How to disable TLS in Linux, the answer to a question that has sparked debate among experts for years. Disabling TLS may seem like a drastic measure, but it can be a necessary step in certain situations. In this article, we will delve into the implications of disabling TLS, the potential risks and vulnerabilities associated with it, and the steps involved in doing so.
We will also explore the different configuration files and directories involved, such as /etc/ssl/ and /etc/hosts, and provide guidance on how to modify the system to prevent TLS from loading.
Understanding the Implications of Disabling TLS in Linux
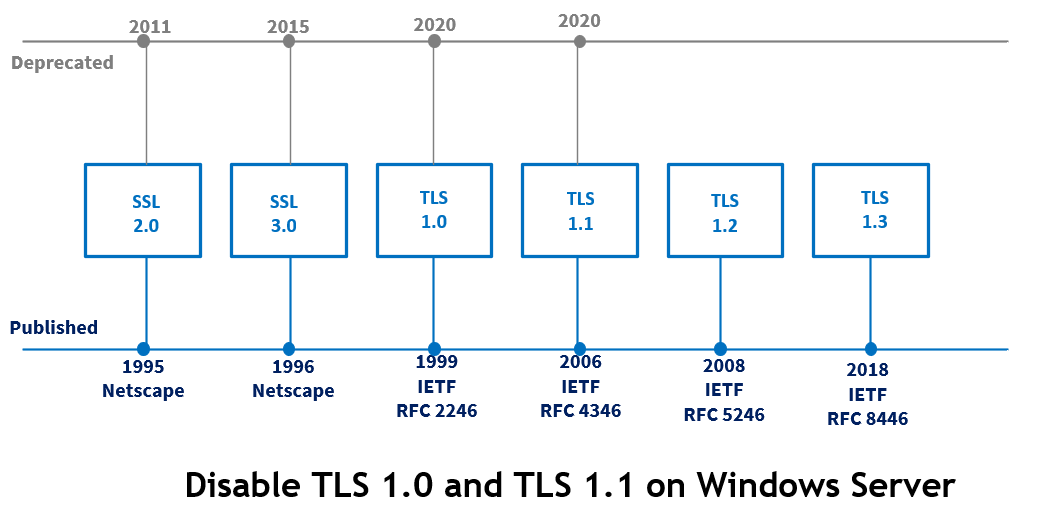
In the realm of secure data transmission, Transport Layer Security (TLS) stands tall as the stalwart encryption protocol that protects online communications. However, some situations may necessitate disabling TLS, albeit with trepidation. Before delving into the nitty-gritty, let’s explore the fundamental differences between TLS and other encryption protocols.
TLS operates at the application layer, encapsulating data in a secure envelope to ensure confidentiality and integrity. It utilizes asymmetric key cryptography for key exchange and symmetric key encryption for data encryption. This two-layered approach provides unyielding protection against eavesdropping and tampering attacks.
In contrast, alternative encryption protocols, such as Secure Sockets Layer (SSL), operate similarly to TLS but have been largely deprecated in favor of the more robust TLS standard. Other protocols, like Internet Protocol Security (IPSec), focus on encrypting entire network communications at the network layer, rather than individual applications.
Potential Risks and Vulnerabilities
Disabling TLS exposes a Linux system to a multitude of risks and vulnerabilities. When TLS is down, data transmission becomes susceptible to:
- Eavesdropping attacks: As data sent over an unencrypted channel is readily accessible to potential interceptors, confidentiality is compromised.
- Tampering attacks: Malicious actors can inject or modify data during transmission, compromising data integrity and potentially leading to devastating consequences.
- Man-in-the-middle (MitM) attacks: Attackers can intercept and modify sensitive information, such as login credentials or financial data.
Situations Where Disabling TLS Might Be Considered
Although not recommended, there are specific scenarios where disabling TLS might be considered, albeit with extreme caution:
- Legacy System Upgrade: In situations where upgrading to a compatible TLS version is not feasible, disabling TLS might be a temporary solution to ensure system continuity.
- Development Environment: In controlled development environments, TLS might be disabled to expedite testing and debugging processes. However, this should be implemented with strict access controls and security measures in place.
- Specialized Network Requirements: In isolated networks with specific security requirements, disabling TLS might be necessary to facilitate communication between systems. In such cases, alternative encryption protocols or custom implementations should be used.
Guidance on Mitigating Risks and Implementing Alternative Security Measures
To mitigate the risks associated with disabling TLS, it is essential to:
-
Implement alternative encryption protocols or custom solutions that prioritize data confidentiality and integrity.
i.e, IPsec, SSL (if absolutely necessary), or custom cryptographic implementations.
-
Establish strict access controls to prevent unauthorized access to sensitive data and system resources.
i.e, IP address filtering, user account management, and permission-based access control.
-
Monitor system activity and enforce regular security audits to detect potential vulnerabilities or attacks.
i.e, system logging, intrusion detection, and vulnerability scanning.
When disabling TLS, it is crucial to weigh the risks against potential benefits, ensuring that alternative security measures are implemented to maintain data confidentiality and integrity.
System Configuration for Disabling TLS in Linux
Disabling TLS (Transport Layer Security) in Linux involves modifying various system configuration files to prevent TLS from loading. This process requires careful consideration and a thorough understanding of the underlying system configuration.
The Role of Certificate Files
Certificate files play a crucial role in the TLS protocol. They are used to authenticate servers and clients and to establish trust. In Linux, certificate files are stored in the `/etc/ssl/` directory. To disable TLS, you need to modify these certificate files or remove them altogether.
The `/etc/ssl/` directory contains various certificate files used by the OpenSSL library.
To modify the certificate files, you can use a text editor such as `vi` or `nano`. Here are the steps to modify the certificate files:
– Open the `/etc/ssl/openssl.cnf` file using a text editor.
– Comment out the lines related to the TLS certificate files by adding a semicolon at the beginning of each line.
– Save the changes to the file.
Alternatively, you can remove the certificate files altogether by deleting them from the `/etc/ssl/` directory. However, be cautious when removing files, as this may cause issues with other system components.
Modifying the OpenSSL Configuration
In addition to modifying the certificate files, you also need to modify the OpenSSL configuration file to prevent TLS from loading.
– Open the `/etc/ssl/openssl.cnf` file using a text editor.
– Add the following lines to the end of the file:
[system_default] tls = false
– Save the changes to the file.
This will prevent the OpenSSL library from loading TLS.
Disabling TLS in System Services
Many system services use TLS to establish secure connections. To disable TLS in these services, you need to modify their configuration files or use alternative protocols.
– Open the `/etc/httpd/conf/httpd.conf` file using a text editor (for Apache HTTP Server).
– Comment out the lines related to TLS by adding a semicolon at the beginning of each line.
– Save the changes to the file.
Alternatively, you can use the `setssl` command to disable TLS in the Apache HTTP Server.
– Open a terminal and run the following command:
setssl -a NONE /etc/httpd/conf/httpd.conf
This will disable TLS for the Apache HTTP Server.
Customizing System Configuration
Customizing system configuration to accommodate specific use cases may require modifying various configuration files or adding new configuration options.
– Open the `/etc/ssl/openssl.cnf` file using a text editor.
– Add a new section to the file that specifies the custom configuration options.
Here’s an example of a custom configuration:
[custom_config] tls = true verify = false
– Save the changes to the file.
This will enable TLS with custom configuration options.
Compiling and Installing Custom Libraries for TLS
Compiling and installing custom libraries is a crucial step in enabling alternative encryption protocols in a Linux system. This process involves modifying the system’s libraries to support specific encryption methods, which can be essential for certain applications or use cases. By compiling and installing custom libraries, system administrators can extend the functionality of their Linux systems and enable support for a wide range of encryption protocols.
Patching the Linux Kernel for TLS Support
To patch the Linux kernel and add custom TLS support, system administrators must first navigate to the kernel source directory and apply a patch that enables TLS support. This typically involves running a series of commands to apply the patch and recompile the kernel. Once the patch is applied, system administrators must rebuild the kernel and install the new version on the system. When patching the Linux kernel, it’s essential to consider the potential implications on the system’s stability and security.
Compiling and Installing Custom Libraries
Compiling and installing custom libraries involves several steps, including retrieving the source code for the desired library, configuring the build process, and compiling the code. System administrators must then install the custom library on their system and ensure that it’s properly configured for use. In some cases, custom libraries may require manual configuration to function correctly. This can include modifying system configuration files or setting environment variables.
- Retrieving the source code: The first step in compiling a custom library is to retrieve the source code for the desired library. This can typically be done using a version control system such as Git or by downloading the source code directly from a repository.
- Configuring the build process: Once the source code is retrieved, system administrators must configure the build process for the custom library. This typically involves running a series of commands to set up the build environment and specify the build options.
- Compiling the code: After configuring the build process, system administrators must compile the source code for the custom library. This typically involves running a command such as `make` to build the library.
- Installing the library: Once the custom library is compiled, system administrators must install it on their system. This typically involves running a command such as `make install` to copy the library to the correct location.
Examples of Libraries that can be Compiled and Installed
Several libraries can be compiled and installed to support alternative encryption protocols in a Linux system. Some examples include:
- TLS-PSK: This library provides support for Pre-Shared Key (PSK) authentication in TLS connections.
- TLS-ECDSA: This library provides support for Elliptic Curve Digital Signature Algorithm (ECDSA) key exchange in TLS connections.
- TLS-SRP: This library provides support for Secure Remote Password (SRP) authentication in TLS connections.
Potential Complications and Caveats, How to disable tls in linux
Compiling and installing custom libraries can be a complex and error-prone process. Some potential complications and caveats include:
- Compatibility issues: Custom libraries may not be compatible with all versions of the Linux kernel or other software components.
- Stability and security risks: Custom libraries can introduce stability and security risks if they are not properly tested and validated.
- Dependency issues: Custom libraries may require specific dependencies to function correctly, which can lead to version conflicts or other issues.
Blockchain-based Secure Communication with TLS
Blockchain-based secure communication involves using a distributed ledger technology to establish secure communication channels. This approach can provide an additional layer of security and integrity to TLS connections. By leveraging blockchain-based secure communication, system administrators can ensure that sensitive data is protected from tampering or eavesdropping.
Using TLS with Other Encryption Protocols
TLS can be used in conjunction with other encryption protocols to provide an additional layer of security. For example, TLS can be used with encryption protocols such as IPSec or PGP to provide end-to-end encryption for sensitive data. By combining multiple encryption protocols, system administrators can create a secure communication channel that is resistant to eavesdropping and tampering.
Compatibility and Interoperability Considerations: How To Disable Tls In Linux
Disabling TLS in a Linux system may lead to compatibility and interoperability issues with various devices and systems that rely on secure connections to function seamlessly. This is particularly crucial in today’s internet-connected landscape, where devices ranging from home appliances to industrial control systems often communicate with the internet and each other through secure protocols like HTTPS and TLS.
Impact on IoT Devices
IoT devices, which comprise a significant portion of modern smart home and industrial automation systems, heavily rely on secure connections to ensure seamless communication with their respective servers and other devices. Disabling TLS in a Linux system may lead to connectivity issues with these devices, compromising their usability and potentially exposing users to various security risks such as man-in-the-middle attacks and unauthorized data exfiltration. In IoT devices, this may result in unpredictable behavior, including incorrect commands, unexpected data, or even physical harm.
- Device Manufacturers’ Documentation: Review device manufacturers’ documentation for specific instructions on configuring connections without TLS. Some devices may have workarounds or dedicated settings for non-secured connections.
- Device Firmware Updates: Regularly update device firmware to ensure the latest security patches and features are installed, which may mitigate the need for disabling TLS.
- Alternative Protocols: Investigate and implement alternative protocols that offer equivalent or superior security to TLS, such as DTLS (Datagram Transport Layer Security) for IoT devices.
Troubleshooting Connectivity Issues
When troubleshooting connectivity issues with IoT devices or other systems that rely on TLS, it’s essential to methodically approach the problem. Start by checking the basic network configuration, ensuring the device is properly configured and connected to the network. Next, investigate the server-side, verifying that the server is set up to communicate securely. If issues persist, attempt to configure alternative protocols, such as DTLS, or consult device manufacturers’ documentation for workarounds.
“Error messages often indicate the root cause of the connectivity issue. Analyze these messages carefully to pinpoint the problem and apply targeted solutions.”
Designing Alternative Protocols and Adapting Current Infrastructure
Designing alternative protocols or adapting current infrastructure to optimize interoperability requires a deep understanding of the underlying systems and their security requirements. When designing new protocols, consider factors like encryption modes, key exchange algorithms, and authentication mechanisms to ensure equivalent or superior security to TLS. For adapting current infrastructure, carefully evaluate the trade-offs between security, performance, and maintainability. Consider implementing cryptographic co-processors or specialized security chips to enhance performance and reduce the computational overhead of encryption and decryption.
- Performance Impact Assessment: Carefully evaluate the performance impact of disabling TLS or implementing alternative protocols on the system and its components.
- Security Review: Conduct a thorough security review of the alternative protocol or adapted infrastructure to ensure it meets or exceeds the security requirements of the system.
- Compatibility Testing: Perform rigorous compatibility testing to ensure seamless interaction with other systems and devices, both within and outside the organization.
Concluding Remarks
In conclusion, disabling TLS in Linux requires careful consideration and planning. While it may be necessary in certain situations, it can also expose systems to potential risks and vulnerabilities. It is essential to weigh the trade-offs and take necessary precautions to mitigate potential risks and implement alternative security measures.
Detailed FAQs
What are the potential security risks of disabling TLS in Linux?
Disabling TLS in Linux can expose systems to man-in-the-middle attacks, eavesdropping, and interception of sensitive data.
Can I still use SSL instead of TLS?
Yes, you can use SSL instead of TLS, but keep in mind that SSL is an older protocol and may not provide the same level of security as TLS.
How do I ensure seamless communication within the Linux system despite TLS disabling?
Ensure that all applications and services using TLS are upgraded or reconfigured to use the new protocol.
What are the potential implications on device connectivity and IoT devices?
Disabling TLS may affect device connectivity and IoT device functionality, especially if they rely on TLS for secure communication.
Can I compile and install custom libraries to support TLS in a Linux system?
Yes, but it involves compiling and installing custom libraries, which can be complex and may pose security risks if not done properly.