Kicking off with how to call anonymously, this guide is designed to captivate and engage readers as we explore the fascinating world of anonymous communication. We will delve into the concept of anonymity in today’s digital landscape, its importance in modern communication, and the various forms it takes. By understanding these aspects, we can grasp the motivations behind individuals making anonymous calls, as well as the technical aspects of achieving anonymity in phone calls.
From the benefits and risks of anonymity to the role of social media in creating a culture of anonymity, we will cover it all. We will examine the primary motivations behind individuals making anonymous calls, discuss the impact of social media on relationships and self-expression, and share case studies of people who have successfully used anonymous calls to achieve their goals.
Understanding Anonymity and Its Implications
In today’s digital landscape, anonymity has become a crucial aspect of modern communication. With the rise of the internet and social media, individuals have the ability to connect with others across the globe, share their thoughts and ideas, and access a vast amount of information. However, with this increased connectivity comes the risk of surveillance, harassment, and censorship. Anonymity provides a means for individuals to communicate freely without fear of retribution or persecution, allowing them to express themselves truly and without restraint.
Anonymity takes many forms, including phone calls, messaging apps, and online interactions. When using anonymous communication tools, individuals can share their thoughts and ideas without revealing their personal identity. This has many benefits, including:
– Protection from harassment and bullying
– Freedom to express oneself without fear of retribution
– Ability to participate in online communities without revealing one’s identity
– Safety from online predators and scammers
However, anonymous communication also comes with risks, including:
– Lack of accountability for one’s actions
– Increased risk of spam and unwanted messages
– Difficulty in verifying the authenticity of information
– Potential for malicious actors to use anonymity for nefarious purposes
Forms of Anonymity
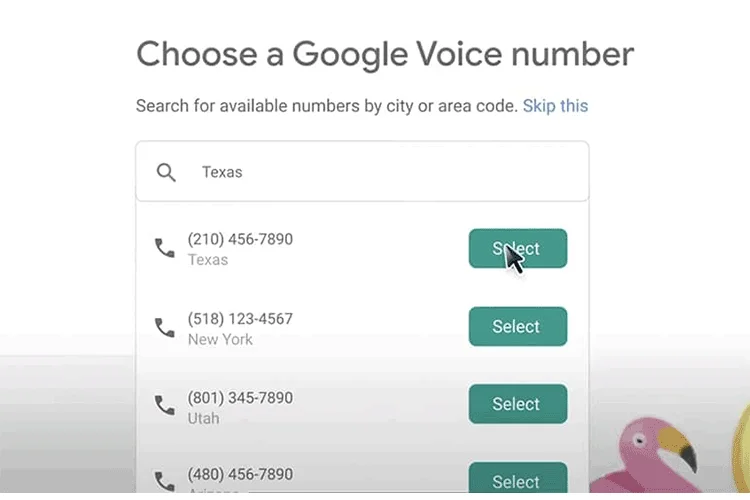
Phone calls are one of the most common forms of anonymous communication. With the rise of VoIP (Voice over Internet Protocol) technology, individuals can make phone calls over the internet using services like Skype and Google Voice. This allows users to make calls without revealing their phone number or location.
Messaging apps like WhatsApp and Signal also offer end-to-end encryption, allowing users to communicate securely and anonymously. These apps use encryption to scramble messages, making it difficult for third-parties to intercept and read them.
Online interactions, such as forums and social media platforms, also offer a level of anonymity. Users can create pseudonyms and engage in discussions without revealing their personal identity. However, this anonymity can also be used by malicious actors to spread disinformation and propaganda.
Situations Where Anonymity is Crucial
Whistleblowing is one situation where anonymity is crucial. Whistleblowers are individuals who report wrongdoing or corruption within an organization. By using anonymous communication tools, whistleblowers can reveal sensitive information without fear of retribution or persecution.
For example, Edward Snowden, a former CIA employee, used anonymous communication tools to leak classified documents about the NSA’s surveillance program. Snowden’s revelations exposed widespread surveillance and sparked a global debate about government secrecy and accountability.
Another situation where anonymity is crucial is in escaping from harassment. Online harassment, such as cyberbullying and online stalking, can have serious consequences for individuals. By using anonymous communication tools, victims can communicate with others without fear of being identified and targeted.
For instance, the Tor Project, a non-profit organization, provides a secure and anonymous way for individuals to communicate online. The Tor network uses encryption and routing techniques to make it difficult for third-parties to track users’ online activity.
Benefits and Risks Comparison Table
| Feature | Anonymous Calls | Messaging Apps | Online Interactions | Whistleblowing | Escaping Harassment |
| — | — | — | — | — | — |
| Benefits | Protects personal identity, allows for free expression, and provides safety from harassment | Provides end-to-end encryption, allows for secure communication, and offers a way to participate in online communities | Offers a way to engage in discussions, connect with others, and access information | Allows for the reporting of wrongdoing, promotes accountability, and protects whistleblowers | Provides a way to communicate safely, escape harassment, and protect personal identity |
| Risks | Lack of accountability, increased risk of spam, and difficulty in verifying authenticity | Lack of accountability, increased risk of spam, and difficulty in verifying authenticity | Increased risk of harassment, difficulty in verifying authenticity, and potential for malicious actors to spread disinformation | Potential for retribution, difficulty in verifying authenticity, and potential for malicious actors to target whistleblowers | Potential for backlash, difficulty in verifying authenticity, and potential for malicious actors to target victims |
| Security Measures | Encryption, secure routing, and pseudonyms | Encryption, secure routing, and end-to-end encryption | Encryption, secure routing, and pseudonyms | Encryption, secure routing, and pseudonyms | Encryption, secure routing, and pseudonyms |
In conclusion, anonymity is a crucial aspect of modern communication, providing individuals with the freedom to express themselves without fear of retribution or persecution. However, anonymity also comes with risks, such as lack of accountability and difficulty in verifying authenticity. By understanding the benefits and risks of anonymous communication, individuals can use these tools effectively and securely.
Reasons Why People Prefer Anonymous Calls
In today’s digital age, anonymity has become an increasingly desirable trait, with many people seeking to make anonymous calls for various reasons. This trend is not unique to personal affairs but has also infiltrated professional and emergency situations.
People may prefer anonymous calls for several reasons. Firstly, they may want to maintain their anonymity in matters related to business or personal relationships, such as resolving conflicts or negotiating sensitive deals. Anonymous calls can also be useful in emergency situations where the individual’s identity needs to be protected, such as reporting a crime or seeking assistance without disclosing their location.
Role of Social Media in Creating a Culture of Anonymity
The rise of social media has significantly contributed to the culture of anonymity. Platforms like Facebook and Twitter enable users to create anonymous profiles, share thoughts and opinions without revealing their identities. This phenomenon has far-reaching implications for relationships, self-expression, and online interactions. Social media can create a false sense of security, leading individuals to share personal information or engage in online behavior that they might not otherwise exhibit in real life. This can result in the erosion of meaningful relationships and the blurring of boundaries between public and private spheres.
Case Studies of Successful Anonymous Calls
Several case studies illustrate the effectiveness of anonymous calls in achieving desired outcomes. For instance, a whistleblower who remains anonymous has exposed corporate corruption, leading to significant reforms and financial penalties. Another case involves a woman who made an anonymous call to report domestic violence, receiving immediate support and protection. These examples demonstrate the potential benefits of anonymous calls in resolving conflicts, seeking help, or exposing wrongdoing.
Common Reasons for Anonymous Calls
Several common reasons drive individuals to make anonymous calls. These include:
- Personal safety: anonymous calls can be used to report crimes or seek assistance without disclosing one’s location.
- Professional purposes: anonymous calls can be used to negotiate sensitive deals or resolve conflicts without compromising one’s identity.
- Harassment or abuse: anonymous calls can be used to report harassment or abuse, providing a safe and confidential means of seeking help.
- Whistleblowing: anonymous calls can be used to expose corporate corruption or other forms of wrongdoing without risking retaliation.
- Emergency situations: anonymous calls can be used to report emergencies, such as fires or medical emergencies, without disclosing one’s location.
In conclusion, anonymous calls have become an increasingly common phenomenon, driven by various reasons, including personal, professional, and emergency situations. As technology continues to advance, the desire for anonymity is likely to persist, presenting both opportunities and challenges for individuals, organizations, and society at large.
Security Concerns and Risks
Anonymous calls can pose significant security risks, primarily due to the lack of verifiable caller identification. This ambiguity can expose individuals to malicious activities, including interception, spoofing, and identity theft.
Interception Risks
Interception occurs when an unauthorized third party accesses a caller’s communication, potentially disrupting or manipulating the conversation. This can happen through various means, such as hacking vulnerabilities in communication networks or intercepting communication streams. Interception can compromise sensitive information, including personal data, business secrets, or confidential discussions.
Spoofing Risks
Spoofing involves impersonating someone else’s identity to deceive others. In the context of anonymous calls, spoofing can occur when an individual masquerades as a trusted party, such as a government agency or a well-established organization. Spoofing can create false impressions, potentially leading to unauthorized access to sensitive information, financial transactions, or even physical locations.
Identity Theft Risks, How to call anonymously
Identity theft occurs when an unauthorized party assumes another person’s identity for malicious purposes. Anonymous calls can facilitate identity theft by making it challenging to verify the caller’s identity. This vulnerability can lead to various forms of exploitation, including financial fraud, theft of confidential information, or even targeted harassment.
Measures for Identity and Confidentiality Protection
To protect one’s identity and confidentiality during anonymous calls, several measures can be taken:
- Encryption: Utilize end-to-end encryption protocols to secure communication streams. This ensures that information remains inaccessible to unauthorized parties.
- Secure Communication Protocols: Implement secure communication protocols, such as secure VoIP (Voice over Internet Protocol) or encrypted SMS. These protocols safeguard communication streams against interception and eavesdropping.
- Trusted Intermediaries: Utilize trusted intermediaries, such as secure communication platforms or encrypted VoIP services, to mitigate risks associated with anonymous calls.
- Data Protection: Implement robust data protection measures, including password protection, secure data storage, and access controls, to safeguard sensitive information.
These measures can significantly reduce the risk of interception, spoofing, and identity theft associated with anonymous calls.
Strategies for Mitigating Risks
To mitigate the risks associated with anonymous calls, consider the following strategies:
- Secure VPN: Utilize a secure Virtual Private Network (VPN) to encrypt communication streams and protect one’s identity.
- Trusted Intermediaries: Engage with trusted intermediaries, such as secure communication platforms or encrypted VoIP services, to ensure confidentiality and authenticity.
- Access Controls: Implement robust access controls, including authentication and authorization mechanisms, to limit access to sensitive information.
- Data Encryption: Utilize end-to-end encryption protocols to safeguard communication streams against interception and eavesdropping.
By leveraging these strategies, individuals can reduce the risks associated with anonymous calls and protect their sensitive information.
Data Protection and Confidentiality
Data protection and confidentiality are critical concerns in the context of anonymous calls. The importance of safeguarding sensitive information cannot be overstated. In this context, compare different approaches to protecting sensitive information:
| Approach | Benefits | Challenges |
|---|---|---|
| Encryption | Provides robust protection against interception and eavesdropping. | May require significant technical expertise to implement and manage. |
| Secure Communication Protocols | Ensures confidentiality and authenticity through secure communication streams. | May require additional infrastructure or resources to implement. |
| Trusted Intermediaries | Provides an additional layer of security through trusted intermediaries. | May introduce dependencies on third-party services, increasing vulnerability. |
Each approach has its strengths and weaknesses, and selecting the most effective solution depends on individual circumstances and requirements. Ultimately, a combination of measures is often the most effective way to ensure data protection and confidentiality in the context of anonymous calls.
Closing Summary: How To Call Anonymously
In conclusion, understanding how to call anonymously is crucial in today’s digital age. By grasping the concept of anonymity, its importance, and the various forms it takes, we can navigate the complexities of anonymous communication safely and securely. Whether it’s for personal, professional, or emergency situations, our guide has provided you with the knowledge and tools to make informed decisions and avoid potential risks.
Expert Answers
Q: What are the primary motivations behind individuals making anonymous calls?
Individuals make anonymous calls for personal reasons, such as seeking help or resolving conflicts, professional reasons, such as conducting market research or resolving business disputes, or emergency situations, such as escaping harassment or reporting a crime.
Q: How can I protect my identity and confidentiality during an anonymous call?
You can protect your identity and confidentiality during an anonymous call by using encryption, secure communication protocols, and a trusted intermediary. It’s also essential to be aware of the potential risks, such as interception, spoofing, and identity theft.
Q: What are the risks associated with anonymous calls?
The risks associated with anonymous calls include interception, spoofing, identity theft, and being traced or identified. It’s crucial to take measures to mitigate these risks, such as using a secure VPN, a trusted intermediary, or encryption technologies.
Q: Can I make an anonymous call using a VPN?
Yes, you can make an anonymous call using a VPN (Virtual Private Network). A VPN creates a secure and encrypted connection between your device and the internet, making it difficult for others to intercept or track your communication.
Q: What are the benefits of anonymity in communication?
The benefits of anonymity in communication include increased freedom of expression, reduced risk of harassment or backlash, improved safety and security, and enhanced confidentiality and discretion.