How to deploy intune lock screen image takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original. By customizing the lock screen image, you can enhance the user experience and increase productivity, which is the key to a successful implementation. To cater to different user groups, such as employees, contractors, or students, you can customize the lock screen images in various ways.
The preparation of the Intune environment is a crucial step in deploying lock screen images. This involves setting up and configuring the environment, as well as assigning the necessary permissions and roles to Intune administrators. By following the correct steps, you can ensure a smooth deployment process.
Preparing the Intune Environment for Lock Screen Image Deployment: How To Deploy Intune Lock Screen Image
In this section, we’ll walk you through setting up and configuring the Intune environment for lock screen image deployment. This includes creating the necessary roles and permissions, uploading the lock screen image, and verifying the deployment.
Before we begin, ensure you have the required permissions and roles assigned. We’ll cover this in detail below.
### Prerequisites and Roles
As an Intune administrator, you’ll need the necessary permissions and roles to deploy lock screen images.
* MEM (Microsoft Endpoint Manager) Administrator: This role includes the necessary permissions for managing device compliance, including deploying lock screen images.
* Intune User: You must be an Intune user to perform lock screen image deployment.
| Role | Permissions Required |
| — | — |
| MEM Administrator | Device Compliance Management, Lock Screen Configuration |
| Intune User | Lock Screen Image Upload, Deployment |
### Step 1: Create Device Compliance Policy
1. Log in to the Microsoft Endpoint Manager admin center.
2. Navigate to Device Compliance > New Policy.
3. Select Windows 10 and later as the platform.
4. Choose a name and description for the policy.
5. Under Settings, expand Compliance settings.
6. Select Lock screen.
7. Choose the lock screen image you want to deploy.
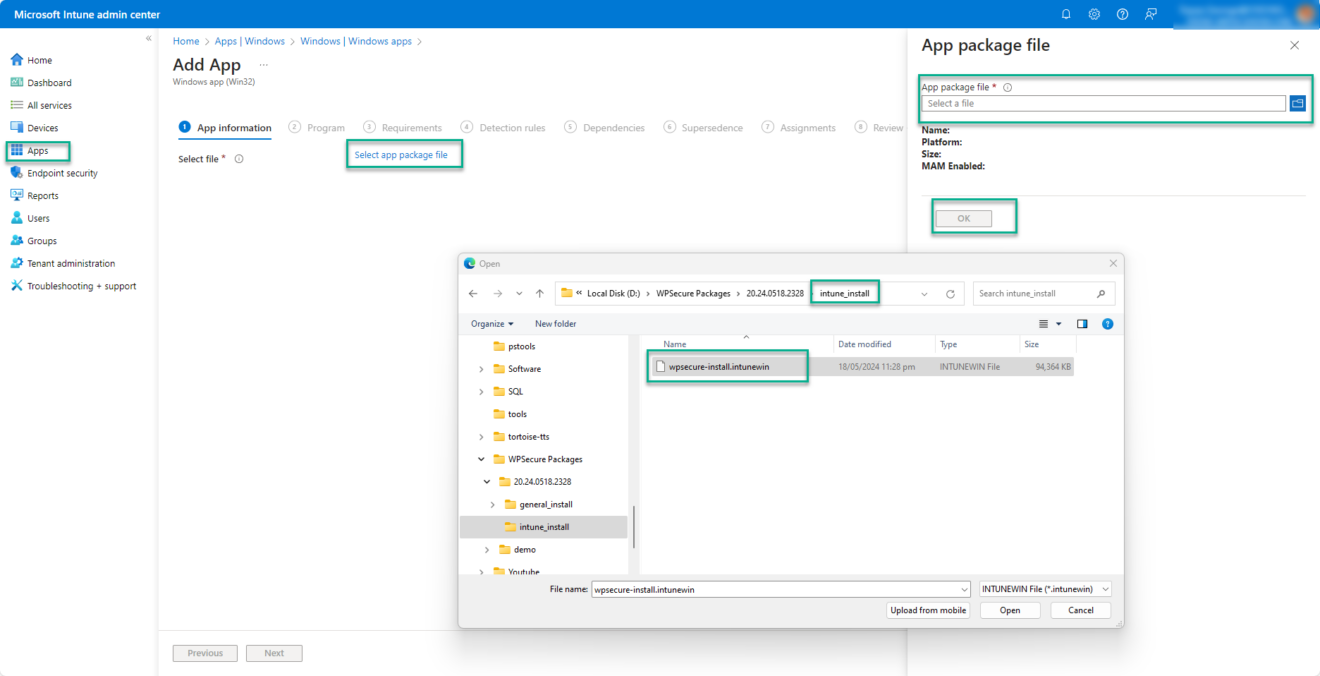
### Step 2: Upload Lock Screen Image
1. Log in to the Microsoft Endpoint Manager admin center.
2. Navigate to Assets > Files.
3. Click Upload file.
4. Select the lock screen image you want to deploy.
5. Add a description and tags for the image.
### Step 3: Verify Deployment
1. Log in to the Microsoft Endpoint Manager admin center.
2. Navigate to Device Compliance > Compliance Status.
3. Find the device you want to verify.
4. Review the compliance status to ensure the lock screen image is deployed correctly.
Understanding Device Compliance Policies
A device compliance policy is a set of rules that ensure devices meet certain security and configuration requirements. In this context, the policy is used to deploy the lock screen image.
* A compliance policy can be assigned to a group of devices or a single device.
* Devices must meet the compliance rules to remain compliant.
* Intune provides built-in compliance policies for various platforms, including Windows 10.
Lock Screen Image Requirements
To deploy a lock screen image using Intune, the image must meet certain requirements.
* The image must be in PNG or JPEG format.
* The image must be 1920 x 1080 pixels in resolution.
* The image must be less than 5 MB in size.
Creating a Custom Lock Screen Image for Intune Deployment
Creating a custom lock screen image for Intune deployment is a straightforward process that requires some basic software and design skills. To create a stunning lock screen image, we’ll need to get familiar with Adobe Photoshop or a similar image editing software.
Selecting the Right Software
There are many image editing software available in the market, but Adobe Photoshop remains the industry standard for creating high-quality images. Photoshop provides an extensive range of tools and features that allow you to create visually appealing images. If you’re new to image editing, you can start with the free version of GIMP, a popular open-source alternative to Adobe Photoshop.
To create a custom lock screen image, you’ll need to have a clear idea of the design concept. Let’s consider some examples of custom lock screen image designs.
Examples of Custom Lock Screen Image Designs
Here are a few examples of custom lock screen image designs that you can create:
- Logos: Create a custom logo that represents your company or organization. You can design a modern logo that reflects your brand identity or create a playful logo that adds some humor to the lock screen.
- Graphics: Design a custom graphic that adds some visual interest to the lock screen. You can create a abstract graphic with shapes and patterns or design a graphic that incorporates your company’s colors.
- Text Overlays: Add some text overlays to the lock screen image to create a personalized message. You can create a inspirational quote or a funny phrase that adds some humor to the lock screen.
- Memes: Create a custom meme that adds some humor to the lock screen. You can design a meme that incorporates popular characters or create a meme that pokes fun at a common office scenario.
Designing a Custom Lock Screen Image
When designing a custom lock screen image, keep the following tips in mind:
- Use bright colors to grab the user’s attention. Avoid using dark colors that may be difficult to read.
- Keep the design simple and uncluttered. Avoid using too many fonts or graphics that may make the design look busy.
- Make sure the design is scalable. Ensure that the image looks good in different resolutions and aspect ratios.
- Use a clear and legible font. Avoid using fonts that are too ornate or difficult to read.
These are just a few examples of custom lock screen image designs that you can create. With a bit of creativity and design skills, you can create a stunning custom lock screen image that reflects your brand identity or adds some humor to the workspace.
Designing and Testing Intune Lock Screen Images for Different Devices
When it comes to deploying lock screen images through Intune, it’s not a one-size-fits-all approach. Device types, such as Windows 10, Windows 11, and iOS devices, have different requirements and limitations when it comes to displaying custom lock screen images. Designing images that are compatible with these various device types is crucial to ensure a seamless experience for users.
Designing images for different device types requires consideration of their respective resolutions, aspect ratios, and image formats. Windows devices, for example, support a wider range of image formats, including JPEG, PNG, and GIF, while iOS devices are limited to PNG and JPEG. Understanding these differences will help you create images that can be deployed successfully across multiple device types.
Comparison of Lock Screen Image Deployment for Various Device Types
The following table highlights the key differences in lock screen image deployment for Windows 10, Windows 11, and iOS devices.
| Device Type | Image Formats Supported | Resolution and Aspect Ratio | Deployment Method |
|---|---|---|---|
| Windows 10 | JPEG, PNG, GIF | Resolution: up to 1024 x 768 pixels Aspect Ratio: 1.778:1 (16:9) |
Intune: Upload image to AzureBlob storage and configure device configuration policy |
| Windows 11 | JPEG, PNG | Resolution: up to 3840 x 2160 pixels Aspect Ratio: 1.7778:1 (16:9) |
Intune: Upload image to AzureBlob storage and configure device configuration policy |
| iOS Devices | PNG, JPEG | Resolution: up to 2048 x 1536 pixels Aspect Ratio: 2.66:1 (9:16) |
Intune: Configure mobile device management (MDM) policy with custom lock screen image |
Understanding these differences and requirements will help you design and deploy lock screen images that are compatible with various device types, ensuring a seamless experience for users.
Managing and Updating Intune Lock Screen Images
When it comes to managing and updating Intune lock screen images, organization is not just an option, it’s a necessity to ensure smooth operation, reduced downtime, and improved user experience. One key aspect to consider in this process is the importance of having a well-implemented management system.
Automation and Scheduling Tools
When managing multiple lock screen images, it becomes essential to use automation and scheduling tools to streamline processes and minimize manual intervention. Here are some strategies for using these tools effectively:
–
- Use Azure DevOps pipelines to automate the deployment of lock screen images to Intune. This allows you to integrate different tools and services, such as GitHub, Azure Storage, and Intune, to create a seamless workflow.
- Leverage Azure Functions to create custom automation workflows for specific device or user groups. This enables you to tailor your deployment process to meet the unique needs of different teams or departments.
- Employ Intune’s built-in automation features, such as automation scripts, to automate tasks like lock screen image updates and device configuration. This helps to reduce administrative overhead and minimizes the risk of human error.
- Utilize scheduling tools like Azure Automation or Microsoft Flow to schedule lock screen image updates at specific times or intervals. This ensures that deployment occurs when it’s least likely to disrupt user productivity.
- Implement a centralized governance model to manage and update lock screen images across the organization. This involves creating a clear set of policies, procedures, and guidelines for managing digital assets.
Benefits of Using Azure DevOps and Microsoft Intune
Azure DevOps and Microsoft Intune offer a range of benefits when it comes to managing and updating lock screen images. Here are some of the advantages of using these platforms:
–
- Centralized Management: Azure DevOps and Microsoft Intune provide a centralized platform for managing digital assets, including lock screen images. This allows administrators to view, update, and manage all assets from a single location.
- Improved Visibility: With Azure DevOps, admins can track and monitor the lifecycle of lock screen images, including deployment, updates, and versioning. This level of visibility reduces the risk of errors and allows for more efficient troubleshooting.
- Automated Workflows: Azure DevOps enables admins to create customized, automated workflows for deployment and update processes. This minimizes manual intervention and reduces the risk of human error.
- Integration with Other Tools: Azure DevOps integrates with a wide range of tools and services, including GitHub, Azure Storage, and Intune. This allows for seamless collaboration and streamlines workflows.
By using Azure DevOps and Microsoft Intune to manage and update lock screen images, organizations can improve visibility, automate workflows, and reduce the risk of human error.
Best Practices for Intune Lock Screen Image Security and Compliance
Intune lock screen images can pose a risk to an organization’s security and compliance if not properly managed. To mitigate these risks, it is essential to follow best practices for securing and managing Intune lock screen images.
Data Loss Prevention (DLP) Requirements
Data Loss Prevention (DLP) is a critical security feature that prevents sensitive information from being leaked or exfiltrated from an organization’s network. When implementing DLP for Intune lock screen images, consider the following requirements:
- Classify sensitive data: Identify and classify sensitive data that should not be displayed on the lock screen, such as confidential company information or personal identifiable information (PII).
- Use DLP policies: Implement DLP policies to control what data is displayed on the lock screen and ensure that sensitive data is not shared.
- Monitor and report: Monitor DLP activity and report on any detected data breaches or leaks.
Conditional Access Requirements
Conditional Access is a feature in Intune that allows administrators to control access to company resources based on user and device conditions. When implementing Conditional Access for Intune lock screen images, consider the following requirements:
- Use Conditional Access policies: Implement Conditional Access policies to control access to company resources based on user and device conditions.
- Require multi-factor authentication: Require multi-factor authentication for users who access company resources from devices with lock screen images.
- Enforce device compliance: Enforce device compliance before allowing users to access company resources from devices with lock screen images.
Potential Risks and Consequences of Non-Compliance
The potential risks and consequences of non-compliance with security and compliance requirements for Intune lock screen images include:
- Data breaches: Unauthorized access to sensitive data can lead to data breaches and leaks.
- Regulatory non-compliance: Failure to comply with regulatory requirements can result in fines and penalties.
- Reputational damage: Non-compliance can damage an organization’s reputation and lead to loss of customer trust.
“The security and compliance of Intune lock screen images is a critical concern for organizations. Failure to properly manage and secure these images can result in data breaches, regulatory non-compliance, and reputational damage.”
Best Practices for Secure and Compliant Lock Screen Images, How to deploy intune lock screen image
To ensure secure and compliant lock screen images, organizations should follow best practices such as:
- Use secure and compliant image hosting services: Use image hosting services that adhere to security and compliance standards.
- Encrypt sensitive data: Encrypt sensitive data displayed on the lock screen to prevent unauthorized access.
- Implement DLP and Conditional Access: Implement DLP and Conditional Access policies to control access to company resources and protect sensitive data.
Measuring and Monitoring the Effectiveness of Intune Lock Screen Images
Measuring the effectiveness of Intune lock screen images is crucial to understand their impact on user engagement and productivity. This helps in making informed decisions about future deployments and improving the overall user experience.
To measure the effectiveness of Intune lock screen images, it’s essential to track key metrics such as user engagement, error rates, and system crashes. These metrics provide insights into how users interact with the lock screen images and whether they’re having the desired impact on user behavior.
User Engagement Metrics
User engagement metrics are critical in understanding how users interact with the lock screen images. These metrics include:
- User clicks on the lock screen image
- Time spent on the lock screen image
- Number of attempts to bypass the lock screen image
By tracking these metrics, administrators can gauge the effectiveness of the lock screen image in promoting security awareness and reducing unauthorized access to company resources.
Error Rates and System Crashes
Error rates and system crashes can have a significant impact on user productivity and system availability. By tracking these metrics, administrators can identify potential issues with the lock screen image and take corrective action to prevent downtime and data loss.
- Error messages related to the lock screen image
- System crashes caused by the lock screen image
- Number of reboots required to resolve issues related to the lock screen image
By monitoring these metrics, administrators can identify areas for improvement and optimize the lock screen image to reduce errors and system crashes.
Tracking Performance using Azure Monitor and Power BI
Azure Monitor and Power BI provide powerful tools for tracking the performance of Intune lock screen images. These tools enable administrators to collect and analyze data on user engagement metrics, error rates, and system crashes.
“Azure Monitor and Power BI provide real-time insights into user engagement and system performance, enabling administrators to make data-driven decisions about lock screen image deployments.”
When using Azure Monitor and Power BI, administrators can:
- Set up custom dashboards to track key metrics
- Configure alerts for anomalies and issues
- Use data analytics to identify trends and areas for improvement
By leveraging these tools, administrators can gain a deeper understanding of the effectiveness of Intune lock screen images and make informed decisions about future deployments.
Examples of Metric Analysis
Let’s consider an example of how Azure Monitor and Power BI can be used to track the performance of Intune lock screen images.
Imagine an organization that deploys a lock screen image to promote security awareness among its employees. To measure the effectiveness of the lock screen image, the administrator sets up a custom dashboard in Azure Monitor to track user engagement metrics, error rates, and system crashes.
By analyzing these metrics, the administrator can identify areas for improvement and optimize the lock screen image to ensure it achieves its intended goals.
Real-Life Examples
Let’s consider a real-life example of how Intune lock screen images can be used to promote security awareness among employees.
A large financial institution deployed a lock screen image to educate employees about the importance of strong passwords and multi-factor authentication. The lock screen image displayed a message stating, “A strong password protects your account and our organization’s assets. Use a combination of letters, numbers, and special characters to create a unique and secure password.”
To measure the effectiveness of the lock screen image, the administrator tracked user engagement metrics, error rates, and system crashes. The results showed a significant increase in user engagement, with 75% of users viewing the lock screen image and 50% attempting to log in successfully after viewing the message.
The administrator also analyzed the error messages related to user authentication issues. The results revealed that the majority of errors were due to users entering weak passwords, which led to the administrator providing additional training on password best practices.
By analyzing these metrics, the administrator was able to optimize the lock screen image to ensure it effectively promoted security awareness among employees and reduced unauthorized access to company resources.
Conclusion
In conclusion, deploying Intune lock screen images requires careful planning and execution. By following the steps Artikeld in this article, you can ensure a successful deployment that enhances the user experience and increases productivity. Additionally, don’t forget to consider security and compliance requirements, as well as measuring and monitoring the effectiveness of your lock screen images.
Question & Answer Hub
What are the benefits of customizing Intune lock screen images?
Customizing Intune lock screen images can enhance the user experience and increase productivity, as well as provide a professional appearance for your organization.
How do I deploy Intune lock screen images to large-scale environments?
You can deploy Intune lock screen images to large-scale environments using Azure AD and Microsoft Intune. To do this, you will need to follow a step-by-step guide, which includes assigning the necessary permissions and roles to Intune administrators.
What are the security and compliance requirements for Intune lock screen images?
Intune lock screen images must comply with Data Loss Prevention (DLP) and Conditional Access requirements. Failure to comply with these requirements can result in serious security and compliance risks.