new vulnerabilities.
Avoiding Malicious File Transfer
Malicious file transfer can compromise card chip data security in several ways, including malware and Trojan horse attacks. To prevent malicious file transfer, businesses and individuals should follow these guidelines:
- Use reputable file transfer services: Utilize industry-recognized file transfer services to ensure secure data transfer.
- Verify file integrity: Regularly verify file integrity to ensure that sensitive information is not compromised during transfer.
- Use encryption: Encrypt sensitive information during transfer to prevent unauthorized access.
Implementing Card Chip Data Security Measures
To prevent unauthorized access to card chip data, businesses and individuals should implement robust security measures. These measures include:
- Two-factor authentication: Implement two-factor authentication to ensure that only authorized individuals can access card chip data.
- Encryption: Encrypt card chip data to prevent unauthorized access.
- Access controls: Implement robust access controls to restrict access to card chip data.
In conclusion, establishing secure card chip data clearing procedures requires a comprehensive approach that addresses multiple aspects of security. By following these best practices, businesses and individuals can ensure that card chip data is securely cleared and prevent potential breaches.
Explaining how to clear card chip data using card reader devices or specialized software
Card chip data clearing is an essential process to ensure the security and integrity of payment card transactions. Card reader devices and specialized software are two effective methods used for clearing card chip data, providing a convenient and efficient solution for card issuers and acquirers.
Principles of Card Reader Devices and Specialized Software, How to clear card chip
Card reader devices and specialized software work on the principle of manipulating the card chip’s magnetic stripe or electronic chip to erase the stored data. This process involves rewriting the card chip with new data, effectively replacing the original information and securing the card.
Cards Reader Devices
Card reader devices are designed to erase card chip data by using a combination of magnetic and electrical signals. These devices are typically used by card issuers to securely destroy sensitive information on cards that are no longer in use or have been replaced.
- When a card is inserted into the reader device, the device sends a signal that disrupts the magnetic stripe, causing the stored data to be erased.
- The device then writes new data onto the card chip, replacing the original information.
Specialized Software
Specialized software is another effective method for clearing card chip data. This software is designed to work with card reader devices to securely erase sensitive information from cards.
- The software provides an easy-to-use interface for card issuers to select the cards to be erased.
- It also provides options for setting security protocols and reporting functions to ensure data integrity and compliance with regulatory requirements.
Benefits and Limitations of Using Card Reader Devices and Specialized Software
Using card reader devices and specialized software for clearing card chip data offers several benefits, including quick and accurate data erasure, easy-to-use interfaces, and security features to prevent unauthorized access. However, these methods also have their limitations, such as the need for specialized equipment and software, and the potential for technical malfunctions.
Card Reader Devices
One of the limitations of using card reader devices is the cost associated with purchasing and maintaining these devices. Additionally, there is a risk of technical malfunctions, which can cause data corruption or loss.
- Despite these limitations, card reader devices remain a popular choice for card issuers due to their convenience and efficiency.
- Many card issuers choose to invest in card reader devices as part of their overall security strategy to protect sensitive information.
Specialized Software
Another limitation of using specialized software is the potential risk of data breach due to software vulnerabilities. However, reputable software providers have implemented robust security measures and encryption algorithms to prevent unauthorized access.
- Regular software updates and patches are also available to address any security vulnerabilities.
- Additionally, many software providers offer customer support and training to ensure users can effectively use the software.
Final Conclusion
Clearing card chip data is a multifaceted process that requires a comprehensive understanding of the various methods available. By following the guidelines Artikeld in this narrative, readers can ensure the secure removal of data from their payment card chips.
Query Resolution
Q: Can I use a magnet to clear card chip data?
A: While a magnet can affect the data stored on a payment card chip, it is not a reliable or recommended method for clearing card chip data, as it can cause damage to the chip.
Q: Are there any risks associated with using radio frequency identification (RFID) technology to clear card chip data?
A: Yes, there are risks associated with using RFID technology to clear card chip data, including data breaches if the system is hacked and dependence on a RFID reader device.
Q: Can I clear card chip data using specialized software?
A: Yes, specialized software can be used to clear card chip data, and it often provides an easy-to-use interface for doing so.
Q: Is it possible to clear card chip data manually?
A: Yes, it is possible to clear card chip data manually using a magnet or other physical means, but this can be a risky and unreliable method.
Q: What are the consequences of not regularly clearing and updating card chip data?
A: The consequences of not regularly clearing and updating card chip data can include data breaches, compromised security, and other serious issues.