As how to delete temporary files takes center stage, this opening passage beckons readers into a world that explores the importance of regularly deleting temporary files for optimal system performance. Temporary files, often overlooked, can accumulate and lead to data loss, system crashes, and security vulnerabilities if left unchecked. This article aims to provide a comprehensive guide on the types of temporary files, methods for deletion, and best practices for ensuring safe and effective removal.
The purpose of temporary files in system operations is to provide a temporary storage area for data, facilitating the creation and modification of data by software applications. However, this temporary storage area can become cluttered with unused files, making it essential to regularly clean out the temporary files. This is particularly crucial in today’s digital age where data is created and deleted at an alarming rate.
The Importance of Regularly Deleting Temporary Files
Regularly deleting temporary files is a crucial task that can help prevent various issues on your devices, including smartphones, laptops, and desktop computers. Temporary files can consume a significant amount of storage space, slow down your device’s performance, and pose security risks if not deleted properly.
Temporary files are generated by various system operations, including software installations, updates, and uninstallations. They are also created by applications and software programs, such as web browsers, email clients, and office suites. These files are typically stored in temporary directories, such as the Windows Temp folder or the macOS Downloads folder.
Purpose of Temporary Files
Temporary files serve several purposes, including:
- Providing a temporary storage space for application data and settings
- Enabling software updates and installations to take place
- Storing cache data to improve application performance
- Generating a record of system activity and errors
These files are essential for system operations, but they can become problematic if they are left undeleted. Temporary files can fill up your storage space, causing your device to slow down and become unresponsive. Furthermore, these files can contain sensitive information, such as passwords, cookies, and other user data, which can put your security at risk if they fall into the wrong hands.
Risks Associated with Undeleted Temporary Files
Undeleted temporary files can lead to various issues, including:
- Data loss: Temporary files can overwrite important system files, causing data loss and corruption.
- System crashes: Undeleted temporary files can cause system crashes and instability, requiring a reboot or even a reinstallation of the operating system.
- Security vulnerabilities: Temporary files can contain sensitive information, such as passwords and cookies, which can be exploited by hackers to gain unauthorized access to your device and personal data.
- Storage capacity issues: Undeleted temporary files can consume a significant amount of storage space, leading to performance issues and reduced device lifespan.
Examples of Temporary Files
Temporary files are generated by various software applications, including:
- Web browsers: Temporary files are created by web browsers to store cache data, cookies, and other user data.
- Email clients: Temporary files are generated by email clients to store attachments and other data.
- Office suites: Temporary files are created by office suites to store data, such as spreadsheets and word processing documents.
- System utilities: Temporary files are generated by system utilities to store logs, error messages, and other system activity data.
It is essential to regularly delete temporary files to prevent these issues and maintain the health and security of your devices.
Understanding the Different Types of Temporary Files
Temporary files play a crucial role in the smooth functioning of operating systems and software applications. These files are created to store data temporarily, allowing for faster performance, improved user experience, and efficient memory management. There are several types of temporary files, each serving a unique purpose.
System cache files, user cache files, and session files are the three primary types of temporary files. Understanding the functions and purposes of each is essential to appreciate their significance in system performance.
System Cache Files
System cache files are temporary files stored by the operating system to optimize performance. They contain frequently accessed data, making it readily available for quick retrieval. This reduces the time and resources required for the CPU to access the original data.
- System cache files improve system responsiveness by reducing the time between user input and system response.
- They help alleviate system bottlenecks caused by excessive data access, ensuring smoother system operation.
- System cache files are generated by the operating system, and their storage and maintenance are handled internally.
Cache files are typically stored in the system’s RAM, which makes them volatile. When the system restarts, the cache files are lost. However, some operating systems, such as Linux and macOS, can recover cache files from the swap space. Windows operating systems store cache files in a combination of RAM and virtual memory.
User Cache Files
User cache files are generated by software applications to store data temporarily. These files are created to improve user experience and optimize application performance. User cache files are typically stored on the user’s local machine.
- User cache files contain data used by applications, such as website credentials, browsing history, and recently opened files.
- They enable applications to load previously accessed data quickly, enhancing the user experience.
- User cache files can be managed by the user, allowing for manual deletion or clearing of cache contents.
Session Files
Session files, also known as session store files, record user interactions within a software application. They store user preferences, login credentials, and other data that persists between application launches. Session files are essential for maintaining a seamless user experience.
- Session files contain data that persists across application launches, allowing for resume functionality and improved user experience.
- They can be used to track user activity, enabling targeted advertising and personalized recommendations.
- Session files are typically deleted when the user logs out or closes the application.
Examples of Temporary Files Generated by Popular Software Applications
Popular software applications generate temporary files to optimize performance, improve user experience, and maintain data integrity. Some examples of temporary files generated by well-known applications include:
| Application | Description |
|---|---|
| Browsers (Google Chrome, Mozilla Firefox) | Cookie files, browsing history, and cache files |
| Microsoft Office | Temporaneous files for word processing, spreadsheet, and presentation editing |
| Adobe Photoshop | Temporary layers, alpha channels, and cache files for smooth image editing |
Temporary files play a crucial role in maintaining system performance and user experience. By understanding the different types of temporary files and their functions, users can optimize system performance and ensure seamless application usage.
Methods for Deleting Temporary Files
Deleting temporary files is an essential task to maintain system performance, optimize storage space, and prevent clutter buildup. By manually deleting temporary files using built-in system tools and software applications, you can ensure a clutter-free environment and prevent potential security risks.
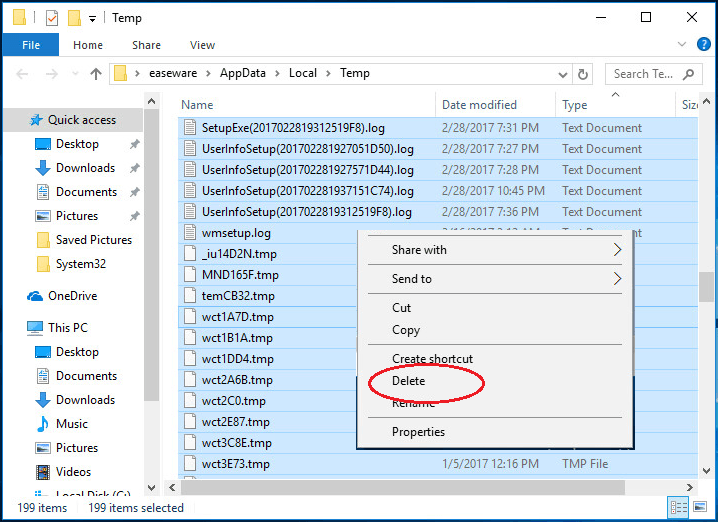
Manual Methods for Deleting Temporary Files
When it comes to deleting temporary files manually, there are several built-in system tools and software applications that can come in handy. Here are some of the most commonly used methods:
- Using the Task Manager (Windows): On Windows devices, you can use the Task Manager to delete temporary files by navigating to the “Processes” tab, finding the temp files, and selecting “End Task” to terminate the process. Alternatively, you can use the “Run” dialog box (Windows key + R) and type “cleanmgr” to access the Disk Cleanup tool, which can help delete temporary files, system files, and other items you don’t need.
- Using the Activity Monitor (macOS): On macOS devices, you can use the Activity Monitor to delete temporary files by navigating to the “Applications” tab, finding the temp files, and selecting “Quit” to terminate the process. You can also use the “System Information” tool to view and delete temporary files.
- Using the ‘trash’ Command (Linux): On Linux devices, you can use the ‘trash’ command to delete temporary files by accessing the terminal and typing “trash” followed by the path to the temp file or folder. This will move the file to the trash, where you can permanently delete it.
Third-Party Tools and Software for Deleting Temporary Files
There are numerous third-party tools and software programs available that can help you delete temporary files with ease. Here are some of the most popular options:
- CCleaner: CCleaner is a popular utility tool that can help delete temporary files, system files, and other items you don’t need. It’s available for Windows, macOS, and Linux devices.
- Glary Utilities: Glary Utilities is a comprehensive maintenance tool that includes a temp file cleaner, as well as other features like disk cleaning, registry cleaning, and more.
- CleanMyMac X: CleanMyMac X is a popular Mac cleaning tool that can help delete temporary files, system files, and other items you don’t need. It also includes features like malware removal and disk cleaning.
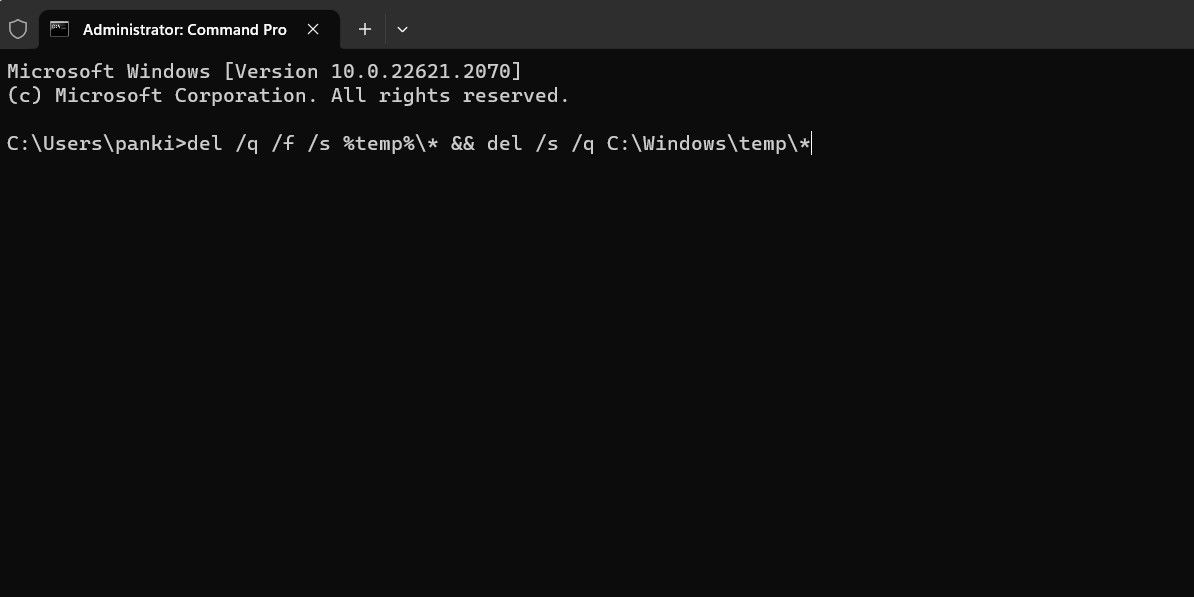
Automation and Scheduling Temporary File Deletion, How to delete temporary files
You can also automate temporary file deletion using scripts and scheduling tools. Here’s a quick rundown of how to do it:
- Using Automator (macOS): On macOS devices, you can use Automator to create a workflow that deletes temporary files on a scheduled basis. Simply create a new workflow, add a “Get Selected Files” action, and then add a “Move to Trash” action to delete the files.
- Using Task Scheduler (Windows): On Windows devices, you can use Task Scheduler to create a scheduled task that deletes temporary files on a scheduled basis. Simply create a new task, add an action to delete the files, and then set the schedule to run the task automatically.
- Delete temporary files daily, especially if you use your computer frequently.
- Use a monthly schedule for less frequent deletions, such as system temporary files.
- Set up a weekly schedule for maintenance tasks, including file defragmentation and disk cleanup.
- Check the file extension and location before deleting. Some system files may have extensions like `.tmp` or `.bak`.
- Use file attributes or flags to identify essential files, such as files marked as ‘System File’ or ‘Hidden File’.
- Create a backup of important files before deleting temporary files, in case of accidental deletion.
- Use command-line tools like `del`, `rm`, or `rmdir` to delete temporary files.
- Write custom scripts using languages like PowerShell or Bash to automate the deletion process.
- Use scheduling tools like Task Scheduler or `cron` to automate the deletion process at regular intervals.
- Monitor the deletion process for errors or warnings.
- Use logging tools to track the deletion process and identify issues.
- Use try-catch blocks or error-handling mechanisms to catch and handle errors.
- Read (r) Permission: This permission allows users to view the contents of a file. For temporary files, read permission is essential to ensure that users can access the files as needed.
- Write (w) Permission: This permission allows users to modify or delete the contents of a file. For temporary files, write permission should be restricted to authorized users to prevent unauthorized changes.
- Execute (x) Permission: This permission allows users to execute a file as a program. For temporary files, execute permission is typically not required.
- Owner: The owner of a file has complete control over the file, including its permissions, deletion, and modification.
- Group: The group owner of a file has control over the file’s permissions and can modify the file, but not delete it.
- Other: Other users can have read, write, or execute permissions to the file, depending on the file’s permissions.
- Use the chmod command to set permissions for temporary files.
- Use the chown command to set ownership for temporary files.
- Restrict write and execute permissions to authorized users.
- Set read permission for all users to ensure accessibility.
- Use the ls -l command to display the file’s permissions and ownership.
- Use the chmod command to set permissions for the file.
- Use the chown command to set ownership for the file.
The Risks of Improper Temporary File Deletion
Temporary files play a crucial role in the functioning of modern computing systems, facilitating various tasks such as data storage, application operation, and system maintenance. However, mismanaging their deletion can lead to detrimental consequences, including data loss, system corruption, and security breaches.
Data Loss and Overwriting
Misdeleting temporary files can lead to catastrophic consequences when these files are critical to the operation of applications or system functions. If temporary files containing vital data are erased or corrupted, users may experience data loss, resulting in a significant loss of productivity and potential financial implications. This can occur due to a combination of factors such as system crashes, misconfigured applications, or hardware failure.
System Corruption and Instability
Temporary files are designed to be temporary, but when these files are not properly deleted, they can accumulate and cause system issues. When multiple temporary files are misdeleted, they can leave behind remnants that can interfere with system functions. This can lead to system crashes, application errors, slower system performance, and even a complete system failure. Furthermore, the accumulation of temporary files can fill up disk space, resulting in disk crashes or the need for disk space management.
Security Risks and Vulnerabilities
Temporary files often contain sensitive information, such as passwords, encryption keys, and login credentials. If these temporary files are not properly secured or deleted, they can be exploited by malicious actors, leading to security breaches and potential identity theft. Malicious actors can also utilize misdeleted temporary files as a vector for malware or ransomware spread.
Example of a Real-Life Scandal – WannaCry Attack (2017)
During the WannaCry global ransomware attack in 2017, temporary files played a significant role in the propagation of the malware. The attack spread rapidly, causing widespread disruptions to healthcare, transportation, and financial services worldwide. This event highlights the devastating consequences of mismanaging temporary files, including data loss, system corruption, and security breaches. As part of its analysis, cybersecurity researchers noted that temporary files containing vulnerable server software configurations and outdated patches were exploited to facilitate the spread of the malware.
The Importance of Proper Deletion Procedures
To mitigate the risks associated with temporary files, it is essential to establish proper deletion procedures for these files. This can involve implementing a robust temporary file cleanup schedule that ensures deleted files are promptly removed from the system. Regular system maintenance, including disk cleanups, updates, and virus scans, can also help prevent the buildup of temporary files that may pose security risks.
Operating System-Specific Risks and Considerations
Different operating systems and file systems have varying levels of security and data protection features. When managing temporary files, understanding these differences is crucial to ensuring security and preventing potential data loss. For instance, Windows and macOS operating systems have built-in features for managing temporary files, but these features may not provide adequate security against sophisticated threats. Users should be aware of the operating system-specific risks and considerations when handling temporary files.
Best Practices for Temporary File Deletion
Temporary files can pile up quickly, taking up space and slowing down your system. To keep your computer running smoothly, it’s essential to regularly delete temporary files. But how do you do it safely and effectively? Here are some best practices to follow:
Setting Up Regular Deletion Schedules and Maintenance Routines
Regularly deleting temporary files is crucial to maintaining your system’s performance. Set up a schedule to delete temporary files at regular intervals, such as daily, weekly, or monthly. You can use built-in tools or third-party software to automate this process. This will help ensure that your system stays clean and free of unnecessary files.
Identifying and Excluding Important Files from Deletion Processes
Be cautious when deleting temporary files, as some essential files may be incorrectly marked as temporary. To avoid deleting important files, identify and exclude them from the deletion process. Here are some tips to help you do so:
Creating Custom Deletion Scripts and Automating the Process
Automating the process of deleting temporary files can save you time and effort. Create custom scripts or use command-line tools to automate the deletion process. This will ensure that your system stays clean and free of unnecessary files.
Error Handling and Troubleshooting
Be prepared for unexpected errors when deleting temporary files. To handle errors and troubleshoot issues, follow these best practices:
Understanding Temporary File Permissions and Ownership: How To Delete Temporary Files
Temporary files play a crucial role in various computer systems and applications. Ensuring proper permissions and ownership for these files is vital to prevent unauthorized access, data breaches, and system vulnerabilities. In this section, we’ll delve into the importance of temporary file permissions and ownership, and discuss best practices for setting up access controls.
The Role of File Permissions
File permissions determine who can access, modify, or delete files on a system. For temporary files, permissions are essential to control access and prevent unauthorized changes. File permissions typically include three main categories: read (r), write (w), and execute (x). Understanding these permissions is critical in managing temporary files effectively.
The Importance of Proper Ownership
Proper ownership of temporary files is essential to prevent unauthorized access and data breaches. The owner of a file has complete control over the file, including its permissions, deletion, and modification. Ensuring that temporary files have proper ownership is critical to maintaining system security.
Best Practices for Setting Up Access Controls
To ensure proper permissions and ownership for temporary files, follow these best practices:
Managing Permissions and Ownership using Command-Line Tools
To manage permissions and ownership for temporary files using command-line tools:
For example, to set permissions for a temporary file using the chmod command:
“`
chmod u=rwx,g=rx,o=r temp_file.txt
“`
To set ownership for a temporary file using the chown command:
“`
chown user:group temp_file.txt
“`
By following these best practices and using command-line tools to manage permissions and ownership, you can ensure that temporary files are properly secured and accessed only by authorized users.
Last Word
Deleting temporary files is a crucial aspect of maintaining a healthy and efficient computer system. By regularly cleaning out temporary files, users can prevent data loss, system crashes, and security vulnerabilities. This article has provided a comprehensive guide on how to delete temporary files, including methods, best practices, and the importance of regular deletion. Remember, a clutter-free temporary file system is essential for optimal system performance.
By following the guidelines Artikeld in this article, users can ensure that their temporary file system is running smoothly and efficiently. This is particularly important for computer users who work with sensitive data or software applications. Remember, regular deletion of temporary files is essential for maintaining a secure and efficient computer system.
FAQs
Q: What happens if I don’t delete temporary files?
A: If you don’t delete temporary files, they can accumulate and lead to data loss, system crashes, and security vulnerabilities.
Q: Can I delete temporary files manually or do I need third-party tools?
A: You can delete temporary files manually using built-in system tools or software applications, but third-party tools can also be used for efficient deletion.
Q: How often should I delete temporary files?
A: It is recommended to delete temporary files regularly, ideally every week or month, depending on usage and system requirements.
Q: Are there any risks associated with deleting temporary files?
A: Yes, there are risks associated with deleting temporary files, including data loss and security vulnerabilities, if not done properly.
Q: Can I automate temporary file deletion using scripts?
A: Yes, you can automate temporary file deletion using scripts and scheduling tools for efficient maintenance.