Delving into how to stop spam emails, this guide is a must-read for anyone who is tired of receiving unwanted messages. With the rise of technology, spam emails have become a growing concern for individuals and organizations alike, causing financial losses, damaging relationships, and wasting precious time. In this comprehensive guide, we will explore the different types of spam emails, their characteristics, and the strategies that email providers use to combat them.
From phishing and malware to spam filtering and email management tools, we will cover everything you need to know to protect yourself from these unwanted messages. By understanding the nature of spam emails and their impact, you will be equipped with the knowledge to identify and report them, preventing further propagation and maintaining a secure and trustworthy email system.
Understanding the Nature of Spam Emails and Their Impact on Email Users: How To Stop Spam Emails
Spam emails, also known as junk emails or unsolicited commercial emails, have become a significant issue for email users worldwide. These emails are sent in bulk, often with the intention of promoting products, services, or phishing scams. In this section, we will explore the different types of spam emails, their characteristics, and how they affect individuals and organizations.
Spam emails can be categorized into several types, including:
Type 1: Phishing Emails, How to stop spam emails
Phishing emails are designed to trick recipients into revealing sensitive information such as passwords, credit card numbers, or personal data. These emails often appear to come from reputable sources and may include fake logos or official-looking designs. Phishing emails can cause significant financial losses and damage to individuals’ and organizations’ reputations.
For instance, in 2013, the FBI reported a phishing scam that compromised over 2 million email accounts, resulting in significant financial losses for those affected.
Type 2: Spam Advertisements
Spam advertisements are unsolicited emails that promote products or services. These emails often contain links to external websites or attachments that may contain malware. Spam advertisements can cause email inbox clutter and may lead to recipients clicking on malicious links, which can compromise their devices.
A notable example of spam advertisements was the “Nigerian Prince” scam, where scammers sent emails claiming that the recipient had inherited a large sum of money from a Nigerian prince. The recipient was asked to provide banking information to receive the inheritance, but in reality, the recipient would be providing sensitive information to scammers.
Type 3: Malware-Related Emails
Malware-related emails contain malicious software or attachments that can compromise recipients’ devices. These emails often appear to come from reputable sources and may contain fake updates or patches. Malware-related emails can cause significant damage to individuals’ and organizations’ systems and data.
For example, in 2020, a malware campaign was launched that spread malware via spam emails. The malware, known as “Emotet,” infected thousands of devices worldwide, resulting in significant financial losses and damage to individuals’ and organizations’ data.
Type 4: Scam Emails
Scam emails are designed to trick recipients into sending money or goods. These emails often appear to come from reputable sources and may include fake stories or promises. Scam emails can cause significant financial losses and damage to individuals’ and organizations’ reputations.
A notable example of scam emails was the “Grandparent Scam,” where scammers sent emails claiming to be a grandchild in need of money. The recipient was asked to send money to help their grandchild, but in reality, the recipient would be providing money to scammers.
How to Identify and Report Spam Emails to Prevent Further Propagation
Identifying and reporting spam emails is a crucial step in preventing further propagation and protecting email users from potential threats. Spam emails can be malicious, carrying viruses, phishing scams, or other forms of cyber attacks that can compromise personal data, finances, or even entire networks.
To effectively identify spam emails, consider the following characteristics:
- Typographical errors and poor grammar often found in spam emails, such as missing or mismatched words, incorrect punctuation, and awkward sentence structures.
- Urgency tactics, such as threatening or enticing language, designed to prompt immediate action without careful consideration.
- Lack of personalization or irrelevant content, indicating mass email campaigns rather than thoughtful communication.
- Suspicious links or attachments, often leading to malicious websites or compromising software.
Once identified, report the spam email to the email provider or relevant authorities. Many email providers have built-in features for reporting spam, such as reporting buttons or settings for marking emails as spam. When reporting spam emails, ensure to include any relevant information, such as email headers or contents, which can aid in tracking and identifying the source of spam campaigns.
Reporting Spam Emails to Email Providers
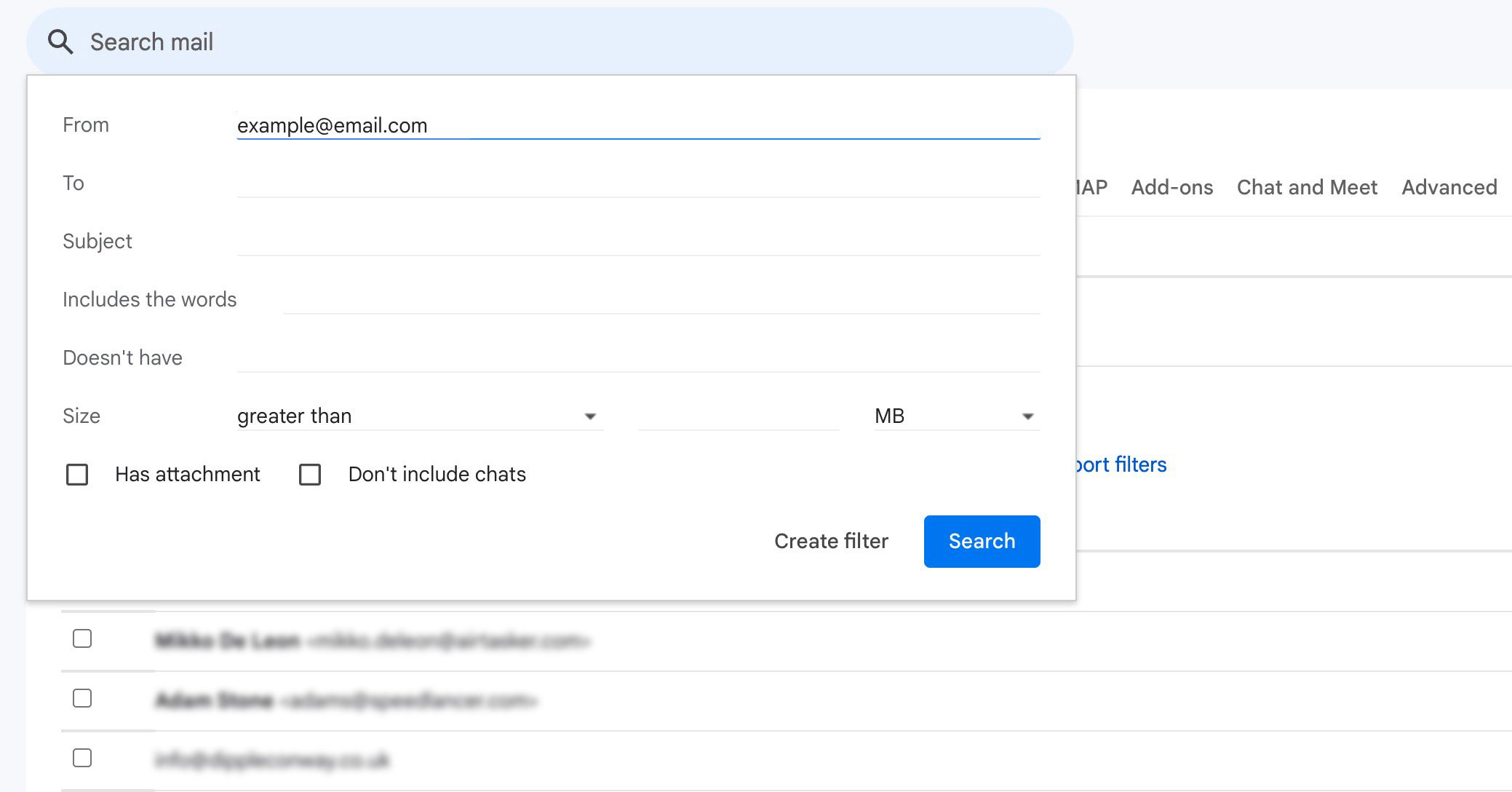
Most email providers, like Gmail, Yahoo Mail, or Outlook, have built-in mechanisms for reporting spam emails. To report spam emails, users can typically follow these steps:
- Open the spam email in question.
- Hover over the email to reveal a “report spam” or similar option.
- Click the “report spam” option to flag the email for review by the email provider’s spam filters.
Additionally, users can also check their email provider’s settings to enable advanced spam filtering features, such as two-factor authentication or custom spam filters.
Reporting Spam Emails to Authorities
In cases where spam emails pose a significant threat or involve illegal activities, such as phishing scams or malware distribution, users can report them to relevant authorities. Here are some options:
- Federal Trade Commission (FTC): The FTC handles complaints about spam emails, phishing scams, and other online threats. Users can file a complaint on the FTC’s website or call 1-877-FTC-HELP.
- Internet Crime Complaint Center (IC3): IC3 is a partnership between the FBI and the National White Collar Crime Center, which handles complaints about cyber crimes, including spam emails. Users can file a complaint on IC3’s website.
- Local Law Enforcement: Users can also report spam emails to local law enforcement agencies, particularly if they believe the spam emails involve illegal activities in their area.
When reporting spam emails to authorities, ensure to provide as much detail as possible, including email headers, contents, and any other relevant information.
Preventing Spam Emails from Affecting Other Users
To prevent spam emails from affecting other users, consider the following best practices:
- Use strong, unique passwords and enable two-factor authentication for all email accounts.
- Regularly update email provider settings to ensure the latest spam filtering features are enabled.
- Report spam emails to both email providers and authorities to help track and identify the source of spam campaigns.
- Stay informed about emerging spam trends and techniques through email provider security bulletins, online security resources, and social media.
By taking these steps, users can contribute to the prevention of spam email propagation and protect themselves, as well as others, from potential threats.
Techniques for Avoiding Phishing and Malware Through Email
Phishing and malware transmission through email have become increasingly common, posing significant risks to individuals and organizations. Phishing involves deceiving users into revealing sensitive information, such as passwords or credit card numbers, while malware can compromise the integrity of a system or steal valuable data. To mitigate these risks, it is essential to adopt safe online practices when receiving emails from unknown sources.
Recognizing Phishing Emails
Phishing emails often appear to be legitimate, but contain subtle indicators that can help identify them as scams. Some common traits of phishing emails include:
- Urgency: Phishing emails often create a sense of urgency, claiming that action must be taken immediately or consequences will follow.
- Suspicious links: Untrustworthy links may lead to malicious websites or download malware.
- Spelling and grammar errors: Legitimate organizations usually maintain high standards of communication, whereas phishing emails often contain grammatical and spelling mistakes.
- Unsolicited emails: Be cautious of emails from unknown senders, especially those claiming to represent a company or organization.
To avoid falling victim to phishing, it is crucial to verify the authenticity of any email before taking action.
Avoiding Malware Through Safe Email Practices
In addition to recognizing phishing emails, there are several steps you can take to avoid malware through safe email practices:
- Never open suspicious attachments: Be cautious of email attachments from unknown senders, especially those with obscure file types or extensions.
- Don’t click on suspicious links: Malicious links can lead to malware downloads or compromised websites.
- Use spam filters: Activate spam filters on your email provider to block unwanted emails and reduce the risk of malware transmission.
- Regularly update your operating system and software: Keeping your system up-to-date can help prevent malware exploits.
By adopting these techniques, you can significantly reduce the risk of phishing and malware transmission through email.
Best Practices for Safe Online Communication
To ensure safe online communication, it is essential to follow these best practices:
- Verify sender information: Before responding to an email or taking action, verify the authenticity of the sender.
- Use strong passwords: Choose unique and complex passwords for all online accounts, and avoid using the same password across multiple sites.
- Keep software up-to-date: Regularly update your operating system, browser, and other software to prevent malware exploits.
- Use two-factor authentication: Enable two-factor authentication to add an extra layer of security to your online accounts.
By following these best practices, you can minimize the risk of phishing and malware transmission through email and maintain a safe online presence.
Conclusion
Phishing and malware transmission through email pose significant risks to individuals and organizations. By recognizing phishing emails and adopting safe online practices, you can reduce the risk of falling victim to these scams. Remember to verify sender information, use strong passwords, keep software up-to-date, and enable two-factor authentication to maintain a safe online presence.
Strategies for Minimizing Email Overload and Organizing Genuine Correspondence
Managing a large volume of email correspondence can be overwhelming, particularly when spam emails dominate the inbox. Effective email management is crucial to maintain productivity, reduce stress, and ensure important messages are not overlooked. This section presents a framework for categorizing and prioritizing legitimate emails, along with examples of email management tools and services that can aid in this process.
Categorization and Prioritization Framework
A well-structured framework enables users to quickly identify and prioritize important emails. The following framework can be implemented:
-
Labeling and Folders
Create distinct labels or folders for different categories of emails, such as work, personal, or social media. This categorization helps in visualizing the email inbox and prioritizing emails accordingly.
-
Flags and Colors
Utilize flags and colors to highlight important emails, reducing the mental effort required to identify priority messages.
-
Priority Levels
Introduce a priority levels system (e.g., high, medium, or low) to indicate the urgency and importance of each email.
Email Management Tools and Services
Several tools and services are available to assist in email management, including:
-
Boomerang for Gmail
Boomerang is an email management tool that enables users to schedule emails to be sent at a later time, set reminders for follow-up emails, and track email open rates. -
Mailstrom
Mailstrom is a web-based email manager that allows users to batch delete, archive, or label emails, reducing the clutter in their inbox. -
Zero Inbox
Zero Inbox is a feature offered by Google Inbox that automatically archives emails based on their priority and frequency of communication with the sender.
Effective email management is essential for maintaining productivity, reducing stress, and ensuring important messages are not overlooked.
Creating and Maintaining a Reliable Spam-Free Email System
Maintaining a secure and trustworthy email system is crucial in the era of growing cybersecurity threats. A spam-free email system not only protects users from malicious content but also enhances the overall email experience by minimizing unwanted emails. To achieve this, it is essential to design a comprehensive plan for managing email security.
Email Security Best Practices
Implementing robust security measures is vital to prevent email-based threats. The following best practices can be adopted to maintain a secure email system:
- Regularly update email client and server software to ensure the installation of the latest security patches and features.
- Use strong, unique passwords and enable two-factor authentication (2FA) to prevent unauthorized access to email accounts.
- Implement email authentication protocols such as Domain-based Message Authentication, Reporting and Conformance (DMARC), Sender Policy Framework (SPF), and Sender ID to prevent email spoofing.
- Use antivirus software and email scanners to detect and remove malicious attachments and links.
Email Filtering and Blocking
Effective email filtering and blocking mechanisms are essential to prevent spam and malicious emails from reaching users. The following techniques can be employed to maintain a spam-free email system:
- Implement content filters to block emails containing specific s or phrases that are commonly used in spam messages.
- Use reputation-based filtering to block emails from known spam sources and email addresses with poor reputations.
- Implement sender-based filtering to block emails from specific senders, such as those with known phishing domains or IP addresses.
- Use behavioral-based filtering to block emails that exhibit suspicious behavior, such as emails with multiple attachments or unusual sender behavior.
Email Encryption and Secure Communication
Encrypting email communication is crucial to protect sensitive information transmitted via email. The following measures can be taken to ensure secure email communication:
- Implement email encryption protocols such as Secure/Multipurpose Internet Mail Extensions (S/MIME) and Pretty Good Privacy (PGP) to encrypt email messages.
- Use secure communication protocols such as Transport Layer Security (TLS) and Secure Sockets Layer (SSL) to encrypt email communication.
- Enable end-to-end encryption to ensure that only the sender and recipient can read the encrypted email content.
Email Archiving and Backup
Maintaining email archives and backups is essential to ensure business continuity and compliance with regulatory requirements. The following measures can be taken to maintain email archives and backups:
- Implement email archiving systems to store and manage email records over a period of time.
- Regularly backup email data to prevent loss or corruption in case of system failures or security breaches.
- Store email archives and backups on secure and protected storage devices to prevent unauthorized access.
Last Word
In conclusion, stopping spam emails requires a multi-faceted approach that involves understanding the nature of these unwanted messages, identifying and reporting them, and utilizing effective email management tools and strategies. By following the steps Artikeld in this guide, you will be able to save your inbox from the scourge of spam and maintain a secure and trustworthy email system.
Remember, taking action against spam emails is a collective effort. By working together, we can create a spam-free email environment that benefits everyone.
Helpful Answers
Q: What is the most effective way to stop spam emails?
A: Regularly updating your email provider’s spam filters and reporting suspicious emails is key to reducing spam.
Q: Can spam emails be identified by their subject line?
A: While some spam emails can be identified by their subject line, many use legitimate-sounding subjects to trick recipients into opening them.
Q: How do I prevent phishing emails from getting into my inbox?
A: Be cautious of emails that ask for sensitive information or contain suspicious links and attachments, and never click on suspicious links or download attachments from unknown sources.
Q: Can email service providers filter out all spam emails?
A: While email service providers have improved their spam filtering capabilities, no filter is 100% effective, and humans must report suspicious emails to help improve the filtering process.
Q: What are some common email management tools that can help prevent spam?
A: Tools such as email filters, blacklists, and whitelists can help identify and block spam emails, while email management software can help manage and prioritize legitimate emails.
Q: How can I report spam emails to email providers and authorities?
A: Most email service providers have built-in reporting tools, and you can also report spam emails to the Federal Trade Commission (FTC) or other relevant authorities.