As how to check fake ids takes center stage, this guide will walk you through the essential steps to verify the authenticity of identification documents, helping you make informed decisions and stay within the law. From recognizing characteristic traits to using ID scanning technology, we will cover it all.
Understand the Risks and Consequences of Using Fake IDs, Identifying Characteristics of Genuine IDs, Common Methods Used by Scammers, Recognizing and Addressing Signs of Potential Fakes, and so much more.
Identifying Characteristics of Genuine IDs and Their Counterparts: How To Check Fake Ids
Physical attributes of genuine IDs and counterfeit documents can be telling. While counterfeiters may be able to replicate some security features, genuine documents contain numerous characteristics that make them difficult to fake.
In comparing the physical attributes of authentic documents to their fake counterparts, we notice the presence of precise and intricate security features that are often missing from fakes. For instance, genuine ID cards tend to have raised or textured elements, such as embossing or hot-stamping, which provide tactile feedback. Counterfeiters may lack the expertise and equipment necessary to replicate these features accurately.
The methods used to create convincing counterfeit documents often rely on printing and hologram techniques. Counterfeiters can use high-quality printers to print images or text that closely resemble genuine documents, and they can also apply holographic foil to mimic the holograms present in authentic documents. However, these methods have their limitations, and the quality of the counterfeit document can vary widely.
Types of Printing Techniques Used in ID Counterfeiting
Printing techniques play a crucial role in ID counterfeiting, with the aim being to produce high-quality images that closely resemble genuine documents. The following are some of the most common printing techniques used by counterfeiters:
- Offset printing: This is a high-volume printing technique that involves transferring ink from a plate to a sheet of paper. Counterfeiters can use offset printing to produce high-quality images that are difficult to distinguish from genuine documents.
- Digital printing: This is a high-speed printing technique that involves printing directly onto the paper. Digital printing allows counterfeiters to produce high-quality images quickly and at a lower cost.
- Silk screening: This is a manual printing technique that involves applying ink or paint to a surface using a screen. Silk screening can be used to produce high-quality images, but it is a time-consuming process.
Hologram Techniques Used in ID Counterfeiting
Holograms are used in many ID documents, including passports and driver’s licenses, to provide an additional layer of security. Counterfeiters have developed various techniques to replicate holograms, including:
- Hologram foil: This involves applying a thin layer of holographic foil to the surface of the document. Counterfeiters can use a variety of techniques, including hot-stamping or UV printing, to apply the hologram foil.
- Laser engraving: This involves using a laser to engrave a hologram onto the surface of the document. Laser engraving can produce high-quality holograms that are difficult to distinguish from genuine documents.
Common Items That Can Help Determine Document Validity
Genuine ID documents contain numerous characteristics that can help determine their validity. Some of the most common items that can help determine document validity include:
- Raised or textured elements, such as embossing or hot-stamping
- Holograms or hologram foil
- Security threads or striping
- UV printing or ink
- Laser engraving or microprinting
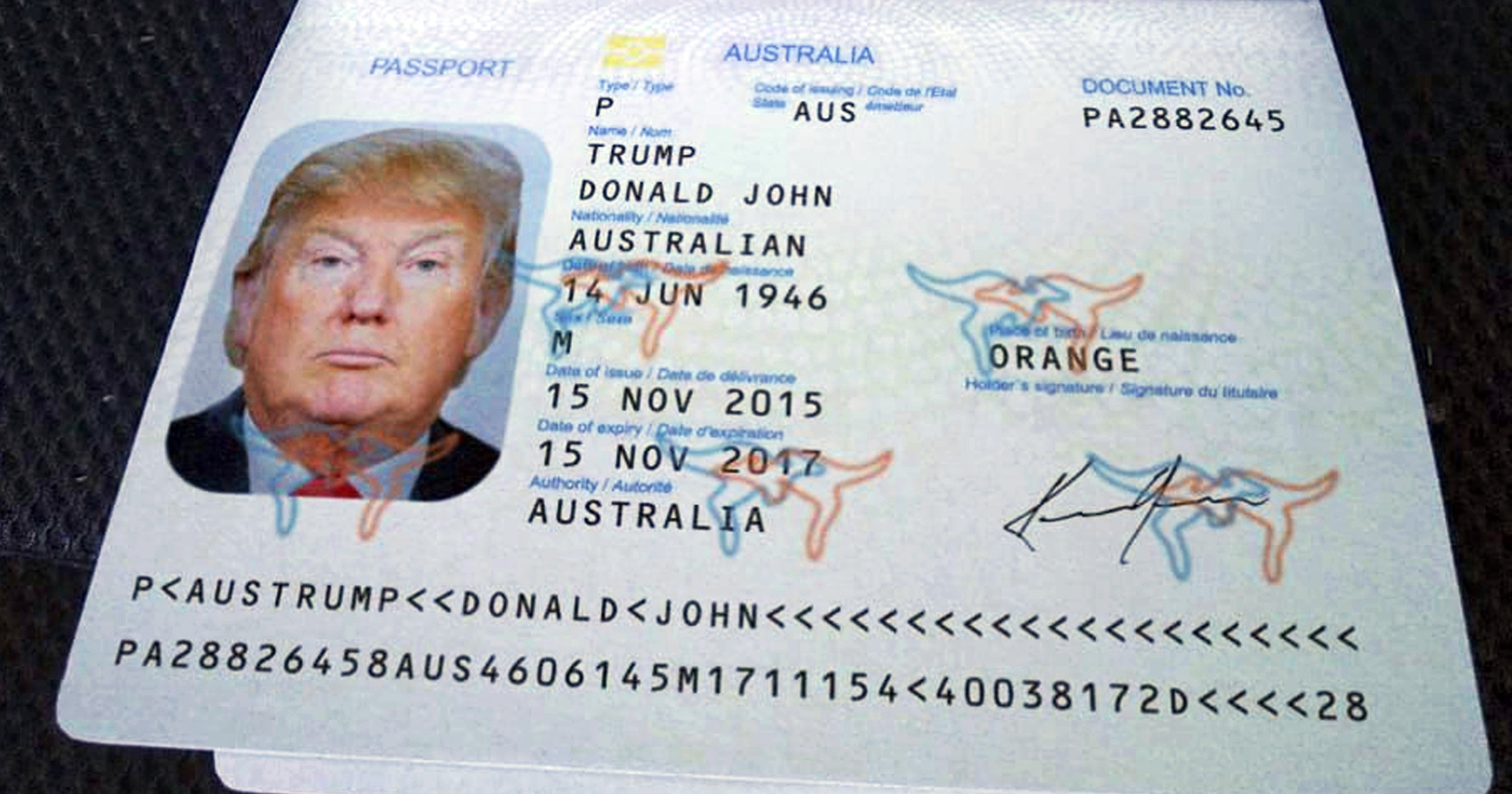
Image of a Genuine ID Document
A genuine ID document, such as a driver’s license, typically features a photograph of the individual whose identity is being verified. The photograph is usually accompanied by various security features, such as a raised or textured surface, holograms, or UV printing. The document also typically includes information such as the individual’s name, date of birth, and address.
In a genuine ID document, the photograph and security features are typically of high quality and are carefully integrated into the design of the document. The document may also include additional features, such as a hologram or a security thread, to further enhance its security.
Differences Between Genuine and Counterfeit Documents
While counterfeiters may be able to replicate some of the security features present in genuine documents, there are usually significant differences between the two. Some of the differences that can be used to distinguish genuine from counterfeit documents include:
- Differences in paper quality or texture
- Differences in the quality or accuracy of the photograph
- Differences in the quality or accuracy of the security features
- Differences in the design or layout of the document
By examining the physical attributes and security features of a document, it is often possible to determine whether it is genuine or counterfeit. This can be done through a variety of methods, including visual inspection, chemical testing, or the use of specialized equipment.
Common Methods Used by Scammers to Create Fake IDs
Creating fake IDs has become a sophisticated business, with scammers utilizing various techniques to create convincing documents. These methods range from using software and scanning techniques to manipulate photographs and alter existing documents. In this section, we will delve into the common methods used by scammers to create fake IDs.
Digital Copy Creation Techniques
Scammers use high-quality software and scanning methods to create digital copies of identification cards. Advanced graphics editors, such as Adobe Photoshop, are used to manipulate images and alter the format of the documents. Some scammers also employ software designed specifically for creating fake IDs, like AI-powered tools that can generate realistic images and text. These programs often come with built-in templates for various types of identification documents, making it easier for scammers to create convincing forgeries.
Photograph Manipulation
To replace existing images with new ones in identification documents, scammers use techniques like photo editing software. They can alter the facial features, eyes, hair, or any other identifiable characteristics to create a new identity or make an existing one appear different. For instance, scammers might use image manipulation software to superimpose a person’s face onto a completely different background, or even use facial recognition technology to create a fake ID with the correct facial features. In addition, scammers can swap the photo on a driver’s license or passport with a real photo of another person’s, making it challenging to detect identity theft.
Document Alteration Techniques
To make fake IDs appear more convincing, scammers alter existing documents to make them seem real. This can include adding security features, such as holograms, watermarks, or microprinting, to the fake IDs. Scammers also modify the formatting and layout of the documents to match the legitimate version. In some cases, scammers even use specialized paper and printing techniques to create IDs that look and feel like the real thing. By tampering with the paper texture, size, and color scheme, scammers can create convincing forgeries that are impossible to distinguish from genuine IDs.
Software-Based ID Creation Tools
Scammers also use software-based tools to create fake IDs. These tools often come with pre-built templates for various types of identification documents, such as driver’s licenses, passports, or state IDs. Some popular software-based ID creation tools include ID card designer, CardPresso, and ID Card Studio. These tools allow scammers to create professional-looking ID cards with just a few clicks, making high-quality counterfeits more accessible than ever.
Other Methods
In addition to the methods mentioned above, scammers also use other methods to create fake IDs, such as:
- 3D printing to create ID cards with raised text or images
- Printing fake holograms or watermarks
- Using advanced materials, such as UV-printing or metallic ink
- Creating fake IDs using 3D modeling software
These methods allow scammers to create fake IDs with advanced security features, making it even harder to detect authenticity.
Understanding the Importance of Verification and the Role of ID Scanning Technology
Proper verification of identification is essential in environments where age-restricted products and services are offered. This process helps prevent underage access to these products and services, ensuring compliance with relevant laws and regulations. ID scanning technology plays a vital role in this verification process, providing businesses with a secure and efficient method for authenticating identification documents.
Methods of Verification
Businesses use several methods to verify identification, each with its own advantages and limitations. These methods include:
- Visual inspection: This involves manually reviewing the identification document for authenticity, expiration dates, and other relevant information. However, this method can be time-consuming and prone to human error.
- Electronic scanning: This method uses specialized scanners to electronically capture and verify the information on identification documents. Electronic scanning provides a more efficient and accurate verification process than visual inspection.
- Infrared scanning: This method uses infrared light to detect any alterations or counterfeiting on identification documents. Infrared scanning provides an additional layer of security, helping to prevent forgery and identity theft.
Advantages of ID Scanning Technology
ID scanning technology offers several advantages over traditional verification methods, including:
- Increased speed and efficiency: Electronic scanning can process identification documents faster than visual inspection, reducing wait times and improving the overall customer experience.
- Improved accuracy: ID scanning technology is less prone to human error, providing a more reliable verification process.
- Enhanced security: Electronic scanning can detect even the slightest alterations or counterfeiting on identification documents, helping to prevent identity theft and forgery.
- Compliance: ID scanning technology helps businesses comply with relevant laws and regulations, reducing the risk of fines and penalties.
Considerations for Implementation
While ID scanning technology offers many advantages, businesses must consider several factors before implementing such technology in their everyday settings, including:
- Cost: The initial investment in ID scanning technology can be substantial, requiring businesses to weigh the costs against the benefits.
- Training: Employees must receive proper training on the use and maintenance of ID scanning technology to ensure accurate and efficient verification.
- Data privacy: Businesses must ensure that identification data is stored and protected securely, adhering to relevant data protection regulations.
- Equipment compatibility: Businesses must select ID scanning technology that is compatible with their existing systems and equipment.
Real-Life Applications
ID scanning technology is used in various environments, including retail stores, bars, and restaurants, where age-restricted products and services are offered. In these settings, ID scanning technology helps businesses to verify the age and identity of customers, preventing underage access to these products and services.
According to a study by the National Institute of Justice, the use of ID scanning technology can reduce underage sales by up to 90%.
Methods to Protect Against Identity Theft and ID Fraud
Protecting oneself from identity theft and ID fraud requires a combination of vigilance, awareness, and proactive measures. In today’s digital age, personal data is easily accessible, and scammers are getting more sophisticated in their tactics. Staying one step ahead of these threats is essential to safeguarding our sensitive information.
Safely Storing and Disposing of Sensitive Documents
To minimize the risk of identity theft, it is crucial to store and dispose of sensitive documents, such as ID cards, securely. Here are some essential guidelines:
- Store sensitive documents in a safe and secure location, such as a locked cabinet or a fireproof safe. This will prevent unauthorized access and protect your documents from damage or theft.
- Shred unnecessary documents, including old ID cards, passports, and other sensitive papers. This will ensure that sensitive information is not compromised and cannot be used for identity theft.
- Use a secure disposal method for electronic devices, such as laptops, smartphones, and hard drives. This includes wiping the devices clean of personal data and physically destroying them to prevent data recovery.
Minimizing the Risk of Exposure to Fake IDs
To avoid falling victim to identity theft and ID fraud, it is essential to minimize the risk of exposure to fake IDs. Here are some strategies to adopt:
- Verify the authenticity of ID cards by checking for genuine features, such as holograms, watermarks, and microprinting.
- Use ID scanning technology to scan IDs and verify their legitimacy.
- Be cautious when handing out personal information, such as your ID card or birth certificate.
- Report any suspicious activity or attempted identity theft to the relevant authorities.
Action Plan for Identity Fraud
In the event of suspected identity fraud or theft, it is crucial to act swiftly and decisively to minimize further damage. Here is an action plan to follow:
- Freeze your credit report to prevent further unauthorized access.
- Notify your bank and other financial institutions to flag your accounts for suspicious activity.
- Report the incident to the relevant authorities, such as the police or a consumer protection agency.
- Change your passwords and account information to prevent further access.
- Monitor your credit report and bank statements for any suspicious activity.
How to Report and Address the Sale and Use of Fake IDs

When it comes to the sale and use of fake IDs, reporting suspicious activity or known incidents is crucial in combating this issue. Law enforcement agencies rely on the public to report any instances of counterfeit identification cards to help them investigate and take necessary action.
Reporting Suspicious Activity, How to check fake ids
If you suspect someone is selling or using a fake ID, you can report it to your local authorities. Here are the steps to follow:
You can report suspicious activity to the police by contacting your local station or visiting their website to fill out an online report form. When reporting, provide as much detail as possible, including the location, time, and description of the individuals involved.
Additionally, you can also report suspicious activity to your local licensing authority or to the state’s licensing department, if the fake ID is suspected to be a state-issued ID.
Law Enforcement Investigation and Action
Once a report is made, the police will investigate the incident. This may involve interviewing witnesses, reviewing security footage, and analyzing the fake ID to determine its authenticity and origin. Based on the findings, the police may take action against the individuals involved, including arrest and prosecution.
In some cases, the police may also work with local businesses and organizations to educate them on how to spot fake IDs and prevent their sale and use.
Community Programs and Regulations
Local regulations and community programs play a crucial role in preventing the sale and use of fake IDs. Some cities and states have implemented programs that provide rewards for reporting fake IDs, while others have increased penalties for those caught selling or using them.
For example, some states have implemented laws that require bar and club owners to verify the authenticity of ID cards before allowing individuals to enter. These laws have been implemented to reduce the number of fake IDs being used to gain entry to establishments.
Some cities have also implemented community programs that educate young people on the risks and consequences of using fake IDs. These programs often include workshops and presentations that highlight the importance of using authentic identification cards and the potential consequences of using fake ones.
Closure
By following the steps Artikeld in this guide, you will be equipped to differentiate between genuine and fake IDs with confidence. Remember, verification is key to responsible customer service and maintaining a safe environment. Stay vigilant and stay informed with our expert advice on how to check fake IDs.
Query Resolution
Can I use a mobile app to check fake IDs?
Yes, many mobile apps are available that use AI-powered technology to verify identification documents. However, it’s essential to choose a reliable app and follow the manufacturer’s guidelines for use.
How long do I need to store a customer’s ID after verifying it?
The length of time to store a customer’s ID varies depending on your business’s policies and local regulations. Typically, you should store IDs for as long as you need to confirm the customer’s age or identity and dispose of them securely.
What should I do if I suspect a customer is using a fake ID?
Approach the situation discreetly and professionally. Ask the customer to produce additional identification or verification, and consider contacting your local law enforcement agency if you suspect a serious case of ID fraud.
Can I use social media to verify a customer’s identification?
No, relying on social media to verify identification is not recommended. Social media profiles can be easily manipulated or created with fake information. Stick to trustworthy methods for verifying age and identity.