How to program nfc tags –
how to program nfc tags sets the stage for this enthralling narrative, offering readers a glimpse into a world that is rich in detail and brimming with originality from the outset. With the rise of the Internet of Things (IoT), NFC tags have become an essential component in the development of smart devices, providing a simple and efficient way to transfer data between devices.
The importance of having a solid understanding of NFC tag programming cannot be overstated, particularly when creating IoT devices that require secure and reliable data transmission. NFC tags in IoT applications offer several benefits, including improved accessibility and reduced energy consumption. In this article, we will delve into the world of NFC tag programming, exploring the different types of NFC tags, their applications, and how to program them.
Introduction to NFC Tag Programming for IoT Devices
As the Internet of Things (IoT) continues to evolve, NFC (Near Field Communication) tags have become an essential component in the development of IoT devices. These small, wireless devices enable devices to communicate and transfer data between each other seamlessly. NFC tags have revolutionized the way IoT devices interact, providing a simple and efficient way to transfer data.
The importance of understanding NFC tag programming cannot be overstated, especially when it comes to creating IoT devices that require secure and reliable data transmission. NFC tags are designed to provide a secure and private communication channel between devices, making them an attractive solution for applications that require high levels of security. With the rise of IoT, the importance of secure data transmission has become increasingly crucial, making NFC tags an essential tool for IoT developers.
Benefits of Using NFC Tags in IoT Applications, How to program nfc tags
One of the primary benefits of using NFC tags in IoT applications is improved accessibility. NFC tags allow devices to communicate with each other wirelessly, eliminating the need for cables or physical connections. This makes it easier for devices to share data and communicate with each other, enabling more seamless interactions between devices. Additionally, NFC tags consume very little energy, making them an attractive solution for applications that require low power consumption.
Secure Data Transmission
NFC tags provide a secure way to transmit data between devices, using advanced encryption algorithms to protect sensitive information. This ensures that data is transmitted securely and privately, reducing the risk of unauthorized access or data breaches. By using NFC tags, IoT developers can ensure that their devices are able to share data securely, providing an added layer of protection for sensitive information.
Real-World Examples of NFC Tags in IoT Applications
NFC tags are used in a variety of IoT applications, ranging from smart home devices to wearables and medical devices. For example, NFC tags are used in smart home systems to enable devices to communicate with each other and control lighting, temperature, and security systems. Wearables, such as fitness trackers and smartwatches, use NFC tags to enable users to securely transfer data to their devices. Medical devices, such as insulin pumps and glucose monitors, use NFC tags to enable secure data transfer between devices.
Challenges of NFC Tag Programming
While NFC tags offer numerous benefits for IoT applications, they also come with their own set of challenges. One of the main challenges is programming the NFC tags, as this requires a strong understanding of NFC programming protocols and technologies. Additionally, NFC tags are prone to interference from other wireless devices, which can affect their performance and security.
NFC Tag Programming Protocols
There are several NFC tag programming protocols available, each with its own strengths and weaknesses. Some of the most popular protocols include:
- NFC Forum Type 2 Tag
- NFC Forum Type 4 Tag
- NFC-A Tag
- NFC-F Tag
Each protocol has its own set of features and limitations, and choosing the right protocol for your IoT application requires a thorough understanding of the specific requirements of your project.
Conclusion
In conclusion, NFC tags are a crucial component in IoT device development, providing a secure and efficient way to transfer data between devices. With their numerous benefits and challenges, NFC tags require a solid understanding of NFC programming protocols and technologies. By mastering NFC tag programming, IoT developers can create secure, efficient, and reliable IoT applications that improve the lives of users around the world.
Understanding NFC Tag Technologies and Form Factors
NFC tags have revolutionized the way we interact with IoT devices, enabling seamless communication and data exchange between devices. With numerous types of NFC tags available, it’s essential to understand the differences between them, including their advantages and disadvantages. In this section, we’ll delve into the world of NFC tag technologies and form factors, exploring the various components and applications that make them so versatile.
NFC Tag Types
NFC tags can be broadly classified into three categories: passive, active, and hybrid tags. Each type has its unique characteristics, advantages, and disadvantages.
– Passive NFC Tags: These tags do not have a built-in power source and rely on the reader’s electromagnetic field to transmit and receive data. They are inexpensive, widely available, and offer a simple solution for basic applications. Examples of passive NFC tags include stickers and smart labels.
– Active NFC Tags: Unlike passive tags, active NFC tags have a built-in battery and can perform more complex operations. They can store and process data, respond to multiple commands, and even initiate connections between devices. Active tags are more expensive than passive tags but offer greater functionality and flexibility.
– Hybrid NFC Tags: As the name suggests, hybrid tags combine the benefits of both passive and active tags. They have a built-in power source, but it can be recharged or extended using external power sources. Hybrid tags offer a balance between cost and functionality, making them suitable for applications that require higher performance.
NFC Tag Form Factors
NFC tags come in a variety of form factors, from simple stickers to more complex designs like wristbands and badges. Each form factor has its unique advantages and applications.
– Stickers and Smart Labels: These are the most common type of NFC tag, used for basic applications like product authentication, inventory management, and tracking.
– Wristbands and Badges: These form factors are used for more complex applications, such as wearable devices, ID cards, and loyalty programs.
– Creative Designs: NFC tags can be designed and manufactured in various shapes and sizes, enabling creative applications like artistic installations, interactive exhibits, and promotional materials.
NFC Tag Components
An NFC tag consists of three primary components: the antenna, microcontroller, and memory module. Understanding these components is crucial for designing and implementing effective NFC tag solutions.
– Antenna: The antenna is responsible for transmitting and receiving data between the NFC tag and the reader device. It is usually made of a conductive material, such as copper or aluminum.
– Microcontroller: The microcontroller processes and stores data within the NFC tag. It is a small computer that executes instructions and manages the tag’s functionality.
–
The memory module is responsible for storing data within the NFC tag. It can be a type of flash memory or a magnetic storage device.
These components work together to enable seamless communication between NFC tags and reader devices, making them an essential part of IoT ecosystems.
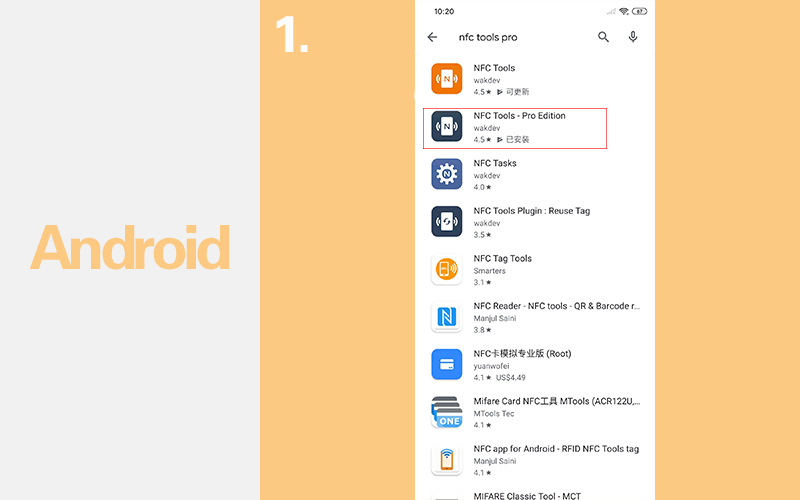
Programming NFC Tags with Android Devices
Programming NFC tags with an Android device using the Android Beam feature is a convenient way to share data and interact with nearby devices. Android Beam, also known as Android’s NFC transfer option, enables seamless data transfer between NFC-enabled devices. This feature, coupled with NFC tag programming capabilities, allows users to create customized interactions and experiences with various devices and systems.
Selecting the Tag’s Operating System
When creating a custom NFC tag using an Android app, one of the first steps is to select the tag’s operating system. Most NFC tags operate within a specific platform or framework, such as Android, iOS, or third-party platforms like NXP or STMicroelectronics. Each operating system has its set of features, functions, and limitations, which users must consider when choosing the appropriate tag for their needs. For instance, if the goal is to create a tag that can be easily read and written by both Android and iOS devices, users may opt for a tag that supports a cross-platform operating system like NXP’s NTAG213 or STMicroelectronics’ VL663.
Programming the Tag’s Contents
Once the tag’s operating system has been selected, the next step is to program the tag’s contents. This can be done using a dedicated Android app specifically designed for NFC tag programming. Typically, these apps provide a user-friendly interface for selecting the tag’s operating system, setting up the tag’s configuration, and writing the desired data onto the tag. Some popular options for tag programming apps include NFC Tools, TagWriter, and Android Beam. When programming the tag’s contents, users have the option to store various types of data, such as text, images, audio files, and even executable code.
Difference Between Reading and Writing NFC Tags
When interacting with NFC tags using an Android device, users must differentiate between reading and writing NFC tags. Reading a tag involves collecting the stored data from the tag and displaying or using it on the device. Writing a tag, on the other hand, involves creating a new set of data and storing it onto the tag for future access. Each scenario has its own set of considerations, including data storage capacity, data format, and compatibility between devices. For instance, when reading an NFC tag, users expect to retrieve pre-existing data that might have been written by another device or system.
Practical Examples of Reading and Writing NFC Tags
To illustrate these concepts, consider the following examples:
– Example 1: A user creates a customized business card using a tag with a unique QR code. They scan the tag with their Android device to read the stored data, which triggers a pre-programmed action, such as opening a specific app or web page.
– Example 2: A user purchases a tag with a pre-configured app that allows remote monitoring of a device or sensor. When they write the tag using their Android device, the pre-configured app is executed, and real-time data can be accessed from a remote location.
Designing Secure NFC Tag Applications
In today’s digital age, security is a top priority, especially when it comes to storing sensitive information on NFC tags. As IoT devices continue to grow in popularity, ensuring that NFC tags are secure and compliant with industry standards has become increasingly important. In this section, we will discuss the importance of secure NFC tag applications and provide guidance on designing a secure system.
Importance of Secure NFC Tags
Secure NFC tags are crucial in protecting sensitive information, such as payment data, personal identifiable information (PII), and other confidential data. Unsecured NFC tags can lead to serious consequences, including data breaches and unauthorized access. According to the Payment Card Industry Data Security Standard (PCI DSS), all merchants and service providers handling credit card information must implement security measures to protect this sensitive data.
- Data Breaches: If an NFC tag is compromised, sensitive information stored on it can be accessed by unauthorized individuals, leading to a data breach. This can result in financial losses, damage to reputation, and legal penalties.
- Unauthorized Access: Unsecured NFC tags can be easily rewritten or modified by anyone, allowing them to gain access to sensitive information or even inject malicious code into the system.
- Financial Losses: Data breaches and unauthorized access can result in significant financial losses, including fines, restitution, and losses due to stolen information.
Design Pattern for a Secure NFC Tag Application
A secure NFC tag application should include authentication, encryption, and data validation. Here’s a design pattern to follow:
Authentication
Authentication ensures that only authorized users can access the NFC tag. This can be achieved through various methods, including:
- Password Protection: Assign a unique password to each NFC tag, requiring users to enter the correct password to access the tag.
- Biometric Authentication: Use biometric features like fingerprint or facial recognition to authenticate users.
li>Public Key Infrastructure (PKI): Use PKI to issue digital certificates to users, allowing them to securely access the NFC tag.
Encryption
Encryption ensures that sensitive information stored on the NFC tag is protected from unauthorized access. This can be achieved through various encryption algorithms, including:
- Advanced Encryption Standard (AES): A widely used encryption algorithm that is secure and efficient.
- RSA Encryption: A public-key encryption algorithm that is widely used for secure data transmission.
Data Validation
Data validation ensures that sensitive information stored on the NFC tag is accurate and up-to-date. This can be achieved through various methods, including:
- Data Integrity Checks: Regularly check the integrity of sensitive information stored on the NFC tag.
- Version Control: Maintain a version control system to ensure that sensitive information is updated correctly.
The primary goal of a secure NFC tag application is to protect sensitive information from unauthorized access and ensure that only authorized users can access the tag. By implementing authentication, encryption, and data validation, you can design a secure system that meets industry standards and protects sensitive information.
Integrating NFC Tags with Microcontrollers
Integrating NFC tags with microcontrollers is a crucial step in creating IoT devices that can read and write data to tags. This integration enables devices to communicate with the physical world and perform tasks based on the data they read from NFC tags. This process can be achieved with various microcontrollers, including Arduino and Raspberry Pi, each with their benefits and limitations.
One of the primary reasons for choosing microcontrollers for NFC integration is their ability to provide low-power consumption and small form factors. This allows for devices that can be powered by batteries for extended periods, making them ideal for applications such as wearable devices and IoT sensors. The ease of use and extensive libraries available for microcontrollers like Arduino and Raspberry Pi make them a popular choice for developers.
Choosing Microcontrollers for NFC Tag Integration
When selecting a microcontroller for NFC integration, several factors must be considered. The first consideration is power consumption, as the microcontroller will be responsible for powering the NFC module. Some popular options for low-power microcontrollers include the ESP32, ESP8266, and the SAMD21.
Microcontrollers Comparison Table
| Microcontroller | Power Consumption (mA) | Price (USD) | Ease of Use |
| — | — | — | — |
| ESP32 | 20-50 | 10-20 | High |
| ESP8266 | 20-50 | 5-15 | Medium |
| SAMD21 | 5-10 | 5-10 | Medium |
The microcontroller also needs to support NFC communication protocols such as NDEF and MIFARE. The ESP32, for example, supports NFC communication through its built-in SPI interface, making it an ideal choice for developers.
Optimizing NFC Tag Communication
To optimize NFC tag communication with microcontrollers, techniques such as low-power mode and data buffering can be employed. Low-power mode reduces the power consumption of the microcontroller, allowing it to read tags for longer periods without draining the battery. Data buffering enables the microcontroller to store data read from the tag and process it when the device is in a low-power state.
Low-Power Mode Techniques
Use the microcontroller’s built-in timers to put the device in a power-saving mode after a certain period of inactivity.
Data buffering can be achieved by using a small amount of memory to store the data read from the tag. When the device is in a low-power state, it can retrieve the data from memory and process it.
Data Buffering Techniques
Use a small amount of EEPROM or SRAM to store the data read from the tag.
By employing these techniques, developers can create IoT devices that can efficiently communicate with NFC tags, reducing power consumption and increasing the device’s lifespan.
-
Use the microcontroller’s SPI interface to communicate with NFC tags.
-
Configure the microcontroller’s interrupts to handle NFC events.
-
Use a separate power source for the NFC module to reduce power consumption.
Using NFC Tags for Data Transfer and Authentication
NFC tags have revolutionized the way we transfer data between devices, and their use in authentication systems has become increasingly popular. With the rise of IoT devices and mobile payments, the need for secure and convenient data transfer and authentication methods has never been more pressing. NFC tags offer a seamless and secure solution for both data transfer and authentication purposes.
Data Transfer between Devices
NFC tags enable data transfer between devices by using radiofrequency signals to communicate. This technology allows users to transfer files, contacts, and other data between devices simply by tapping them together. Additionally, NFC tags can be used to transfer encrypted data, ensuring that sensitive information remains secure during transfer.
- Data Encryption: NFC tags support various encryption methods, including AES and DES, to secure data transfer. This ensures that even if the data is intercepted, it will be unreadable.
- Data Validation: NFC tags can also perform data validation checks to ensure that the data being transferred is authentic and has not been tampered with.
Authentication Purposes
NFC tags have become a popular choice for authentication purposes due to their secure and convenient nature. With NFC-based authentication systems, users can securely access secured areas, login to their devices, and even make payments. The use of NFC tags in authentication systems offers several benefits, including increased security, convenience, and speed.
- Secure Login: NFC tags can be used to securely login to devices and systems, eliminating the need for passwords or PINs.
- Access Control: NFC tags can be used to grant or deny access to secured areas, devices, or systems, providing an additional layer of security.
Example of an NFC-based Authentication System
One example of an NFC-based authentication system is a smart door lock that uses a NFC tag to grant access to authorized individuals. When an individual approaches the door, their NFC-enabled device detects the presence of the NFC tag and automatically grants access. If the individual is not authorized, the NFC tag will not function, ensuring that unauthorized individuals cannot gain access to the secured area.
NFC-based authentication systems provide a secure and convenient way to manage access control and login processes, eliminating the need for passwords or PINs.
Outcome Summary

In conclusion, programming NFC tags for smart devices requires a comprehensive understanding of the technology, its applications, and the best practices for secure and reliable data transmission. By following the steps Artikeld in this article, readers can gain valuable insights into the world of NFC tag programming and unlock the full potential of their smart devices.
Quick FAQs: How To Program Nfc Tags
Can I use NFC tags with multiple Android devices?
Yes, NFC tags can be used with multiple Android devices by programming them with the desired data and setting the tag to work in broadcast mode, allowing any Android device to read the tag.
Do I need specialized hardware to program NFC tags?
No, programming NFC tags typically requires only an NFC-enabled device, such as a smartphone or tablet, and a compatible application or tool.
How secure are NFC tags?
The security of NFC tags depends on the level of encryption and authentication used when programming them. Well-designed NFC tag systems can provide robust security, while poorly designed systems can leave devices vulnerable to data breaches and unauthorized access.