As how to delete files takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original. In the digital age, file management is a crucial aspect of data security, and deleting files the right way is essential to maintaining the integrity and confidentiality of your data.
From understanding the different types of file deletion methods available to securely erasing sensitive information, this comprehensive guide will walk you through the process of deleting files in a way that is both efficient and safe. We’ll explore the importance of reviewing file properties before deletion, the use of file shredding software and other secure erase methods, and the potential consequences of deleting a file without a clear policy in place.
Understanding File Deletion Methods
When it comes to deleting files, you might think it’s just a simple matter of hitting the delete button, but there’s more to it than meets the eye. In this section, we’ll dive into the different types of file deletion methods, both manual and automated, and explore when to choose one over the other.
Types of File Deletion Methods
File deletion methods can be broadly classified into three categories: permanent, temporary, and partial deletion.
Permanent File Deletion
Permanent file deletion is a method that permanently removes a file from your system, making it impossible to recover. This method is often used when you want to completely erase a file and its contents. One scenario where permanent file deletion would be more suitable is when dealing with highly sensitive or confidential data, such as financial information or personal identification documents.
This method is like taking a permanent marker – once you’ve used it, you can’t erase it!
Temporary File Deletion
Temporary file deletion, on the other hand, moves a file to a temporary location, making it inaccessible but still retaining its original content. This method is often used in debugging or testing scenarios where you want to preserve the original file for future reference. Temporary deletion is like moving a file to a “storage unit” – it’s still there, but you can’t access it from the main storage area.
Partial File Deletion
Partial file deletion is a method that deletes only a portion of a file, rather than the entire file. This method is often used when dealing with large files or when you want to save storage space. Partial deletion is like editing a document – you’re removing specific parts, but the rest remains intact.
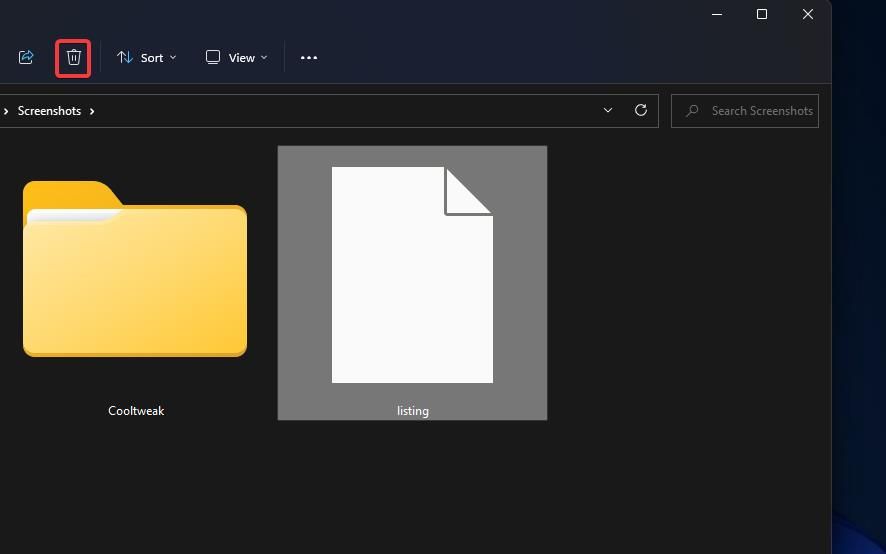
Manual vs. Automated File Deletion Processes, How to delete files
Manual file deletion involves using the operating system’s built-in file deletion tools, such as the Windows Explorer or macOS Finder, to delete files. Automated file deletion, on the other hand, uses third-party software or scripts to delete files based on specific criteria, such as file type, age, or size. Automated deletion is like having a personal assistant – it saves time and effort by doing the task for you!
Manual deletion is a good choice when you need to delete a small number of files or when you want more control over the deletion process. Automated deletion is a better option when you need to delete a large number of files or when you want to perform repetitive tasks efficiently.
Preparing Files for Deletion
Before you embark on the deletion adventure, it’s essential to prepare those files for a smooth goodbye. Think of it like packing for a trip – you don’t want to accidentally leave anything behind that might cause trouble later.
Reviewing File Properties
Imagine you’re about to delete a file, but you’re not sure if you’re the owner, or what permissions other users have on it. This is where file properties come in – they’re like a file’s passport, containing information about who created it, who owns it, and what permissions are attached. Reviewing these properties before deletion is crucial to avoid any potential problems.
When reviewing file properties, look for the following:
- Date and Time Created
- Owner and Group
- Permissions
- File Size and Location
- Data Breaches
- Loss of Valuable Data
- Regulatory Consequences
- Windows: When you delete a file in Windows, the operating system typically sends a delete request to the file system, which marks the file as deleted and removes it from the directory table. The file data itself is not immediately deleted; instead, it’s scheduled for deletion at the next system shutdown or during a subsequent disk cleanup process. Windows also keeps deleted files in a recycle bin, allowing users to recover them if needed.
- macOS: In macOS, file deletion works similarly to Windows. The operating system sends a delete request to the file system, which marks the file as deleted and removes it from the directory table. However, unlike Windows, macOS doesn’t have a dedicated recycle bin; instead, deleted files are sent to the Trash, which behaves similarly to the recycle bin.
- Linux: Linux file deletion is often more involved than in Windows or macOS. When you delete a file, the operating system typically sends a request to the file system, which marks the file as deleted and removes it from the directory table. However, the file data itself may still remain on the disk, depending on the file system and the presence of any file deletion hooks. Additionally, Linux often uses a combination of the file system’s inode and directory tables to manage deleted files.
- is a popular tool for deleting temporary files, system files, and other unwanted data. It’s available for both PC and Mac, and offers a range of customizable settings to help you tailor your cleaning experience.
- offers advanced features like secure deletion, registry cleaning, and system optimization. It’s a great option for those who need more advanced cleaning capabilities.
- is a simple tool that allows you to delete files securely, using advanced algorithms to overwrite data multiple times. It’s a great option for those who want to ensure their deleted files are truly gone.
- offers a range of advanced features like secure deletion, disk wiping, and file shredding. It’s a great option for those who need advanced cleaning capabilities.
-
Data breaches: Unintentional deletion of sensitive data can result in catastrophic consequences, including loss of confidential information, reputational damage, and financial loss.
-
Regulatory fines: Companies that fail to protect sensitive data can face hefty fines and penalties, as seen in the case of the UK’s Labour Party.
-
Loss of business: Customers may lose trust in a company that mishandles sensitive data, leading to a loss of business and revenue.
This tells you when the file was created, which can be useful for tracking changes or identifying potential security threats.
Check who the owner and group of the file are, as this will determine who has permission to access and modify the file.
Permissions determine what actions users can perform on the file, such as read, write, or delete. Ensure that you have the necessary permissions to delete the file.
Verify the file size and location to ensure you’re deleting the correct file.
For instance, imagine you’re working on a project with a team, and one of your team members has created a file with sensitive information. If you don’t review the file properties before deletion, you might inadvertently delete the file, which could lead to data breaches or loss of valuable information.
Deleting a file with sensitive information can have severe consequences, including:
Sensitive information can fall into the wrong hands, compromising your team’s security and reputation.
Deleting a file with valuable data can result in lost productivity, wasted time, and reduced team efficiency.
Depending on the type of data deleted, you might be subject to regulatory penalties or fines for non-compliance with data protection laws.
File Deletion and Operating System Differences
When it comes to deleting files, the operating system plays a significant role in determining the outcome. While the general process of deleting a file may seem similar across different operating systems, there are some key differences that can affect the way files are deleted. In this section, we’ll delve into the world of file deletion and explore the differences between Windows, macOS, and Linux.
File Deletion Processes: A Comparison
From a technical standpoint, file deletion involves removing the entry from the file system’s directory table and, depending on the operating system, possibly also freeing up the space on the hard drive. Let’s take a look at how different operating systems handle file deletion:
Real-World Example
Consider a scenario where you’re working on a collaborative project and accidentally delete a crucial file from a shared system. In this case, the operating system’s file deletion process can have significant consequences. For example, if you’re using a Windows system, the deleted file might still be recoverable from the recycle bin. However, if you’re using a Linux system, the deleted file might be irreversibly lost, depending on the file system and any file deletion hooks.
Sharing Systems and File Deletion
When it comes to shared systems, file deletion can be more complicated due to the presence of multiple users and potential data loss or corruption. For instance, if two users are working on a shared document and one user deletes the file, the other user may lose access to the file’s data or experience file corruption. In these situations, it’s essential to implement proper backup and version control procedures to minimize data loss and ensure continuity.
File deletion is not always an immediate process and can have unintended consequences, especially in shared systems.
File Deletion Tools and Software: How To Delete Files
Are you tired of manually deleting files one by one? Do you need a tool to help you wipe out those pesky files? Look no further! In this section, we’ll dive into the world of file deletion tools and software, exploring their features, limitations, and popular options.
File deletion tools and software are designed to simplify the process of deleting files, allowing you to remove multiple files at once or even wipe entire folders clean. These tools often come with additional features such as secure deletion methods, customizable settings, and integration with other software.
Popular File Deletion Tools
When it comes to popular file deletion tools, there are several options to choose from, each with their own strengths and weaknesses. Here are some of the most well-known tools:
When choosing a file deletion tool, consider your specific needs and preferences. Do you need a simple tool for deleting temporary files, or do you require advanced features for secure deletion?
Step-by-Step Guide to Installing and Using a Popular File Deletion Tool
In this example, we’ll walk you through the process of installing and using .
1.
Download and install from the official website
2. Launch and select the type of cleaning you want to perform (e.g. “Quick Clean” or “Deep Clean”)
3. Click “Analyze” to let scan your system for unwanted files
4. Review the list of files and folders to be deleted and select the items you want to remove
5. Click “Run Cleaner” to start the cleaning process
That’s it! With these steps, you’ll be able to install and use like a pro.
File Deletion Best Practices
The golden rule of file deletion is quite simple: if you don’t know what you’re doing, don’t do it yourself. This is especially true for companies dealing with sensitive data. Without a clear file deletion policy, chaos can ensue, and confidentiality can be compromised. In this section, we’ll dive into why having a solid policy is crucial and share a real-life example of a company that got it right.
The Importance of a Clear Policy
A well-structured file deletion policy is like a safety net for your company. It Artikels who can delete files, how they should be deleted, and what happens to the data afterwards. This ensures that sensitive information is protected and that everyone involved knows their role. Without such a policy, employees may accidentally delete crucial files, or worse, delete them intentionally to cover their tracks.
When companies fail to establish clear guidelines, the consequences can be disastrous. In 2010, the UK’s Labour Party made headlines when it was revealed that the party’s leader, Ed Miliband, had used a personal email account to conduct party business. This led to a data breach, resulting in the loss of sensitive data. The incident highlighted the importance of having a clear file deletion policy, especially when dealing with sensitive information.
Consequences of Deleting a File Without a Clear Policy
Without a clear policy, deleting a file can lead to a range of problems, including:
By implementing a clear file deletion policy, companies can avoid these pitfalls and ensure the responsible handling of sensitive data. It’s a matter of being prepared and having a plan in place to protect confidentiality and avoid data breaches.
Real-Life Example: Sony’s Policy Implementation
Sony’s 2011 data breach serves as a case in point. The company had a clear file deletion policy in place, which helped them respond quickly to the incident. Their policy ensured that sensitive data was encrypted and stored securely, minimizing the damage.
When the breach occurred, Sony’s IT team followed the policy by immediately isolating the affected systems and conducting a thorough investigation. The company’s swift action helped prevent the breach from spreading further, and they were able to mitigate the damage.
By learning from Sony’s example, companies can implement effective file deletion policies that protect their sensitive data and minimize the risk of data breaches.
Final Conclusion
By following the steps Artikeld in this guide, you’ll be able to securely delete files and maintain the integrity of your data. Remember, file deletion is not just about getting rid of unwanted files – it’s about protecting your sensitive information from falling into the wrong hands.
Q&A
Q: Can I recover a file once it’s been deleted?
A: It depends on the file system and the deletion method used. In some cases, deleted files can be recovered using specialized software, but this is not always possible, and attempting to recover a deleted file can be complicated.
Q: Is it safe to delete a file without reviewing its properties?
A: No, it’s not safe to delete a file without reviewing its properties. This can lead to the loss of important data or even cause system crashes. Always take the time to review a file’s properties before deleting it.
Q: What is the difference between file shredding and file wiping?
A: File shredding is a more secure method of deleting files that overwrites data multiple times to ensure it’s irrecoverable, while file wiping simply removes the file from the system but doesn’t overwrite the data. File shredding is generally used for sensitive data, while file wiping is sufficient for less sensitive information.