As how to implement BYOK takes center stage, this opening passage beckons readers into a world of cloud computing and key management systems, crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original.
The concept of Bring Your Own Key (BYOK) has gained significant attention in the world of cloud computing, allowing organizations to take control of their encryption keys and ensuring the security and integrity of their data. BYOK is designed to provide organizations with the flexibility to use their own encryption keys, managed by a key management system, to encrypt and decrypt their data in the cloud.
Understanding the Basics of BYOK
Imagine having the keys to a high-security safe, but instead of physical keys, it’s a digital code that only you possess. This is the essence of BYOK (Bring Your Own Key) – a concept that allows individuals or organizations to manage their own encryption keys, giving them unparalleled control over their sensitive data.
BYOK is a game-changer in the world of cloud computing, enabling companies to maintain strict security standards while still utilizing the benefits of cloud storage. By leveraging BYOK, organizations can ensure their data remains encrypted, even when stored outside their premises. This approach not only protects data from unauthorized access but also provides an added layer of compliance with regulatory requirements.
Main Reasons for Adopting BYOK, How to implement byok
Companies are adopting BYOK for several compelling reasons:
- Improved Security: BYOK provides an additional layer of security, ensuring that data remains encrypted even in the event of a security breach.
- Control and Autonomy: BYOK allows organizations to manage their encryption keys, giving them complete control over their data.
- Compliance: BYOK helps organizations meet regulatory requirements, especially in industries with stringent data protection standards.
- Flexibility: BYOK enables organizations to switch cloud service providers without compromising security or compliance.
Types of Keys Used in BYOK
There are primarily two types of keys used in BYOK:
- Symmetric Keys: These keys are used for both encryption and decryption. Examples include AES (Advanced Encryption Standard) keys.
- Asymmetric Keys: These keys consist of a pair: a public key for encryption and a private key for decryption. Examples include RSA (Rivest-Shamir-Adleman) keys.
Characteristics of a Secure Key Management System
A secure key management system is the backbone of BYOK. It should possess the following key characteristics:
- Encryption: The system should provide robust encryption methods, such as AES, to protect sensitive data.
- Key Storage: The system should securely store and manage encryption keys, using techniques like Hardware Security Modules (HSMs) or secure key stores.
- Access Control: The system should ensure that only authorized personnel have access to encryption keys and sensitive data.
- Auditing and Logging: The system should maintain detailed records of all key management transactions, ensuring that any security breaches can be swiftly detected and addressed.
- Scheme Flexibility: The system should be capable of supporting a variety of encryption schemes, including BYOK and hybrid approaches.
Key Establishment and Management: How To Implement Byok

In the realm of Bring Your Own Key (BYOK), establishing and managing secure keys is a crucial aspect that ensures the integrity and confidentiality of cryptographic operations. Effective key establishment and management processes are essential to prevent unauthorized access and minimize the risk of key compromise.
Key establishment is the process by which a shared secret key is generated and distributed between two parties. In the context of BYOK, this process involves creating and managing the cryptographic keys used for authentication and encryption. Proper key establishment ensures that sensitive data remains protected, even in the event of a security breach.
Designing a Secure Key Establishment Process
A secure key establishment process involves several steps:
- Key Pair Generation: The client generates a key pair, consisting of a private key and a public key, using a secure random number generator. The private key is kept confidential, while the public key is shared freely.
- Key Exchange: The client shares its public key with the server, which verifies the key to ensure that it is authentic and has not been tampered with.
- Key Negotiation: The client and server negotiate the key exchange protocol, agree on the cryptographic parameters, and establish the shared secret key.
- Key Activation: The shared secret key is used to activate the cryptographic operations, such as encryption and decryption.
The key establishment process should be designed to ensure the security and confidentiality of the shared secret key, as well as to prevent any potential vulnerabilities that could compromise the entire system.
Key Management Techniques Used in BYOK
Several key management techniques are employed in BYOK to ensure the security and integrity of cryptographic keys:
- Key Hierarchy: A hierarchical key structure is used to manage multiple levels of keys, including root keys, intermediate keys, and leaf keys.
- Key Escrow: A key escrow mechanism is used to store and manage cryptographic keys, allowing for secure access in case of a key compromise or loss.
- Key Revocation: A key revocation mechanism is used to invalidate compromised or outdated keys, ensuring that they are no longer used for cryptographic operations.
- Key Rotation: A key rotation mechanism is used to periodically update and replace key material, preventing unauthorized access and minimizing the risk of key compromise.
These key management techniques are designed to work together to ensure the security and integrity of cryptographic keys in BYOK.
The Role of Key Rotation and Revocation
Key rotation and revocation are essential components of BYOK, ensuring that compromised or outdated keys are replaced and invalidated to prevent unauthorized access and minimize the risk of key compromise.
Key rotation involves periodically updating and replacing key material to prevent unauthorized access and minimize the risk of key compromise. This ensures that any potential vulnerabilities or weaknesses in the existing key material are addressed, and the system remains secure.
Key revocation involves invalidating compromised or outdated keys, ensuring that they are no longer used for cryptographic operations. This prevents unauthorized access and ensures that the system remains secure and trustworthy.
Example of a Key Management System Used in BYOK
A popular key management system used in BYOK is the HashiCorp Vault. HashiCorp Vault is a secure key management system designed to store, manage, and retrieve cryptographic keys. The system utilizes a hierarchical key structure, key escrow, and key revocation mechanisms to ensure the security and integrity of cryptographic keys.
The system allows for secure key generation, sharing, and rotation, ensuring that keys are kept confidential and up-to-date. HashiCorp Vault also provides advanced features, such as key auditing, monitoring, and reporting, to ensure that the system remains secure and trustworthy.
“A secure BYOK implementation requires a robust key establishment process, effective key management techniques, and regular key rotation and revocation procedures.”
Integration with Cloud Services
As organizations increasingly rely on cloud services to store and process sensitive data, implementing Bring Your Own Key (BYOK) becomes a crucial step in ensuring the security and integrity of that data. Integration with cloud services is a critical aspect of BYOK, allowing organizations to manage keys and protect data in the cloud. In this section, we will delve into the steps involved in integrating BYOK with cloud services, compare the integration processes of different cloud service providers, and discuss the security implications of such integration.
Steps Involved in Integrating BYOK with Cloud Services
To integrate BYOK with cloud services, organizations must follow a series of steps:
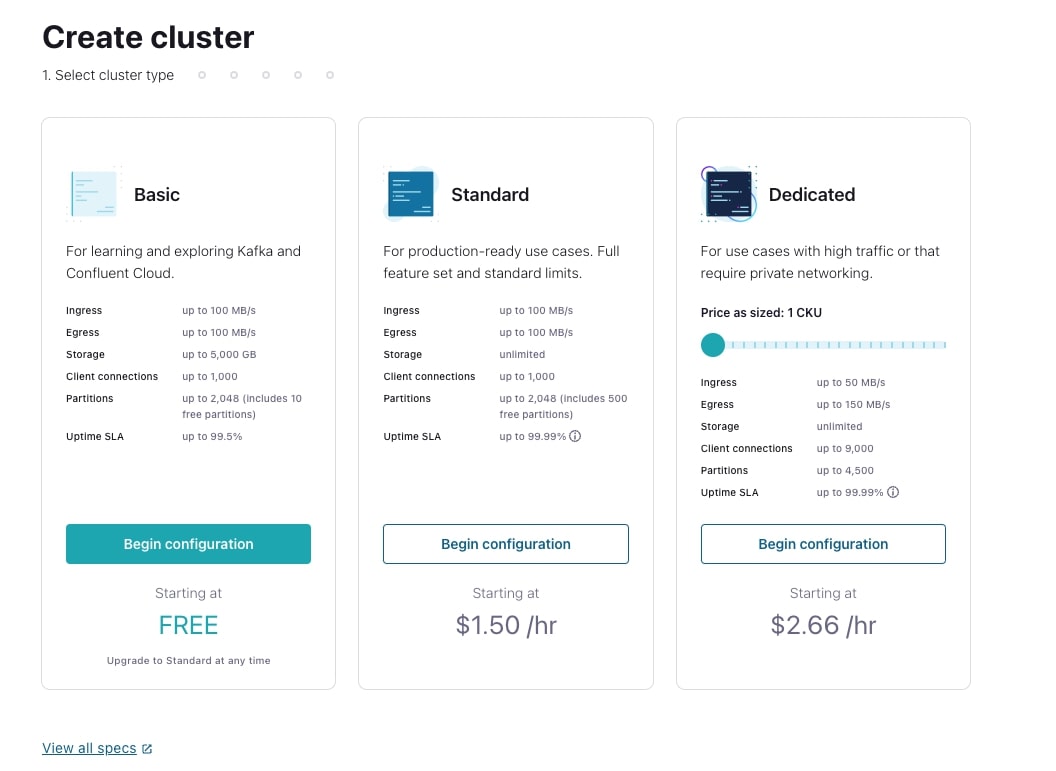
- Choose a cloud service provider (CSP) that supports BYOK: Not all CSPs support BYOK, so it is essential to select a provider that offers this feature.
- Generate and store keys: Organizations must generate and store keys securely outside of the cloud, using a key management system (KMS) or a similar solution.
- Configure the CSP: The organization must configure the CSP to use the BYOK service, which typically involves uploading the organization’s public key to the CSP.
- Encrypt data in the cloud: Once the CSP is configured, the organization can encrypt data in the cloud using the BYOK service.
- Decrypt data: The organization can decrypt data in the cloud using the private key stored securely outside of the cloud.
Comparison of Integration Processes across Different Cloud Service Providers
Each cloud service provider (CSP) has its own integration process for BYOK, which can be complex:
- AWS Key Management Service (KMS): AWS provides a comprehensive guide for integrating BYOK with their services, but the process requires significant configuration and setup.
- Azure Key Vault: Azure offers a more streamlined process for integrating BYOK, but the organization must provide the necessary public keys and configure the Azure Key Vault accordingly.
- Google Cloud Key Management Service (KMS): Google Cloud provides a robust BYOK service, but the organization must generate and manage keys securely using a KMS or similar solution.
Security Implications of Integrating BYOK with Cloud Services
Integrating BYOK with cloud services offers several security benefits, including:
- Key management: Organizations maintain control over keys, reducing the risk of unauthorized access to sensitive data.
- Data encryption: BYOK ensures that data is encrypted in the cloud, protecting it from unauthorized access or exposure.
- Compliance: BYOK helps organizations meet regulatory requirements and industry standards for secure data handling.
Importance of Proper Configuration and Setup of BYOK in Cloud Services
To ensure the effective integration of BYOK with cloud services, organizations must:
- Configure the CSP correctly: The organization must configure the CSP to use the BYOK service, which involves uploading public keys and setting up proper encryption and decryption processes.
- Implement key rotation: Regular key rotation is essential to maintain the integrity of the BYOK service and prevent potential security risks.
- Monitor and audit: The organization must monitor and audit the BYOK service to detect any potential security threats and maintain compliance with regulatory requirements.
Ending Remarks
Implementing BYOK requires a deep understanding of key establishment, management, and rotation, as well as the integration of BYOK with cloud services and the monitoring of system performance. By following the best practices and guidelines Artikeld in this article, organizations can successfully implement BYOK and ensure the secure storage and management of their data in the cloud.
Frequently Asked Questions
What is BYOK and why is it important?
BYOK is a concept in cloud computing where organizations bring their own encryption keys to manage their data in the cloud. It’s important because it gives organizations control over their encryption keys, ensuring the security and integrity of their data.
What are the key characteristics of a secure key management system?
A secure key management system used in BYOK should have features such as key rotation, revocation, and access controls to ensure the security of encryption keys.
How do I integrate BYOK with cloud services?
Integrating BYOK with cloud services involves following the steps Artikeld in the article, including key establishment, management, and rotation, as well as the monitoring of system performance.
What are the benefits of implementing BYOK?
The benefits of implementing BYOK include improved data security, control, and compliance with regulatory requirements.